January 18th, 2019 | 🕒
https://www.ispeech.orgSnyk helps you find, fix and monitor known vulnerabilities in Node.js npm, Ruby and Java dependencies, both on an ad hoc basis and as part of
January 15th, 2019 | 🕒
https://www.ispeech.org In Parliament on Tuesday (Jan 15), Minister for Communications and Information S Iswaran delivered a ministerial statement on the
June 21st, 2018 | 🕒
Text to Speech DemoNSABlocklist © project originally created under the MIT license 2015-2018 by CHEF-KOCH. Description This isn’t yet another hosts file or DNSBL that
February 2nd, 2018 | 🕒
iSpeech Welcome to #TechnicalWaqas. Top 3 Best WiFi Hacking App 2018 | You Never known | Technical Waqas |10000 ℅
September 13th, 2017 | 🕒
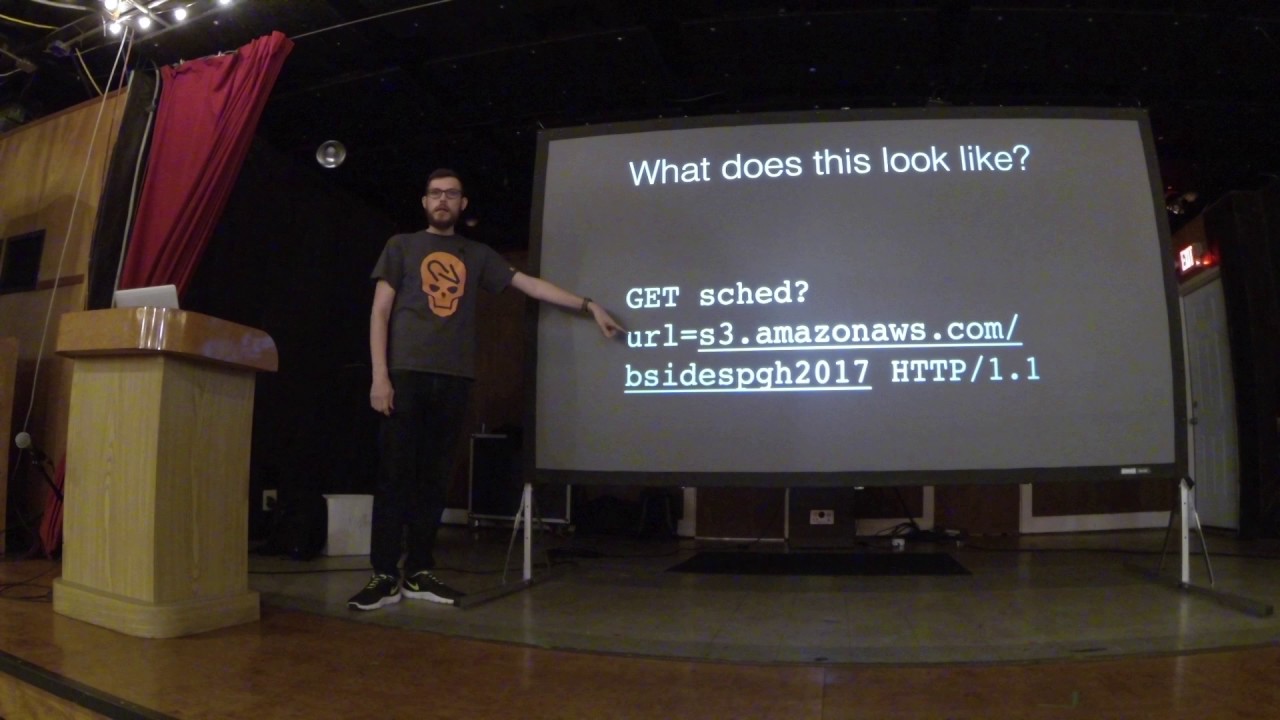
Text to Speech OWASP Top 10 explained: Watch our Proof of Concept video to find out how attackers can exploit
June 16th, 2017 | 🕒
iSpeech.org Lesser-known Application Vulnerabilities - Which are Costing Companies $$$$ - Kevin Cody Vulnerabilities are expensive, there’s simply no way
April 17th, 2017 | 🕒
iSpeech.org 2017-04-17 02:55:47 source
August 22nd, 2016 | 🕒
iSpeech This video is part of a larger product developed by nVisium to test students in a real application on
June 18th, 2014 | 🕒
https://www.ispeech.org core feature of XML is the ability to define and validate document structure using schemas and document type lead
November 20th, 2013 | 🕒
iSpeech Welcome to a demo of one of Infrared Security's Computer Based Training (CBT) offerings. Infrared Security's CBTs are built
September 12th, 2012 | 🕒
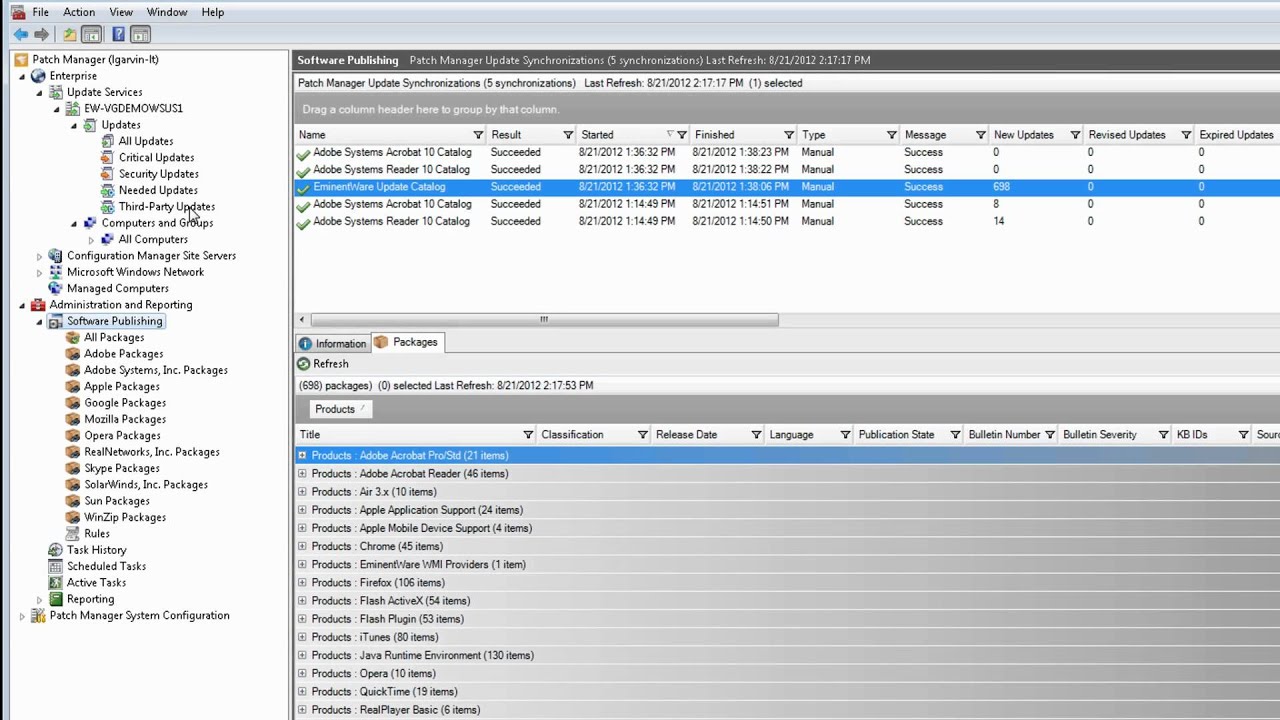
Text to Speech Voices Learn more: http://bit.ly/patch_compliance_reporting In this short video WSUS MVP, Lawrence Garvin, will demo how you can














Gloss