July 17th, 2011 | 🕒
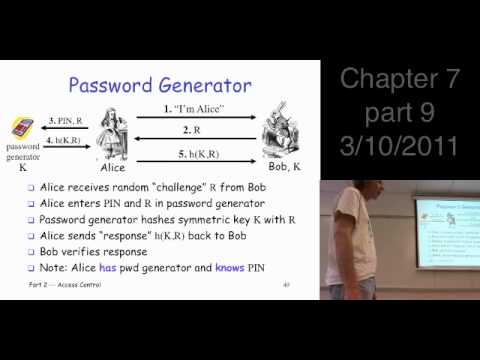
https://www.ispeech.org/text.to.speech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.5-7.7 password generator, 2-factor authentication,
July 17th, 2011 | 🕒
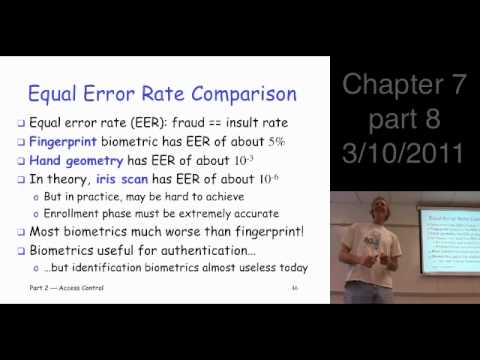
https://www.ispeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.4.3-7.4.4 biometrics, equal error rate
July 17th, 2011 | 🕒
iSpeech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Section 7.4.2 biometrics, iris scan Class
July 17th, 2011 | 🕒
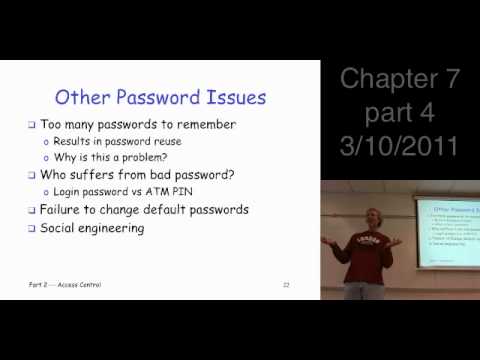
https://www.ispeech.org/text.to.speech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.3.6 other password issues Class
July 17th, 2011 | 🕒
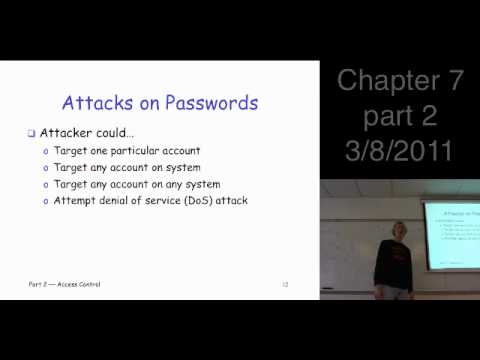
iSpeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.3.2,7.3.4 passwords Class Lecture, 2011
July 17th, 2011 | 🕒
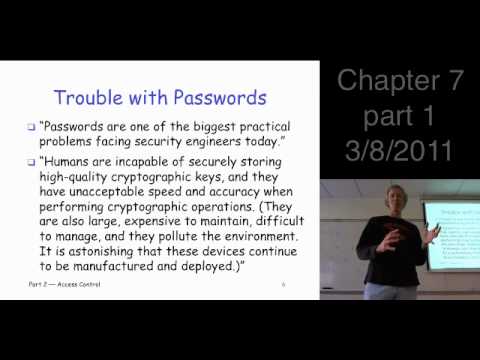
https://www.ispeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.1-7.3.1 access control, authentication, passwords
July 17th, 2011 | 🕒
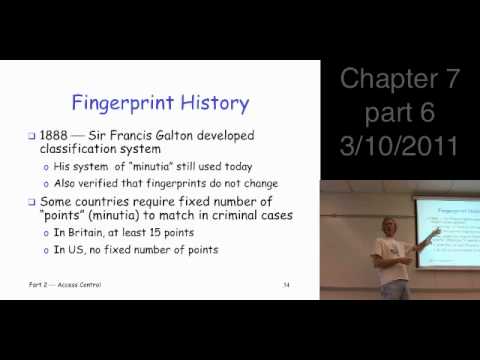
iSpeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.4.1-7.4.2 biometrics, fingerprints, hand geometry
July 17th, 2011 | 🕒
https://www.ispeech.org/text.to.speech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.4 biometrics Class Lecture, 2011
July 17th, 2011 | 🕒
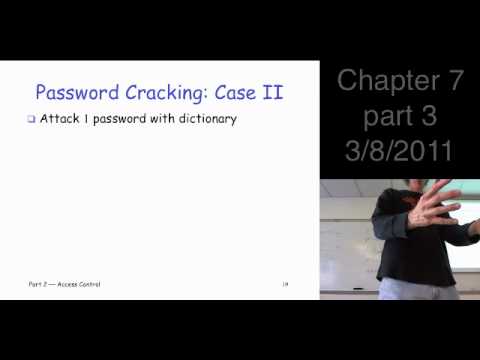
https://www.ispeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 7: Authentication Sections 7.3.4-7.3.5 password cracking Class Lecture,
July 17th, 2011 | 🕒
iSpeech.org Sharon Coneady talks about social engineering: „Social engineering is hitting the headlines more than ever. As computer security becomes
July 17th, 2011 | 🕒
iSpeech Toralv Dirro gives an overview about the state of malware: „Malware is still on the rise, numbers are growing,
July 17th, 2011 | 🕒
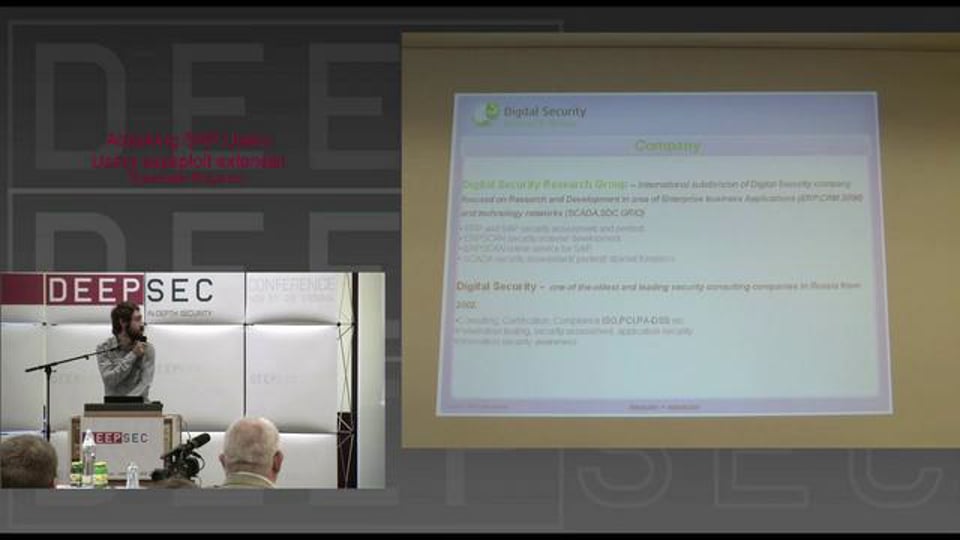
Powered by iSpeech Alexander Polyakov explains how to attack SAP with sapsploit: „Business applications like ERP, CRM, SRM and others
July 17th, 2011 | 🕒
Text to Speech Voices Mitja Kolsek talks about an overlooked security issue: „The binary planting vulnerability, although documented for over
July 17th, 2011 | 🕒
iSpeech.org Ron Bowes talks about password security: „Recent years have been a golden age for password research; between breaches of













Gloss