The Chinese threat actor known as APT31 (aka Bronze Vinewood, Judgement Panda, or Violet Typhoon) has been linked to a set of advanced backdoors that are capable of exfiltrating harvested sensitive information to Dropbox.
The malware is part of a broader collection of more than 15 implants that have been put to use by the adversary in attacks targeting industrial organizations in Eastern Europe in 2022.
"The attackers aimed to establish a permanent channel for data exfiltration, including data stored on air-gapped systems," Kaspersky said in an analysis spotlighting APT31's previously undocumented tradecraft.

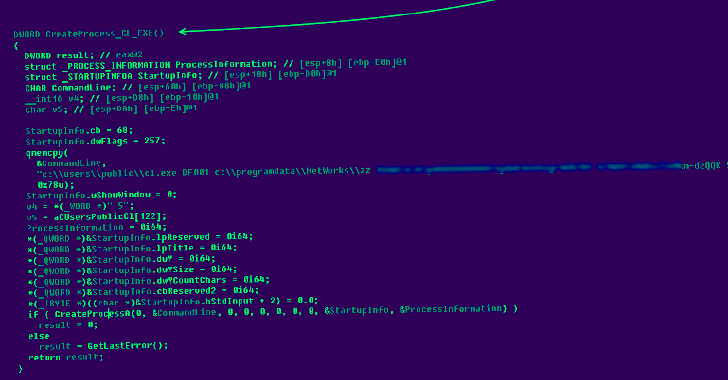
The intrusions employ a three-stage malware stack, each focused on disparate aspects of the attack chain: setting up persistence, gathering sensitive data, and transmitting the information to a remote server under the attackers' control.
Some variants of the second-stage backdoors also come with features designed to look up file names in the Microsoft Outlook folder, execute remote commands, and employ the third-step component to complete the data exfiltration step in the form of RAR archive files.
"The first step is used for persistence, the deployment and startup of the second-step malware module, which is responsible for uploading the files collected to the server by calling the third-step implant and cleaning up," the Russian cybersecurity firm said.
In what's a novel twist, APT31 is said to have used a command-and-control (C2) inside the corporate perimeter and leveraged it as a proxy to siphon data from systems that lacked direct access to the internet, indicating clear attempts to single out air-gapped hosts.

Kaspersky said it also spotted additional tools used by the attacker to manually upload the data to Yandex Disk and other temporary file-sharing services such as extraimage, imgbb, imgshare, schollz, and zippyimage, among others. A third similar implant is configured to send the data via the Yandex email service.
The findings highlight the meticulous planning and the ability of the threat actor to adapt and spin up new capabilities in their cyber espionage pursuits.
"Abusing popular cloud-based data storages may allow the threat actor(s) to evade security measures," the company said. "At the same time, it opens up the possibility for stolen data to be leaked a second time in the event that a third party gets access to a storage used by the threat actor(s)."








Gloss