new InfoStealer Malware delivered by eMail to many International Companies
I made this quick introduction because the following analysis would probably take the reader to think about specific attribution, but it won’t be so accurate, so please be prepared to have not such a clear conclusions.
Today I’d like to show an interesting analysis of a quite new InfoStealer Malware delivered by eMail to many International Companies. The analysis shows up interesting Code Reuse capabilities, apparently originated by Japanese Attackers reusing an English Speaker Attacker source code. Again I have not enough artifacts to give attributions but only few clues as follows. In the described analysis, the original sample was delivered by sarah@labaire.co.za (with high probability a compromised South Africa account) to one of my spamming email addresses.
 |
| Stage 1: Invoked Command |
A fashionable powershell command drops and executes: hxxp://ssrdevelopments.co.za/a2/off.exe. Powershell seems to be a “must have” in contemporary Malware. Analyzing the “dropping” url and tracking down the time it is in “Index Of” mode (2017-0-13), I suspect it is not a compromised website rather a crafted web server or a compromised host of a dead company.
 |
| Dropping Web Site |
By surfing the Malware propagator website I founded out many malicious executables (sees IoC section) each one showing up specific behaviors such as: password stealers, RAT, and Banking Trojans. Even if the samples were developed for different targets, all of them shared the following basic behaviors:
- Check for victims IP address before getting into Malicious activities (maybe related to targeted activities)
- Install itself into auto execution path
- Tries to fingerprint the target system (such as CPU, HD, Memory, Username, System, etc..)
- Sniff for Keystrokes
[adsense size='1' ]
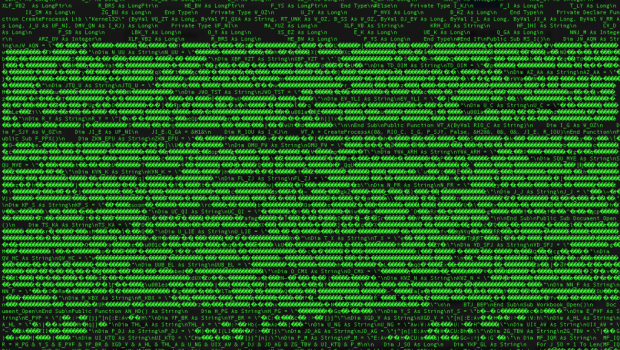
I’d like to write a simple analysis for each found sample, but today time is not my friend, so let’s focalize to one of the malicious samples. Let’s get done the received sample by digging into the “second stage” dropped by the pPowerShell “first stage” from ssrdevelopments.co.za/a2/off.exe. After few seconds on second stage (off.exe) it became clear that it was a .NET software. By reversing the interpreted .NET language some clear text comments appeared interesting. Japanese language such as comments and variable names came out from static analysis. Let’s have a look to them.
 |
| Stage 2: Apparently Japanese characters |
 |
| Stage 2: Japanese Names and Self Encoding Structures |
 |
| Stage 2: Xoring function to extract Stage 3 |
On my run, the xored payload took the name of GIL.exe; another .NET executable. We are now facing the third stage. By analyzing the decompiled sample it became clear that:
- The coding style was quite different from the previous stage (Stage 2)
- The implementation style was different from the previous stage as well
- The sample was interested in information about the user, the machine, the web services on the PC and to many more windows specific parameters.
 |
| Stage 3: New Language in Strings and Class names |
 |
| Stage 3: New Code Style |
- Hash Stage 1:
- 7f1860673de9b1c2e6f7d6963a499e8ba4e412a1
- bf4a26c9e52a8cacc7afd7d95d197bff1e47fb00
- Hash Stage 2:
- ac55ee783f3ed0bd23eccd01040a128dc6dc7851
- Hash Stage 3:
- 6a38e4acd9ade0d85697d10683ec84fa0daed11c
- Persistence: HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\kij %APPDATA%\Roaming\kij\kij.exe
- Dropping URL:
- ssrdevelopments.co.za
- Command and Control:
- ssrdevelopments.co.za/cgi-bin/
- Related hashes from harvesting Dropping URL:
- 62c9d2ae7bafa9c594230c570b66ec2d4fa674a6
- b15b69170994918621ceb33cb339149bdff5b065
- 55abcfb85e664fbc8ad1cb8b60a08409c2d26caa
- f843427e9b7890f056eaa9909a5103bba6ffb8fd
- f2b81e66fcb1032238415b83b75b3fe8bf28247d
- cab90f7c935d355172b0db123d20b6a7d1403f65
- c1ba30d7adec6d545d5274f95943f787ad4c03e7
- ed9959bb0087f2c985b603cee0e760f3e0faaab15
- c93851627ffd996443f85d916f3dbedd70e0ff69
- 144b34b4816062c2308a755273159e0460ffd604
- 98293b80ccf312a8da99c2b5ca36656adebd0d0f
- 2875d1b54337b1c17c8f4cd5f6b2d579667ee3d9
- 0b4299ffb3f9aa59e19dd726e79d95365fe1d461
- 46bb0b10d790a3f21867308e7dcdeb06784a1570
- 0960726560a94fbbb327aa84244f9588a3c68be8
- a480a75c3af576e5656abadb47d11515a18a82be
- 2ba809c53eda2a475b1353c34f87ce62b6496e16
- 5b0c3071aa63e18aa91af59083223d3cceb0fa3c
- dc780bf338053e9c1b0fdf259c831eb8a2768169
As final thought I’d like to highlight the following key concept of that analysis:
- From a single email, the analyst could discover attacker’s assets, mapping them and disarming them (through IoC).
- The analyzed code shows apparent evidences to belonging to different groups of attackers.
- The analyzed samples show code reuse. Code reuse is dangerous because it makes attackers more powerful and extremely quick to change Malware behavior.
Hope you enjoyed.
The original post published by Marco Ramilli on his blog at the following URL:







Gloss