BSidesSF 2018 – Data Driven Bug Bounty (Arkadiy Tetelman)
iSpeech.org
Arkadiy Tetelman - Data Driven Bug Bounty
In a single sentence: if you're not collecting metrics from your bug bounty program then you're missing out on half of the value - it's not enough to simply triage, assign, and resolve individual bugs.
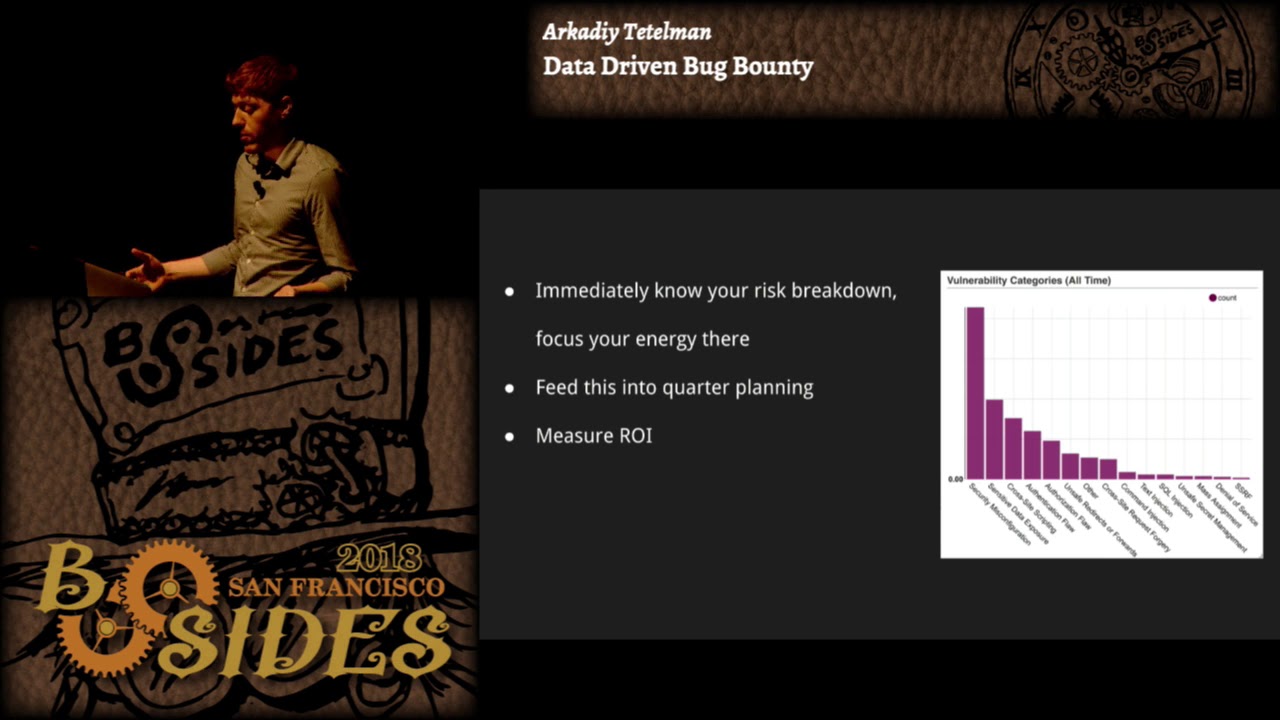
You should collect as much data as you can - things like first response/triage/payout/resolution time, what components are vulnerable and what bug classes are they vulnerable to, which teams are bugs originating from, how often do vulnerabilities go past SLA, and so on. This data can then be used for:
- assessing your company security posture
- figuring out which teams are fast responders and which teams consistently go past ticket SLA, and why
- starting dialogs with problematic teams, and getting alignment on resolving issues
- figuring out your security weak spots, and addressing those areas (feeding the data into your quarterly planning process)
- measuring improvement (or lack of improvement) over time
In this talk I'll share some of the metrics and graphs that we collect, and how we use them internally to improve our security process.
2018-04-25 07:28:39
source







Gloss