December 29th, 2023 | 🕒
iSpeech Dec 29, 2023NewsroomMalware / Cyber Threat Nation-state actors affiliated to North Korea have been observed using spear-phishing attacks to
February 23rd, 2023 | 🕒
iSpeech One of my Labs colleagues recently published an article on the Coalfire Blog about executing an obfuscated PowerShell payload
February 14th, 2023 | 🕒
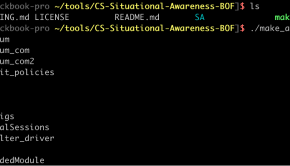
iSpeech.org 1.1 Introduction Recently, myself and a few friends decided to port my coworker Kevin Haubris‘ COFFLoader project to Metasploit.
February 13th, 2023 | 🕒
iSpeech I am a big fan of using meterpreter as a post compromise payload. It has so many tools that
March 25th, 2020 | 🕒
Powered by iSpeech Ganar acceso con kali linux en una maquina corriendo win7 con una aplicacion vulnerable: Rejetto HTTP File
March 20th, 2020 | 🕒
iSpeech.org For those who are starting in the cyber security area, the Hack The Box is an online platform that
March 11th, 2020 | 🕒
iSpeech.org For those who are starting in the cyber security area, the Hack The Box is an online platform that
February 6th, 2020 | 🕒
iSpeech Installing Kali Linux 2020 on VirtualBox so that you can start using the latest operating system from Offensive Security
January 24th, 2020 | 🕒
iSpeech.org Every web and mobile application are connected to a database to house critical data. Hackers ultimate goal is to
December 29th, 2019 | 🕒
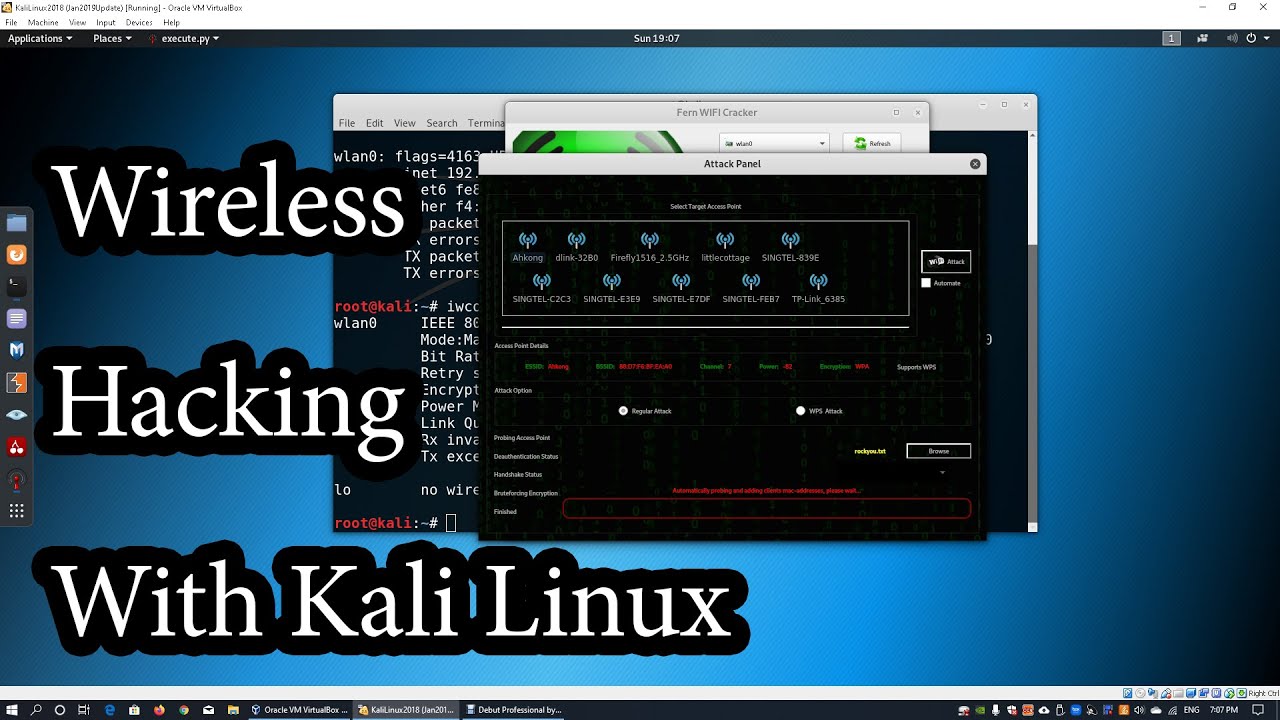
TTS Demo Fern wireless cracker on Kali Linux to break into access points. Video is strictly for educational purposes. Ethical
November 9th, 2019 | 🕒
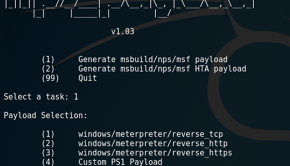
Text to Speech Demo In this video I show you how to hack windows 10 by bypassing windows defender using
November 4th, 2019 | 🕒
TTS video, sharing, camera phone, video phone, free, upload 2019-11-04 07:44:12 source
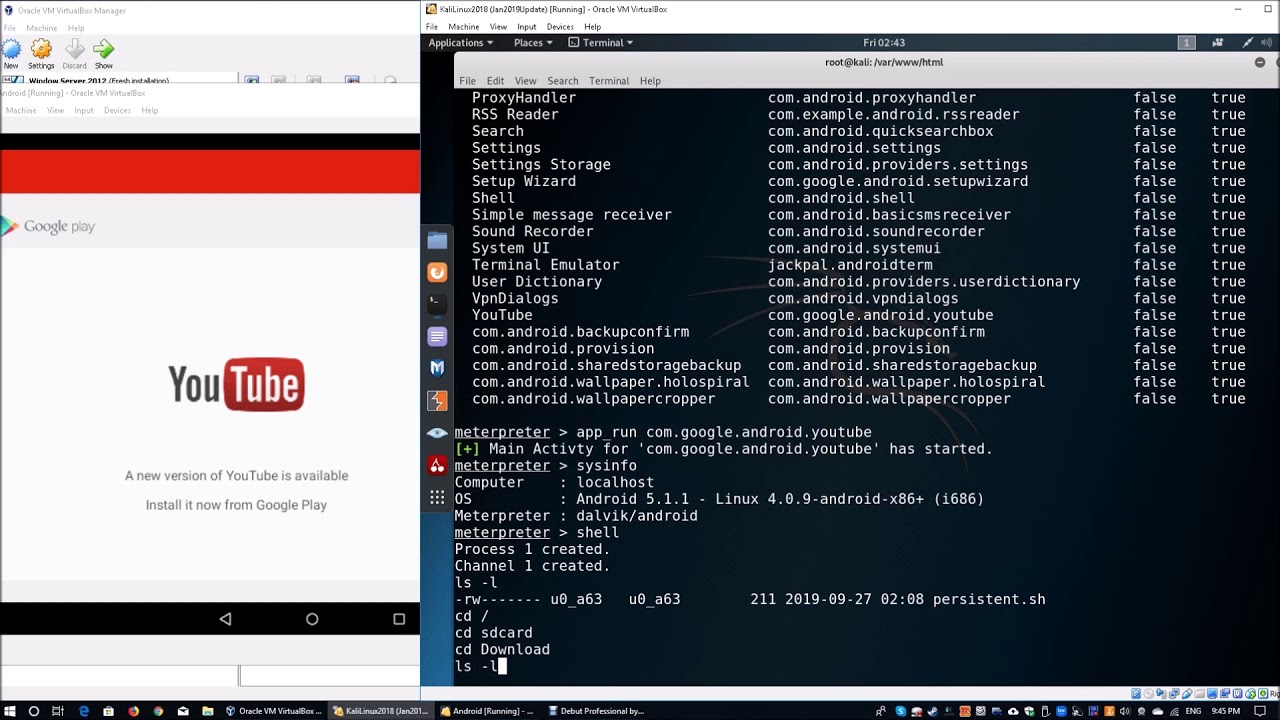
September 27th, 2019 | 🕒
https://www.ispeech.org/text.to.speech Android debugger to maintain access as part of post exploitation. Video is strictly for education purposes. Ethical Hacker |
September 22nd, 2019 | 🕒
TTS En este video vamos a acceder a un equipo que tiene una aplicación vulnerable corriendo en el puerto 80,
















Gloss