February 2nd, 2018 | 🕒
https://www.ispeech.org Crescono le minacce informatiche, con particolare riguardo al ransomware, i virus informatici che tentano di cifrare i dati all’interno
February 2nd, 2018 | 🕒
iSpeech Sharp MFPs feature an intelligent network interface that can limit access to specific computers on a network, and selectively
February 2nd, 2018 | 🕒
https://www.ispeech.org/text.to.speech REMIX / METAL / INDUSTRY / DUBSTEP What happens when you give ZARDONIC full access to the stems to
February 2nd, 2018 | 🕒
iSpeechEAPHammer is a toolkit for performing targeted evil twin attacks against WPA2-Enterprise networks. It is designed to be used in full
February 2nd, 2018 | 🕒
iSpeech Between malware, botnets, viruses, worms, ransomware and DDoS attacks, it may seem impossible to protect yourself online. The trick
February 2nd, 2018 | 🕒
iSpeech 2018-02-02 05:43:36 source
February 2nd, 2018 | 🕒
https://www.ispeech.org Likes: 1 Viewed: source
February 2nd, 2018 | 🕒
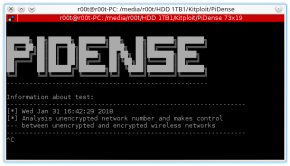
french ttsMonitor illegal wireless network activities. Similar SSID broadcasts Same SSID broadcasts Calculates unencrypted wireless networks density Watches SSID broadcasts at
February 2nd, 2018 | 🕒
iSpeech.org Malware Exploiting Spectre, Meltdown Flaws Emerges Researchers at the antivirus testing firm AV-TEST have discovered more than 130 samples
February 2nd, 2018 | 🕒
iSpeech Welcome to #TechnicalWaqas. Top 3 Best WiFi Hacking App 2018 | You Never known | Technical Waqas |10000 ℅
February 2nd, 2018 | 🕒
iSpeech.org This video is all about.. best website to learn hacking. website to download hacking tools. best hacking books PDF

















Gloss