January 24th, 2020 | 🕒
https://www.ispeech.org/text.to.speech In this video, Katie Paxton-Fear @InsiderPhD shares with me her methodology for bug bounty hunting. Full video: https://www.youtube.com/watch?v=pzv-Lu7TbFI Katie
January 24th, 2020 | 🕒
iSpeech.org In this video, Katie Paxton-Fear @InsiderPhD shares with me her methodology for bug bounty hunting. Full video: https://www.youtube.com/watch?v=pzv-Lu7TbFI Katie
January 16th, 2020 | 🕒
Text to Voice Cisco CCIE Routing and Switching (R&S) 400-101 V5.1 Exam Topics: 5.1 Device security 5.1.d Describe device security
January 8th, 2020 | 🕒
Text to Speech Demo As of January 1, 2020, California became the first state to permit residents whose personal information
December 27th, 2019 | 🕒
iSpeech People rely on usernames and passwords to identify themselves to machines so they can gain access to data and
December 11th, 2019 | 🕒
iSpeech A fast web fuzzer written in Go. Heavily inspired by the great projects gobuster and wfuzz. Features Fast! Allows
October 16th, 2019 | 🕒
Powered by iSpeech Gobuster is a tool used to brute-force: URIs (directories and files) in web sites. DNS subdomains (with
September 14th, 2019 | 🕒
Powered by iSpeech A simple reverse shell written in python 3.7 just for fun. Actually it supports Windows and Linux
September 8th, 2019 | 🕒
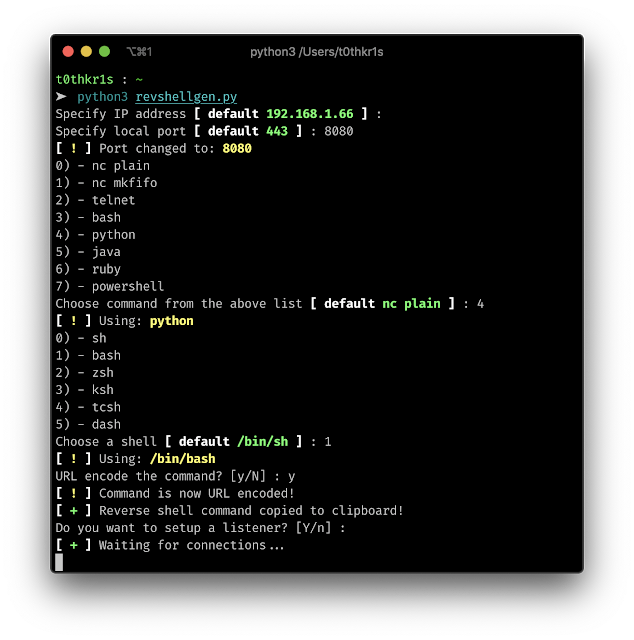
TTS Demo Standalone python script for generating reverse shells easily and automating the boring stuff like URL encoding the command
August 1st, 2019 | 🕒
text to speech Enlarge / This is going to go down on your permanent record. McMillan Publishers Edward Snowden, the
June 1st, 2019 | 🕒
iSpeech.org You are seeing a high-performant, coroutines-driven, and fully customisable implementation of Low & Slow load generator designed for real-world
March 11th, 2019 | 🕒
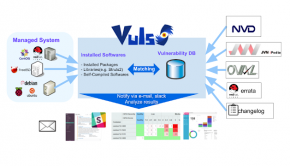
https://www.ispeech.org/text.to.speechVulnerability scanner for Linux/FreeBSD, agentless, written in golang. Twitter: @vuls_en adsense size='1'] DEMO adsense size='1'] Abstract For a system administrator,
March 9th, 2019 | 🕒
https://www.ispeech.org Goca is a FOCA fork written in Go, which is a tool used mainly to find metadata and hidden information in the documents its
September 17th, 2018 | 🕒
iSpeech.org Proactive Computer Security Module 1 Information Sharing and Threat Intelligence Proactive Computer Security https://www.coursera.org/learn/proactive-computer-security ============================ Youtube channel: https://www.youtube.com/user/intrigano ============================

















Gloss