Browsing the "Proxy" Category

Published on April 23rd, 2024 | by admin
iSpeech Apr 23, 2024NewsroomEnd-to-End Encryption / Privacy European Police Chiefs said that the complementary partnership between law enforcement agencies and the technology industry is at risk due to end-to-end encryption (E2EE). They called on the industry... Read More →

Published on April 23rd, 2024 | by admin
iSpeech Cybersecurity breaches can be devastating for both individuals and businesses alike. While many people tend to focus on understanding how and why they were targeted by such breaches, there's a larger, more pressing question: What... Read More →

Published on April 23rd, 2024 | by admin
iSpeech Apr 23, 2024NewsroomSpyware / Cyber Espionage The U.S. Department of State on Monday said it's taking steps to impose visa restrictions on 13 individuals who are allegedly involved in the development and sale of commercial... Read More →

Published on April 23rd, 2024 | by admin
iSpeech.org Apr 23, 2024NewsroomNational Security Agency / Threat Intelligence The Russia-linked nation-state threat actor tracked as APT28 weaponized a security flaw in the Microsoft Windows Print Spooler component to deliver a previously unknown custom malware called... Read More →
Published on April 22nd, 2024 | by admin
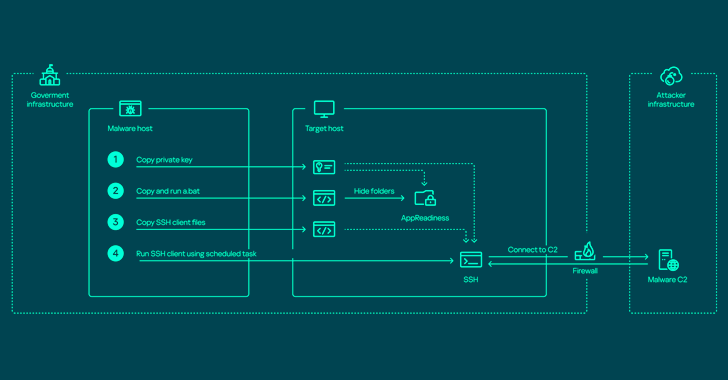
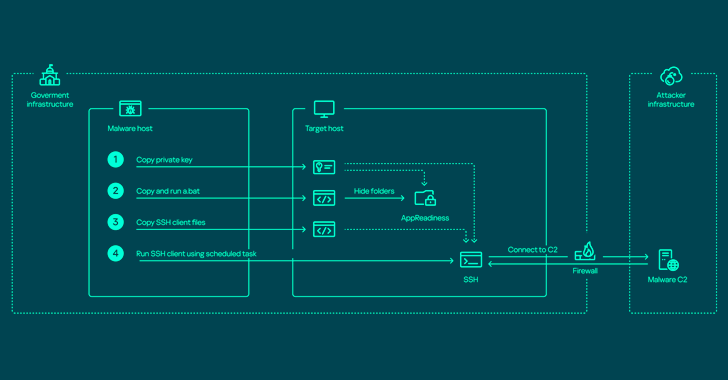
https://www.ispeech.org Apr 22, 2024NewsroomNetwork Security / Endpoint Security The threat actor known as ToddyCat has been observed using a wide range of tools to retain access to compromised environments and steal valuable data. Russian cybersecurity firm... Read More →

Published on April 22nd, 2024 | by admin
iSpeech.org Selecting the best computer for your business can be a straightforward process if you plan ahead. Check out these factors to make the most of your purchase. Pro Tip: Bargain prices should not be the... Read More →

Published on April 22nd, 2024 | by admin
iSpeech.org Over the past two years, a shocking 51% of organizations surveyed in a leading industry report have been compromised by a cyberattack. Yes, over half. And this, in a world where enterprises deploy an average... Read More →

Published on April 22nd, 2024 | by admin
iSpeech Between crossovers - Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have experienced a Cyber Extortion / Ransomware attack, we noticed that some victims re-occur. Consequently, the... Read More →

Published on April 22nd, 2024 | by admin
iSpeech Apr 22, 2024NewsroomRootkit / Software Security New research has found that the DOS-to-NT path conversion process could be exploited by threat actors to achieve rootkit-like capabilities to conceal and impersonate files, directories, and processes. "When... Read More →

Published on April 22nd, 2024 | by admin
iSpeech.org Apr 22, 2024NewsroomCryptocurrency / Artificial Intelligence Microsoft has revealed that North Korea-linked state-sponsored cyber actors has begun to use artificial intelligence (AI) to make its operations more effective and efficient. "They are learning to use... Read More →

Published on April 21st, 2024 | by admin
Free Text to Speech A new information stealer has been found leveraging Lua bytecode for added stealth and sophistication, findings from McAfee Labs reveal. The cybersecurity firm has assessed it to be a variant of a... Read More →
Published on April 20th, 2024 | by admin
iSpeech Apr 20, 2024NewsroomVulnerability / Network Security Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS that has come under active exploitation in the wild by malicious actors. The company described... Read More →
Published on April 20th, 2024 | by admin
https://www.ispeech.org Apr 20, 2024NewsroomVulnerability / Network Security Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS that has come under active exploitation in the wild by malicious actors. The company described... Read More →
Published on April 20th, 2024 | by admin
Text to Speech Apr 20, 2024NewsroomVulnerability / Network Security Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS that has come under active exploitation in the wild by malicious actors. The... Read More →

















Gloss