December 2nd, 2014 | 🕒
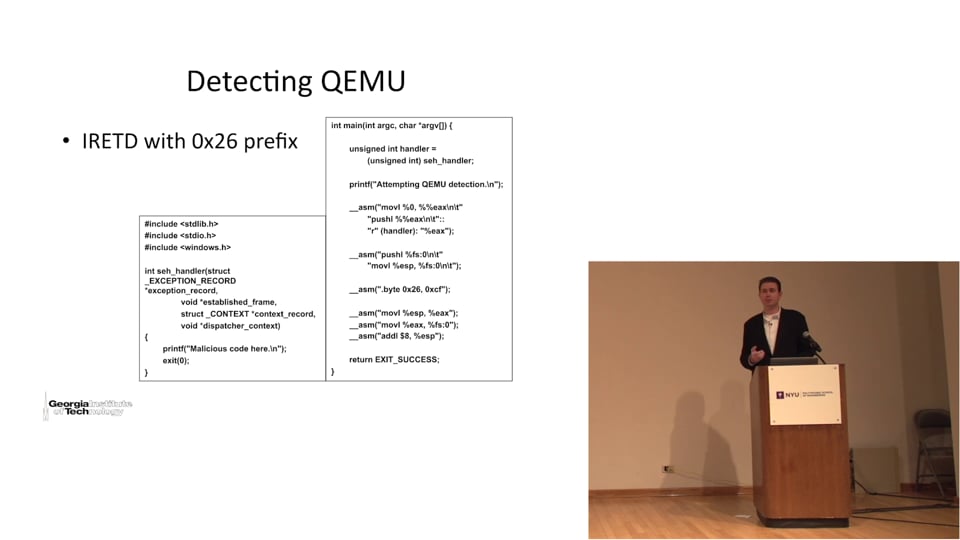
iSpeech.org The detection of virtualized malware analysis environments has become increasingly popular and commoditized. Sophisticated virtualization detection techniques are now
December 2nd, 2014 | 🕒
https://www.ispeech.org EVE MALER, VP Innovation & Emerging Technology, ForgeRock: The writing is on the wall: personal data is a new
December 2nd, 2014 | 🕒
iSpeech.org In this video, we will explain how to use Kaspersky Total Security to create an encrypted storage and hide
December 2nd, 2014 | 🕒
iSpeech.org North Korea said "wait and see" when asked if Pyongyang was involved in a cyberattack on Sony Pictures Entertainment
December 2nd, 2014 | 🕒
https://www.ispeech.org/text.to.speech In-depth look at the internet landscape when it comes to hackers. Indeed, how can we best protect ourselves, what
December 2nd, 2014 | 🕒
iSpeech.org Hacker Bug Bounties - RelateIQ Bug Bounty - (API) Application Side Mail Encoding Web Vulnerability @bugbounty #bugbounty #hacker @vuln_lab











Gloss