Hook Analyser 3.2 – Malware Analysis Tool
https://www.ispeech.org/text.to.speech
[adsense size='1']
- Spawn and Hook to Application – Enables you to spawn an application, and hook into it
- Hook to a specific running process – Allows you to hook to a running (active) process
- Static Malware Analysis – Scans PE/Windows executables to identify potential malware traces
- Application crash analysis – Allows you to analyse memory content when an application crashes
- Exe extractor – This module essentially extracts executables from running process/s
- The malware analysis module has been improved - and new signatures have been added
- Cyber Threat Intelligence module -
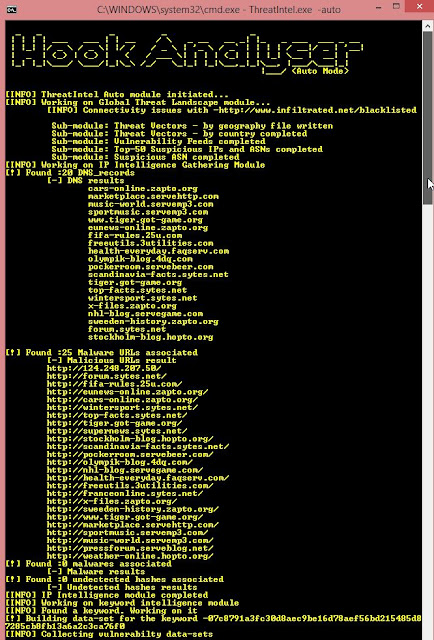
- IP Intelligence module (Analyse multiple IP addresses instead of just 1!). Sample output -
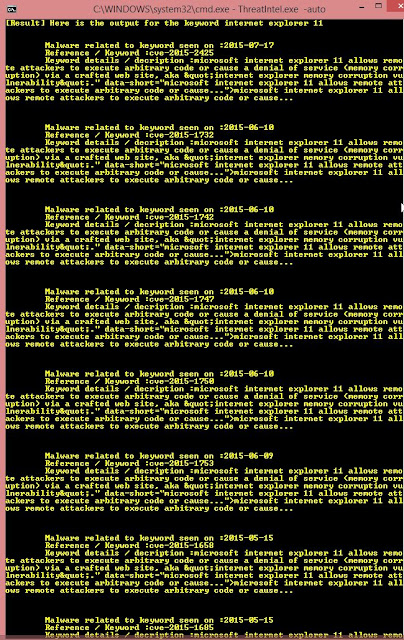
- Keyword Intelligence module (Analyse keywords e.g. Internet Explorer 11, IP address, Hash etc). Sample output -
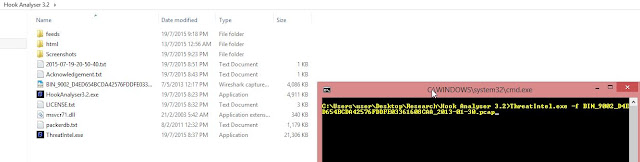
- Network file (PCAP) analysis - Analyse user-provided .PCAP file and performs analysis on external IP addresses. Example -
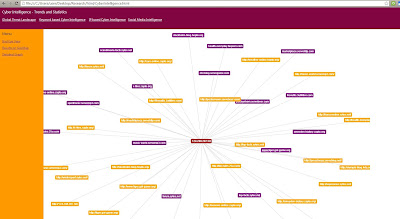
- Social Intelligence (Pulls data from Twitter- for user-defined keywords and performs network analysis). Example -
Let's look at "HOW-TO-USE" of this releases (Cyber Threat Intelligence) -
The tool can perform analysis via 2 methods - auto mode and manual mode.
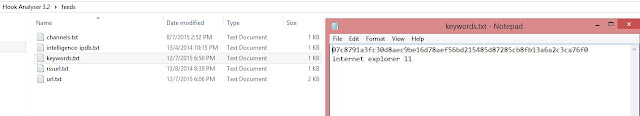
In the auto mode, the tool will use the following files for analysis -
[adsense size='1']
- Channels.txt (Path: feeds->channels.txt): Specify the list of the twitter related channels or keywords for monitoring. In the Auto mode, the monitoring is performed for 2 minutes only, however if you'd like to monitor indefinitely, please select the manual mode.
- Example -
- intelligence-ipdb.txt (Path: feeds->intelligence-ipdb.txt): Specify the list of IP addresses you'd like to analyse. Yes, you can provide as many IPs you'd like to.
- Example -
- Keywords.txt (Path: feeds->Keywords.txt): Specify the list of keywords you'd like to analyse. Yes, you can provide as many keywords you'd like to.
- Example -
- rssurl.txt (Path: feeds->rssurl.txt): Specify the RSS feeds to fetch vulnerability-related information.
- Example -
- url.txt (Path: feeds->url.txt): Specify the list of the URLs from where tool will pull malicious IP addresses information.
- Example -
Threat Intel module can be executed from HookAnalyser3.2.exe (option #6) file or can be executed directly through ThreatIntel.exe file. Refer to the following screenshots -
In manual mode, you'd need to provide filename as an argument. Example below -
Important note - The software shall only be used for "NON-COMMERCIAL" purposes. For commercial usage, written permission from the Author must be obtained prior to use.
[adsense size='1']





















Gloss