December 19th, 2019 | 🕒
https://www.ispeech.org Everywhere you look today you see “risk-based security” being touted as the next big thing. Knowing your assets, understanding
June 29th, 2018 | 🕒
iSpeech Whether it's an unsecured Kubernetes configuration or the Meltdown/Spectre exploits, there is always a way into your company's seemingly
July 6th, 2017 | 🕒
iSpeech Discussing real use cases of state actors engaged in APT campaigns, explore what can be done with the available
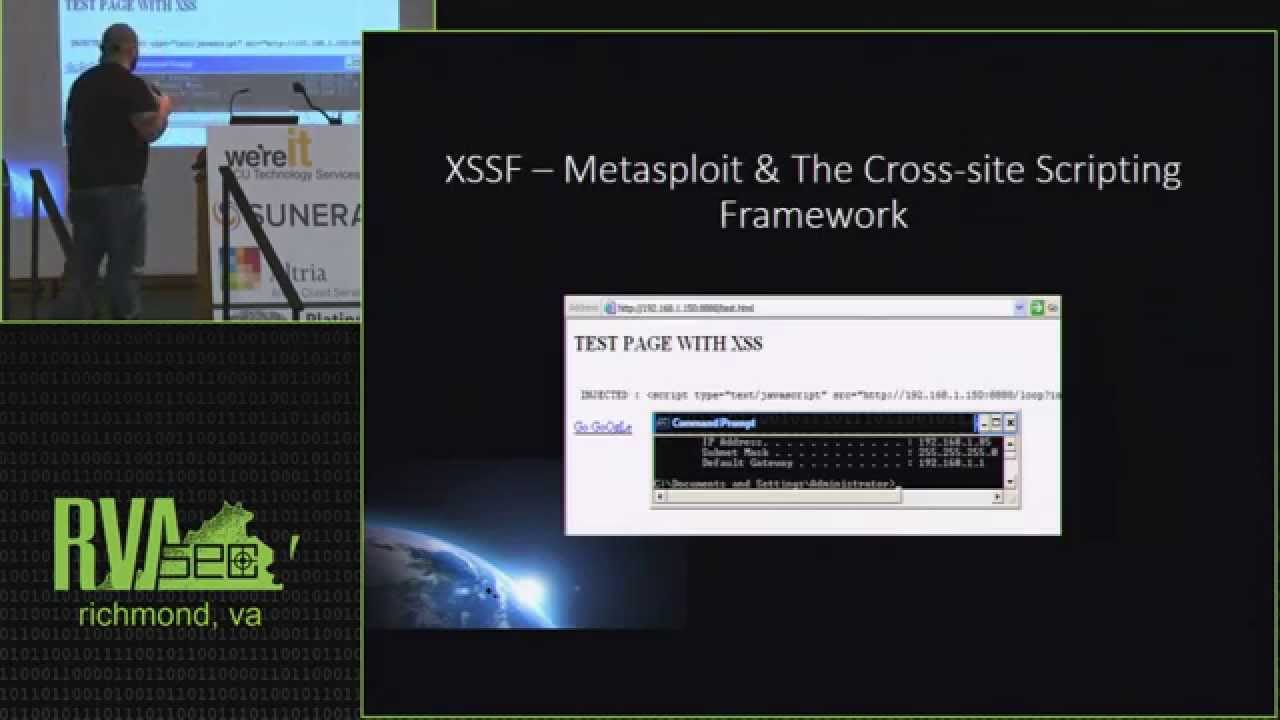
July 6th, 2015 | 🕒
iSpeech Metasploit is most commonly known for its epic pwnage of network and service level vulnerabilities. What you may not
July 3rd, 2013 | 🕒
iSpeech.org Slides: http://rvasec.com/slides/2013/Lockery-Social_media_forensics.ppt With the advent of social media, mobile devices, digital photography and media sharing sites becoming critical data
July 1st, 2013 | 🕒
Free Text to Speech Slides: http://rvasec.com/slides/2013/Kouns-Risk_Assessment.pdf Risk assessment, we have all heard the words and often times use them ourselves,










Gloss