May 19th, 2019 | 🕒
https://www.ispeech.org Offensive Security Online Courses: https://www.blackhatethicalhacking.com/courses/ Complete Metasploit Course on Vimeo: https://vimeo.com/blackhatethicalhacking Hello Everyone! In today's Armitage Series Part (3),
May 6th, 2019 | 🕒
Powered by iSpeech During the past few days, we heard of a lot of incidents involving accidental data leakage from
April 18th, 2019 | 🕒
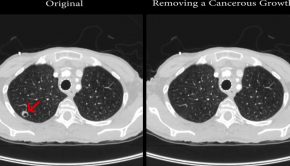
text to speech The object on the doctor’s screen, a white mass on a dark void, sits in the lungs,
April 6th, 2019 | 🕒
iSpeech.org Researchers are presenting with a malware that not only modifies CT scan results, it also does them with such
April 4th, 2019 | 🕒
iSpeech.org This malware is related to two other malware families namely MongoLock ransomware and XBash. This malware does not include
August 18th, 2018 | 🕒
https://www.ispeech.org/text.to.speech To address the challenges of vulnerability detections increasing year over year, Qualys is introducing new ways to visualize vulnerability
January 14th, 2017 | 🕒
iSpeech.org Network scanning is a procedure for identifying active hosts on a network, either for the purpose of attacking them
May 29th, 2015 | 🕒
https://www.ispeech.org/text.to.speech Yasuo is a ruby script that scans for vulnerable 3rd-party web applications. While working on a network security assessment
January 16th, 2015 | 🕒
iSpeechOpen source tool called Gitrob trawls the Github repositories for sensitive data Security researcher and member of SoundCloud security team, Michael
September 28th, 2010 | 🕒
ttsPerforming OWASP and PCI DSS Audits of Web Based Applications Tenable Network Security offers solutions to perform vulnerability scanning,passive network
July 2nd, 2010 | 🕒
iSpeech.org Is your PC slow? Is your PC protected from potential spyware, adware, Trojans, bots, worms, and hijackers? Are you
















Gloss