August 13th, 2014 | 🕒
https://www.ispeech.org Whistleblowers and journalists play a crucial role in scrutinising the powerful and holding them to account. The revelations by
August 12th, 2014 | 🕒
iSpeech.org Despite substantial investments in traditional security technologies, the vast majority of advanced attacks go undetected and proliferate undefended. Determined
August 12th, 2014 | 🕒
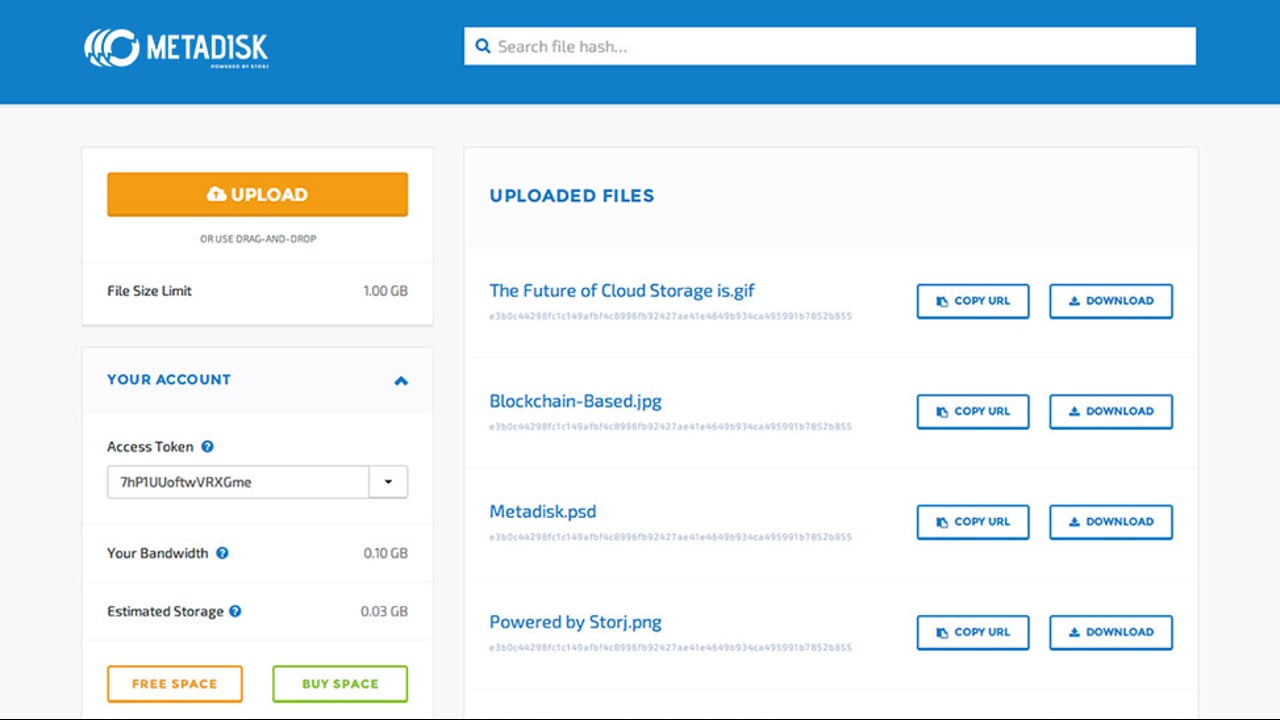
Text to Speech Demo The world's first blockchain-based decentralized file-sharing app. DRAG AND DROP No complicated software to download or
August 12th, 2014 | 🕒
Text to Speech RC3 and SPARSA Student run weekend competition. 5 Blue Teams (5 students each) and 1 Red Team
August 12th, 2014 | 🕒
https://www.ispeech.org/text.to.speech This is an attempt at disarming the bomb challenge that was in the hardware hacking / tamper evident village
August 12th, 2014 | 🕒
https://www.ispeech.org tutorial for beginners :protect php web sites from hackers sql injection attack ,By Foued BenBelkacem video, sharing, camera phone,
August 11th, 2014 | 🕒
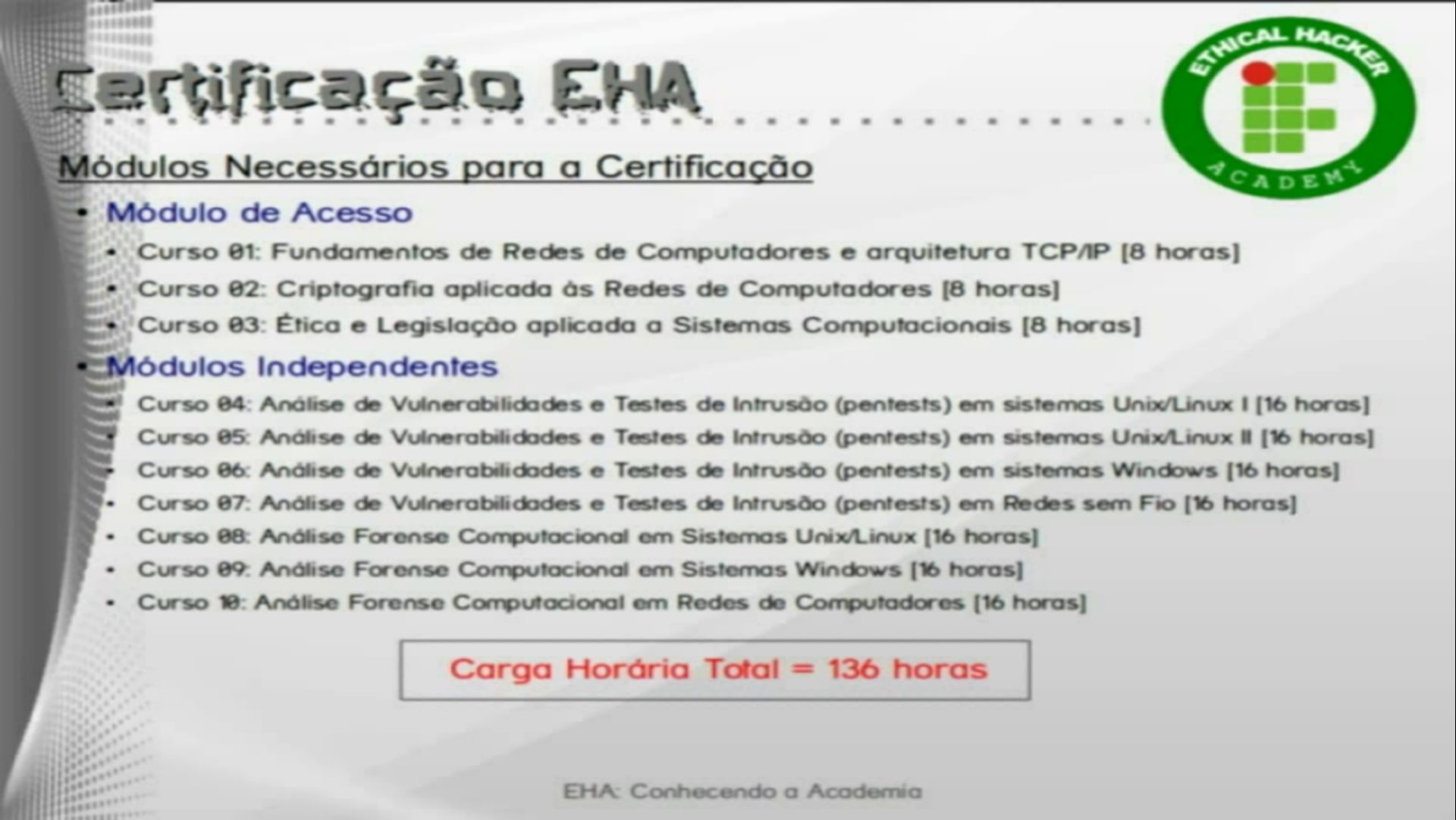
iSpeech.org Vídeo de apresentação do programa de extensão "Academia do Hacker Ético" (EHA/IFRN). Como o slogan "Hacking com Responsabilidade" a
August 11th, 2014 | 🕒
https://www.ispeech.org An editorial about the latest Ninja Turtles movie. Likes: 0 Viewed: source
August 11th, 2014 | 🕒
iSpeech „Disco 9/11“ (VÖ 13.08.2004) zielte ins Herz des Narrativs vom Krieg gegen den Terror, das ja vor allem eines
August 11th, 2014 | 🕒
https://www.ispeech.org Rushes MGFX Studio explore the dark side of internet surveillance in latest BBC Horizon, in which Wikileaks Julian Assange
August 11th, 2014 | 🕒
https://www.ispeech.org Un videotutorial donde se realiza una prueba de pentesting utilizando fuerza bruta. Enlace al sistema hiCrack: https://github.com/ironStark/hiCrack Enlace al
August 11th, 2014 | 🕒
https://www.ispeech.orgXCat is a command line program that aides in the exploitation of blind XPath injection vulnerabilities. It can be used
August 10th, 2014 | 🕒
https://www.ispeech.org/text.to.speech A creative security researcher has found a way to use his pet cat mapping dozens of vulnerable Wi-Fi networks
August 9th, 2014 | 🕒
https://www.ispeech.org/text.to.speech http://nakedsecurity.sophos.com/bad-passwords-on-pos-terminals http://nakedsecurity.sophos.com/how-to-send-5-million-spam-emails http://nakedsecurity.sophos.com/1-2-billion-logins-scooped-up-by-cybervor 2014-08-09 20:56:08 source


















Gloss