Hack the Box (HTB) machines walkthrough series — Lightweight
Today, we will be continuing with our exploration of Hack the Box (HTB) machines as seen in previous articles. This walkthrough is of an HTB machine named Lightweight.
HTB is an excellent platform that hosts machines belonging to multiple OSes. It also has some other challenges as well. Individuals have to solve the puzzle (simple enumeration plus pentest) in order to log into the platform and download the VPN pack to connect to the machines hosted on the HTB platform.
Note: Only write-ups of retired HTB machines are allowed. The machine in this article, named Lightweight, is retired.
The walkthrough
Let’s start with this machine.
1. Download the VPN pack for the individual user and use the guidelines to log into the HTB VPN.
2. The “Lightweight” machine IP is 10.10.10.119.
3. We will adopt the same methodology of performing penetration testing as we’ve previously used. Let’s start with enumeration in order to learn as much about the machine as possible.
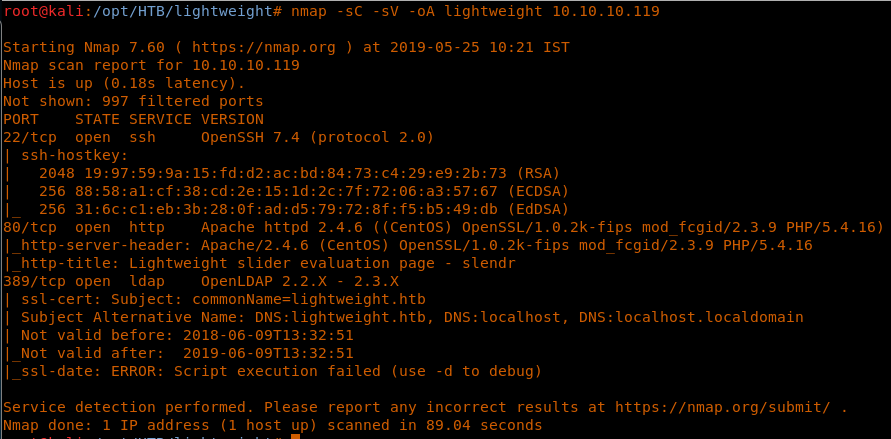
4. As usual, let’s start with the Nmap scan to gather more information about the services running on this machine. [CLICK IMAGES TO ENLARGE]
<

5. As we can see, we have ports 22, 80 and 389 open. Let’s start to enumerate port 389.
6. We can use the ldapsearch utility or Nmap script as well like below to perform enumeration on port 389.
<

7. We could see we have two users: ldapuser1 and ldapuser2. Remember this, and let’s move on to other ports for further enumeration.

8. Moving to port 80. Below is the landing page, which shows that the site is protected against brute-forcing. So we might need to avoid using directory enumeration for now on this box.

9. Let’s (Read more...)







Gloss