
Daily Archives: February 15, 2018
Splunk for Security Investigation: Ransomware
February 15th, 2018 | 🕒
iSpeech Welcome to the Splunk for Security Investigation Experience. In this fourth video, learn how you can harness the power
Eoin Keary, CEO of edgescan, talks with ITSPmagazine about security and risk management within a CDCI-enabled DevSecOps process
February 15th, 2018 | 🕒
Speech Synthesis Eoin Keary, CEO of Dublin-based edgescan, talks to ITSPmagazine about his entry into cybersecurity, starting off in software
H4cks CCTV Cameras – Kali Linux
February 15th, 2018 | 🕒
iSpeech.org How to h4cks CCTV Cameras using Kali Linux 2018 + IP Scanner ( IPSCAN ) + Android Phone ---------------------------------------------------------------------------------------------------------------------------------------------------------------
How GRC planning protects your company’s brand against the next threat cyberattack
February 15th, 2018 | 🕒
https://www.ispeech.org We only need to look at Equifax, Sony, and other notable corporate crises to understand the challenge of managing
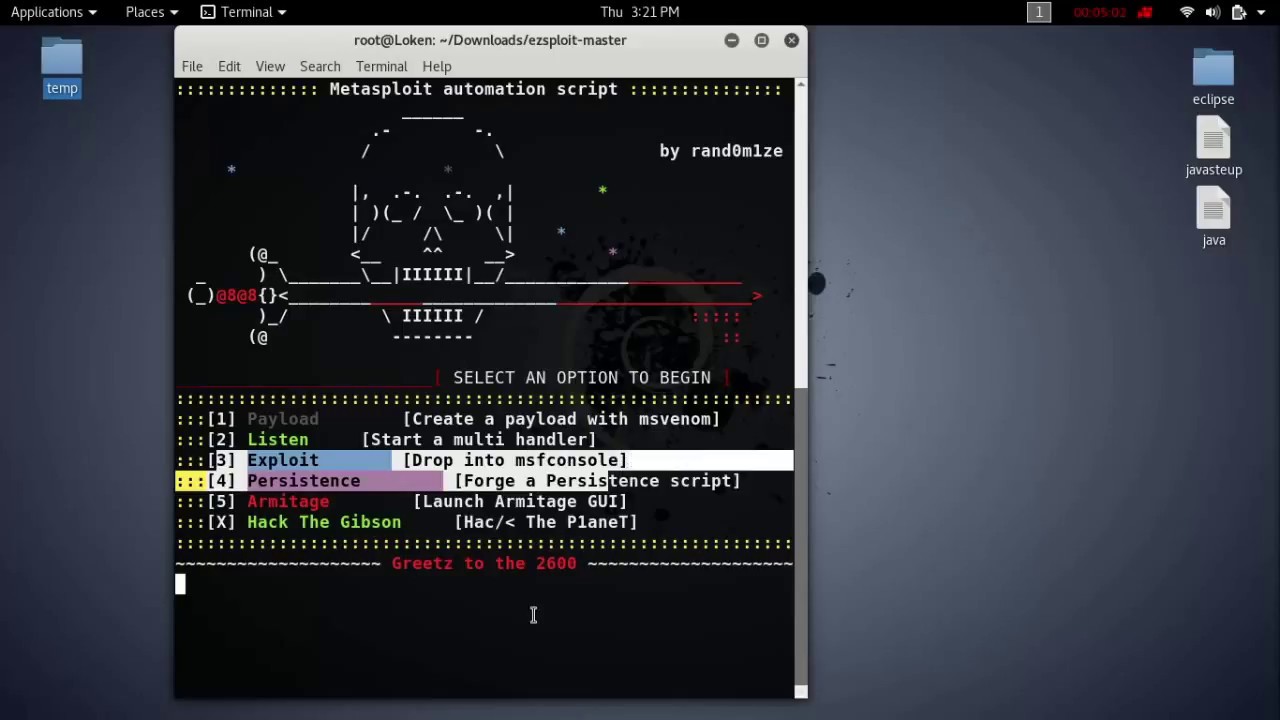
Exploit Android Over Local Network.. #Pentesting
February 15th, 2018 | 🕒
Text to Speech Demo Hack any Android Device on the Internet using Kali Linux! A complete step by step tutorial
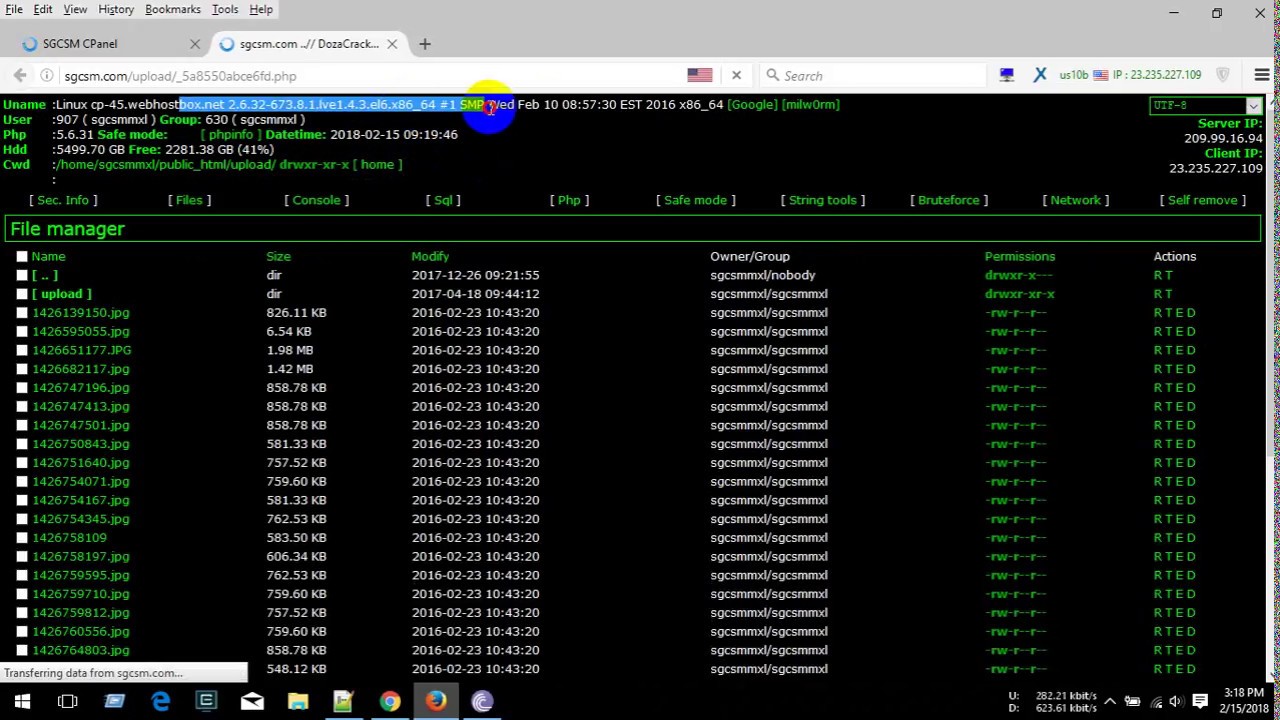
Sql Injection and WAF bypass with shell upload 2018
February 15th, 2018 | 🕒
iSpeech.org Hackbar Pro : https://mega.nz/#!g8lhQayK!wyMe-YWsDai3Zbe2X_zXKTtBLBuPrcfx_7u93vWvFy8 More hacking php script : https://pastebin.com/u/HaxorScripts 2018-02-15 11:01:36 source
The ALT Guide To Character Design
February 15th, 2018 | 🕒
iSpeech The Alt Guide to Character Design is a subversive initiation into the art of character design principles, as told
Economy Today: Discussion on Cyber Security | 15/2/2018
February 15th, 2018 | 🕒
iSpeech.org Economy Today: Discussion on Cyber Security | 15/2/2018 .............................................................................................. ‘DD News’ is the News Channel of India's Public Service
How to lock computer Software | Lock Program | Secure Software | File | Folder
February 15th, 2018 | 🕒
Free Text to Speech How to lock computer software Live Example in Hindi, It is a small software to secure
Whapa – WhatsApp DataBase Parser Tool
February 15th, 2018 | 🕒
iSpeech.orgWhapa is a whatsapp database parser that automates the process. The main purpose of whapa is to present the data handled by
BitGrail cryptocurrency exchange has been hacked – More than $160 million stolen in Nano
February 15th, 2018 | 🕒
https://www.ispeech.orgThe Italian cryptocurrency exchange BitGrail announced late last week that it was hacked and lost about 17 million Nano cryptocurrency














Gloss