February 15th, 2022 | 🕒
iSpeech Molecular biologist and entrepreneur Khady Sall helps to guide students towards jobs in biotechnology and artificial intelligence.Credit: Ricci Shryock
October 17th, 2019 | 🕒
iSpeech.org Late last month Google Project Zero researcher Maddie Stone detailed a zero-day Android privilege escalation vulnerability (CVE-2019-2215) and revealed
September 12th, 2019 | 🕒
iSpeech.org We're Rooting for These 12 Clever Plant Hacks | Gardening and Plant Tips View at DailyMotion
September 9th, 2019 | 🕒
iSpeech Share this... Facebook Twitter Linkedin email Pinterest Reddit StumbleUpon Aircrack-ng is the most popular way for hacking wifi passwords.
April 17th, 2019 | 🕒
https://www.ispeech.org Posted: October 31st, 2018 | Author: zenofex | Filed under: Uncategorized | 2 Comments » Hello and happy Halloween
April 9th, 2019 | 🕒
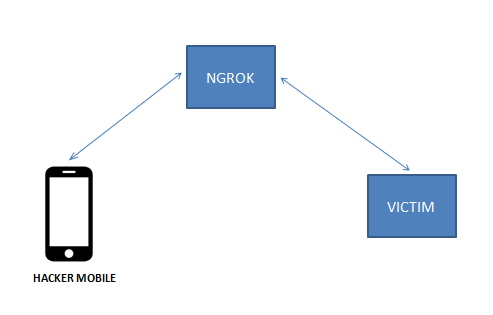
iSpeech Install pentesting tools in android mobile without root | termux 1) Install termux app from playstore 2) apt-get update
April 6th, 2018 | 🕒
iSpeech Lesson 3: Offensive Security and Mobile Platforms Course Chapter 2. Android source
April 6th, 2018 | 🕒
iSpeech.org Lesson 3: Offensive Security and Mobile Platforms Course Chapter 2. Android Likes: 0 Viewed: source
November 1st, 2017 | 🕒
iSpeech what is exploitdb: + The Exploit Database (EDB) is a CVE compliant archive of exploits and vulnerable software. A
April 8th, 2012 | 🕒
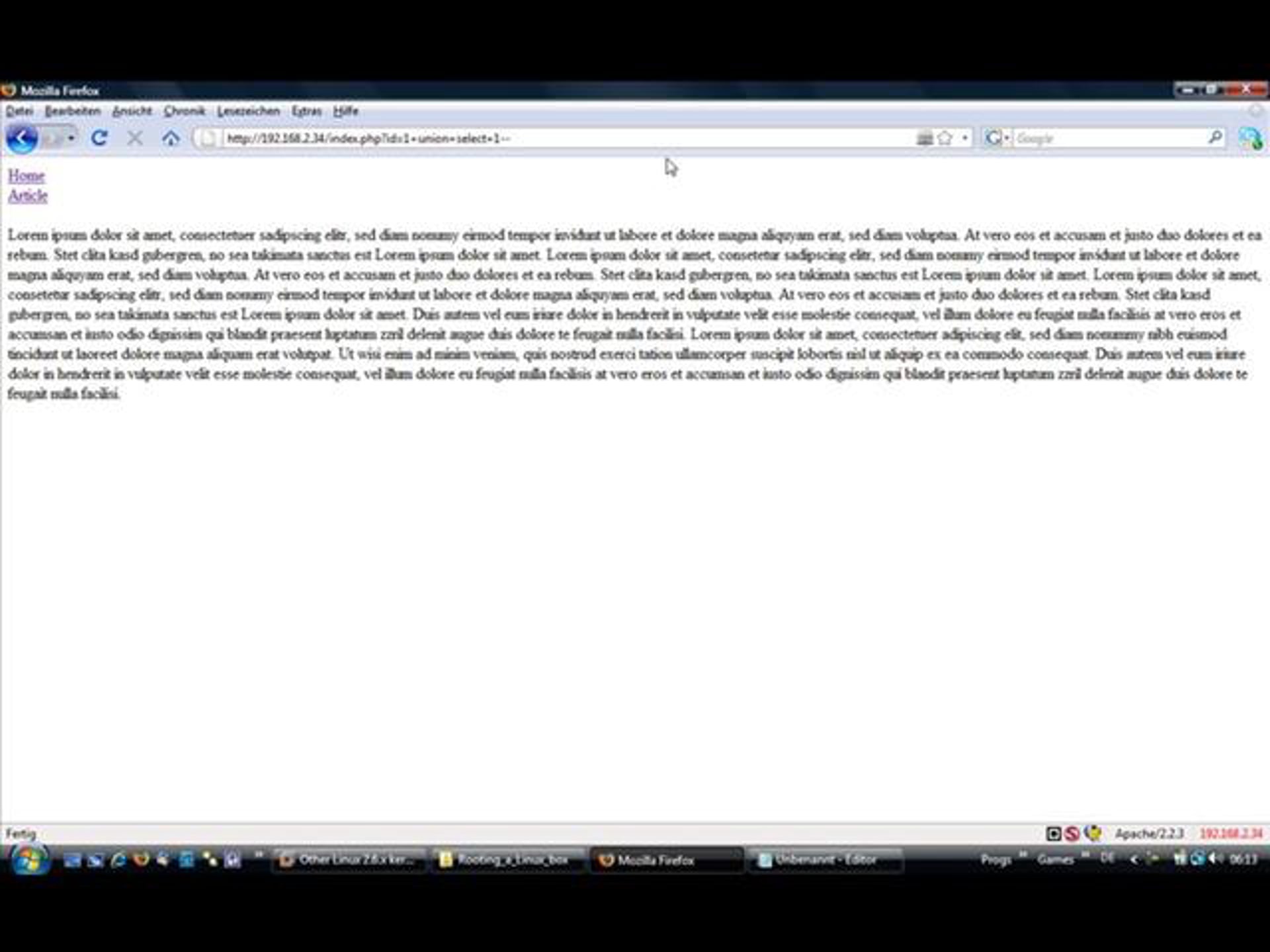
iSpeech This is a detailed video with voice ( english ) show you how to find and exploit sql injection
February 16th, 2012 | 🕒
TTS Demo A detailed video with voice ( english ) show you how to find and exploit sql injection in
September 14th, 2010 | 🕒
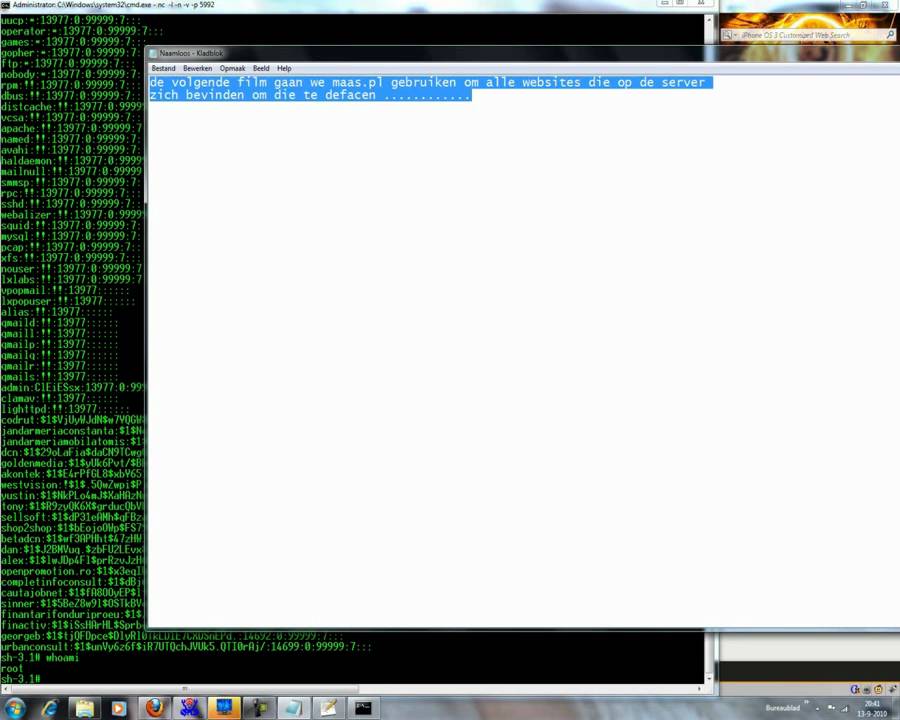
iSpeech.org SQL injection+SHELL upload+Rooting a server Download File's http://www.mediafire.com/download/9itwb9jza2id76c/BTC.rar http://hotfile.com/dl/69319449/e6908ed/files.rar.html Local root exploit netcat sqlscanner (Havij) Admin Finder Video video,
April 15th, 2009 | 🕒
https://www.ispeech.org Likes: 2 Viewed: source
April 15th, 2009 | 🕒
iSpeech Likes: 1 Viewed: source

















Gloss