Browsing the "Proxy" Category

Published on April 12th, 2024 | by admin
Text to Speech Apr 12, 2024NewsroomWeb Security / WordPress Cybersecurity researchers have discovered a credit card skimmer that's concealed within a fake Meta Pixel tracker script in an attempt to evade detection. Sucuri said that the... Read More →

Published on April 12th, 2024 | by admin
iSpeech Apr 12, 2024NewsroomCyber Attack / Data Breach The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday issued an emergency directive (ED 24-02) urging federal agencies to hunt for signs of compromise and enact preventive... Read More →

Published on April 11th, 2024 | by admin
iSpeech Canine Companions, a service dog company, will announce new technology this week that enables trained canines to perform tasks, such as tamping down anxiety and interrupting nightmares, after receiving wireless alerts. Called CanineAlert, the technology... Read More →

Published on April 11th, 2024 | by admin
iSpeech.org Apr 11, 2024NewsroomEndpoint Security / Ransomware A threat actor tracked as TA547 has targeted dozens of German organizations with an information stealer called Rhadamanthys as part of an invoice-themed phishing campaign. "This is the first... Read More →

Published on April 11th, 2024 | by admin
iSpeech.org Apr 11, 2024NewsroomSpyware / Cyber Espionage Apple on Wednesday revised its documentation pertaining to its mercenary spyware threat notification system to mention that it alerts users when they may have been individually targeted by such... Read More →

Published on April 11th, 2024 | by admin
https://www.ispeech.org Apr 11, 2024NewsroomVulnerability / Threat Mitigation Fortinet has released patches to address a critical security flaw impacting FortiClientLinux that could be exploited to achieve arbitrary code execution. Tracked as CVE-2023-45590, the vulnerability carries a CVSS... Read More →

Published on April 10th, 2024 | by admin
Powered by iSpeech Apr 10, 2024NewsroomMobile Security / Spyware An active Android malware campaign dubbed eXotic Visit has been primarily targeting users in South Asia, particularly those in India and Pakistan, with malware distributed via dedicated... Read More →

Published on April 10th, 2024 | by admin
Powered by iSpeech Apr 10, 2024NewsroomCyber Crime / Malvertising Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March 2024. "Historically, Raspberry Robin was... Read More →

Published on April 10th, 2024 | by admin
Text to Speech The long-standing promise of 3D printing to simplify and enhance our lives is now evolving from concept to reality. From dental aligners to jet engine fuel nozzles and houses to sports shoes, 3D... Read More →

Published on April 10th, 2024 | by admin
iSpeech.org Apr 10, 2024NewsroomSoftware Security / Supply Chain Attack Threat actors are now taking advantage of GitHub's search functionality to trick unsuspecting users looking for popular repositories into downloading spurious counterparts that serve malware. The latest... Read More →
Published on April 10th, 2024 | by admin
tts The browser is part of a bigger project to keep internet browsing anonymous: Use Tor and you use the Tor Project network, a complex, encrypted relay system managed by the Tor community, making it much... Read More →
Published on April 10th, 2024 | by admin
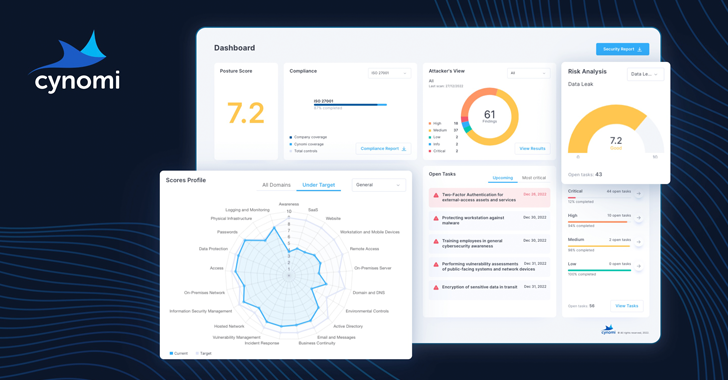
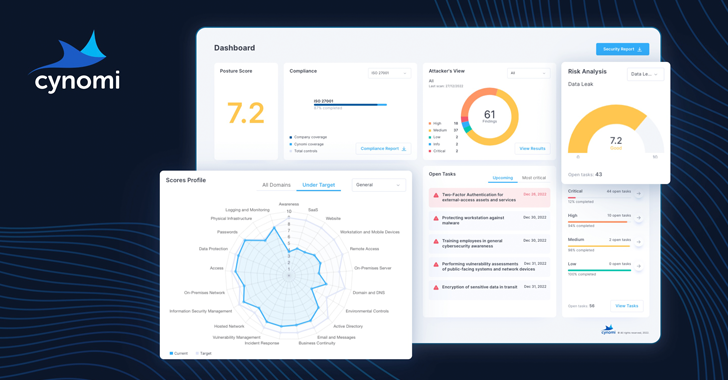
Convert Text to Speech The need for vCISO services is growing. SMBs and SMEs are dealing with more third-party risks, tightening regulatory demands and stringent cyber insurance requirements than ever before. However, they often lack the... Read More →

Published on April 10th, 2024 | by admin
https://www.ispeech.org Apr 10, 2024NewsroomHardware Security / Linux Cybersecurity researchers have disclosed what they say is the "first native Spectre v2 exploit" against the Linux kernel on Intel systems that could be exploited to read sensitive data... Read More →

Published on April 10th, 2024 | by admin
iSpeech Apr 10, 2024The Hacker NewsWebinar / Identity Security We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity Threat Exposures (ITEs) are like... Read More →


















Gloss