March 11th, 2019 | 🕒
https://www.ispeech.org/text.to.speech Ariel Garten is Founder of InteraXon, makers of Muse: the brain sensing headband that makes meditation easier by sensing
March 6th, 2019 | 🕒
Text to Speech Voices James Lyne, Director of Research, SANS Institute Stephen Sims, Security Researcher, SANS Institute Historically, penetration testers
February 13th, 2019 | 🕒
iSpeech.org Simulation of a cyberattack on a robotic arm, experiment performed on a robotic arm. Forcing it to erroneously perform
February 5th, 2019 | 🕒
iSpeech Network hacking attacks: MWR Infosecurity Principal Security Consultant Donato Capitella shows how it is done source
November 29th, 2018 | 🕒
iSpeech SISA is organizing mini-events across regions showcasing Live Simulations of Payment Data Breaches. These events are CXO, CTO, and
April 4th, 2018 | 🕒
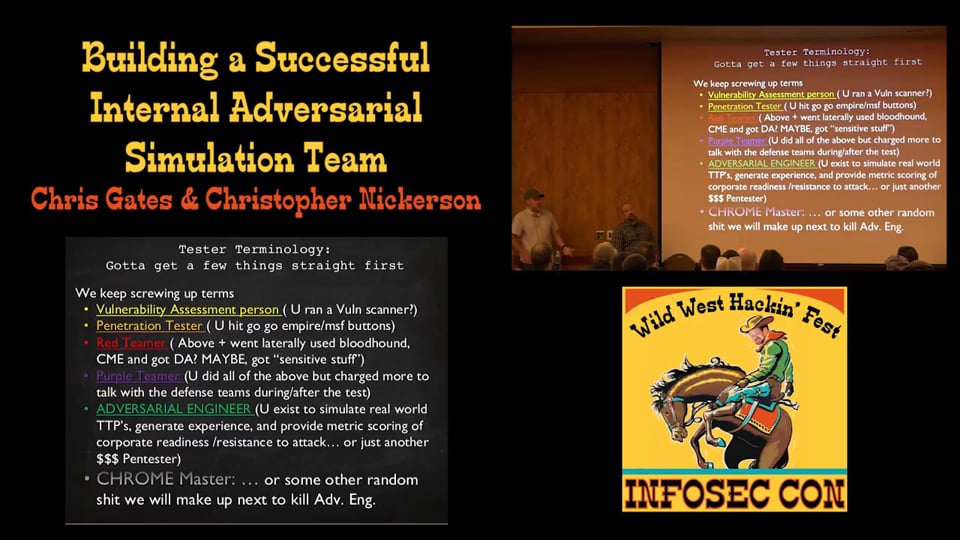
Powered by iSpeech Wild West Hackin' Fest 2017 The evolution chain in security testing is fundamentally broken due to a
September 29th, 2017 | 🕒
https://www.ispeech.org This video is part of the Angular Security MasterClass - Web Security Fundamentals Course - https://angular-university.io/course/angular-security-course In this video
October 29th, 2015 | 🕒
Powered by iSpeech This demo employs the latest Pulldownit 3.5 plugin and showcases its capabilities in dynamics solving and fracture
November 14th, 2014 | 🕒
Text to Speech 2nd Year Visual Effects & Motion Graphics Project. This was my first project back in the second
July 17th, 2014 | 🕒
iSpeech FakeNet is a Windows Network Simulation Tool that aids in the dynamic analysis of malicious software. The tool simulates
October 22nd, 2013 | 🕒
iSpeech.org Jump at - 4:25 - to see nuclear warfare! Nuclear War Simulation by "Defcon"! Game is set up to
June 14th, 2011 | 🕒
https://www.ispeech.org Alexei Kachalin explains how to simulate large-scale networks under attack. This talk was held at DeepSec 2009. Likes: 0
January 10th, 2011 | 🕒
iSpeech DEFCON is an awesome PC, Mac, and Linux (yes, Linux!) game made by Introversion Software. In this game, I
August 7th, 2009 | 🕒
iSpeech When a rogue terrorist group begins to hack into country's computer systems, chaos ensues. Will the United Nations Security



















Gloss