January 5th, 2022 | 🕒
https://www.ispeech.org When businesses suspect that they may have experienced a cyber incident, their first call is typically not to a
March 3rd, 2020 | 🕒
https://www.ispeech.org/text.to.speech Part 1 of this article reviewed overlooked information technology (IT) and intellectual property (IP) provisions in bank vendor agreements.
October 17th, 2019 | 🕒
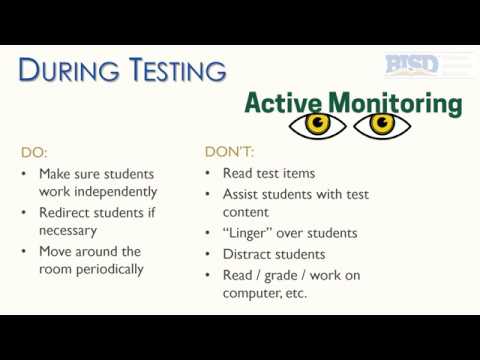
iSpeech.org Designed for teachers who will administer Interim Assessments in 2019-20. Covers basic issues of security and confidentiality specific to
September 17th, 2019 | 🕒
iSpeech Using the CERN e-mail service gives you some flexibility. Maybe a bit too much, as some current practices are
May 23rd, 2019 | 🕒
https://www.ispeech.org There are three key pillars of security that every device needs to use to ensure that they are secure.
May 20th, 2019 | 🕒
iSpeech.org The CIA Triad is a model that represents the three core principles of information security - Confidentiality, Integrity &
May 18th, 2019 | 🕒
Text to Speech Confidentiality is one of the key rights of a patient. This video illustrates how confidentiality can be
March 26th, 2019 | 🕒
TTS Demo Confusion and ambiguity in how U.S. patients and researchers perceive genetic privacy is uncovered by a study published
February 21st, 2019 | 🕒
japanese text to speech 📚📚📚📚📚📚📚📚 GOOD NEWS FOR COMPUTER ENGINEERS INTRODUCING 5 MINUTES ENGINEERING 🎓🎓🎓🎓🎓🎓🎓🎓 SUBJECT :- Discrete Mathematics (DM)
January 2nd, 2019 | 🕒
chinese text to speech Hart Montgomery, Fujitsu Laboratories of America Achieving strong privacy and confidentiality on a blockchain can be
October 13th, 2018 | 🕒
Text to Speech #NetworkSecurity #CCNA #MCSA #EthicalHacking #infotechshesh About This Video :- Friends i this video i explained What IS
October 11th, 2016 | 🕒
https://www.ispeech.org Basic high level overview on ITIL Information Security Management. 2016-10-11 12:39:38 source


















Gloss