March 26th, 2019 | 🕒
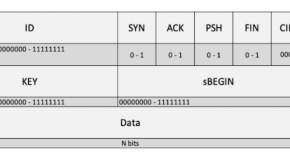
iSpeech Sms Stack is a Framework to provided TPC/IP based characteristics to the GSM Short Message Service. This framework works
March 26th, 2019 | 🕒
iSpeech ImageMagick is prone to a stack-based buffer-overflow vulnerability. Attackers can exploit this issue to run arbitrary code within the
March 23rd, 2019 | 🕒
https://www.ispeech.org Sms Stack is a Framework to provided TPC/IP based characteristics to the GSM Short Message Service. This framework works
February 7th, 2019 | 🕒
iSpeech https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers how to find the right module in buffer overflows, which will allow us to avoid
February 7th, 2019 | 🕒
TTS https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers how to find the EIP offset in buffer overflows, which will allow us to point
February 7th, 2019 | 🕒
https://www.ispeech.org https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers the art of fuzzing in buffer overflows, which allows us to identify if a command
August 25th, 2017 | 🕒
Powered by iSpeech Step 1 : Open Any browser , visit exploit-db.com and then go to Denial of Service Section
December 17th, 2015 | 🕒
https://www.ispeech.org/text.to.speech Remember that web application you wrote when you where first learning PHP? Ever wonder how vulnerable that code base
June 13th, 2011 | 🕒
https://www.ispeech.org This module exploits a vulnerability in the igssdataserver.exe component of 7-Technologies IGSS up to version 9.00.00 b11063. While processing
November 28th, 2009 | 🕒
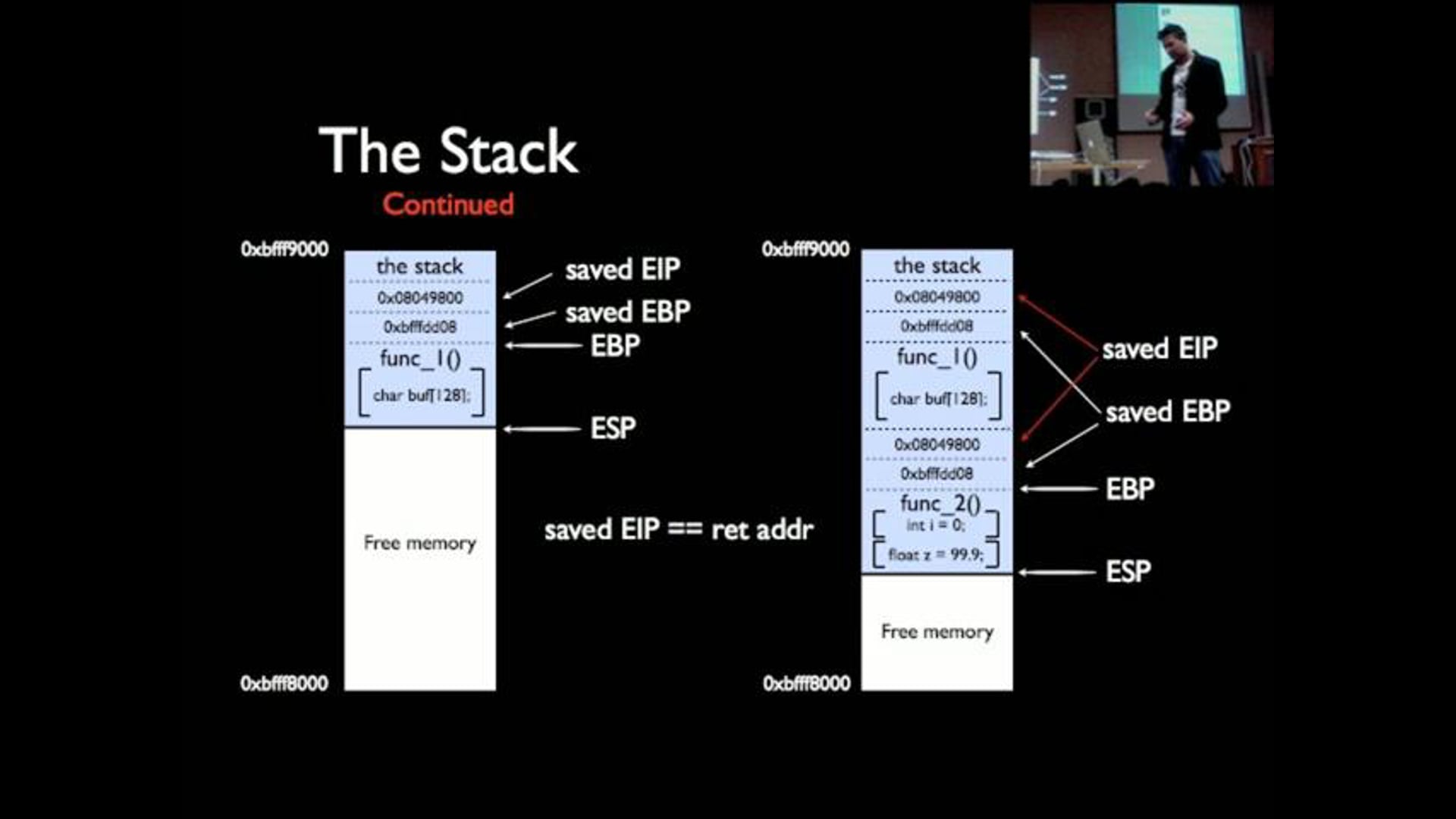
iSpeech ZaCon09 - Exploitation - Stalker Stalker talks on exploitation basics and walks through some of the solutions from the













Gloss