
Monthly Archives: December 2014
World News – December 19, 2014 – Sony hack & cybersecurity, child abuse & the state, vaccine dangers
December 20th, 2014 | 🕒
iSpeech.org 2014-12-20 03:45:01 source
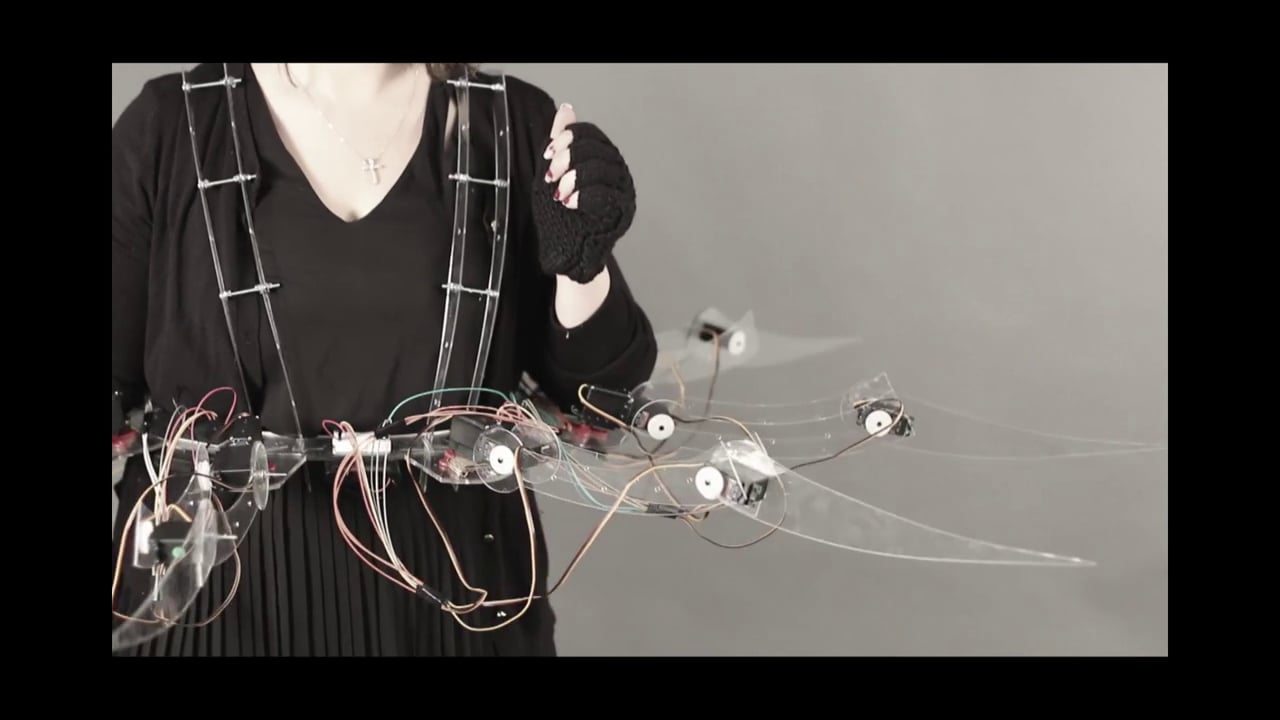
SPY[DER]
December 20th, 2014 | 🕒
iSpeech Prosthetic and Film by: Chrisoula Kapelonis Graduate School of Design, Harvard University Architecture of Cultural Prosthetics: Fall 2014 Professors:
Security Weekly #400 – Part 6, Interview with Mike Poor
December 20th, 2014 | 🕒
Text to Speech Mike Poor is a founder and Senior Security Analyst with InGuardians. Mike conducts forensic analysis, penetration tests,
How did North Korea pull off cyberattack?
December 20th, 2014 | 🕒
iSpeech CNN's Jim Sciutto reports on how U.S. intelligence traced North Korea to the Sony cyberhacking. 2014-12-19 22:21:47 source
AVG Anti Theft – Post based Stored XSS via CSRF Attack
December 19th, 2014 | 🕒
iSpeech.org # Service : AVG Anti-Theft # Vendor : AVG # Vulnerability : Post-based Stored-XSS via CSRF Attack # Severity
Hackers Can Read Your Private SMS and Listen to Phone Calls
December 19th, 2014 | 🕒
iSpeech.org Security researchers have discovered a massive security flaw that could let hackers and cybercriminals listen to private phone calls
Quantum Encryption Makes Credit Cards Fraud-Proof
December 19th, 2014 | 🕒
https://www.ispeech.org Credit card frauds are very common these days – today a data breach occurs in retailer’s shop, online shopping
Built-In Backdoor Found in Popular Chinese Android Smartphones
December 19th, 2014 | 🕒
chinese tts Chinese smartphone manufacturers have been criticized many times for suspected backdoors in its products, the popular Chinese smartphone
Outdated Computer Security Idea. Dragon's Den Funniest Clip ever! Hilarious!!
December 19th, 2014 | 🕒
iSpeech.org Barracuda Security comes to Dragon's Den to sell their anti-burglary security system for desktops. Just watch it. it's Hilarious!!
Android Wear Proof of Concept
December 18th, 2014 | 🕒
Powered by iSpeech A quick proof of concept using Android Wear to show getting a quote and automated text description
Cyber Security Operations Center
December 18th, 2014 | 🕒
Powered by iSpeech To withstand advanced cyber threats, it is essential to have an effective Cyber Security Operations Center (CSOC).
Deborah C. Peel, M.D.: The Greatest Data Breach You’ve Never Heard Of
December 18th, 2014 | 🕒
https://www.ispeech.org Who has your health information? According to Deborah Peel, probably more people than you think. Here she shares why


















Gloss