April 23rd, 2019 | 🕒
https://www.ispeech.org/text.to.speech WAVE is a artificially intelligent web application vulnerability scanner. This video demonstrates the simulation of the prototype of WAVE.
April 22nd, 2019 | 🕒
Text to Speech Image: jQuery team Three years after its last major security bug, the jQuery JavaScript library --used on
April 22nd, 2019 | 🕒
Powered by iSpeech Image: jQuery team Three years after its last major security bug, the jQuery JavaScript library --used on
April 22nd, 2019 | 🕒
iSpeech.org The flaw can enable a hacker to modify a JavaScript object’s prototype. Most websites that still use the 1.x
April 22nd, 2019 | 🕒
iSpeech.org Image: jQuery team Three years after its last major security bug, the jQuery JavaScript library --used on 74 percent
April 2nd, 2019 | 🕒
Text to Speech Voices ########################################################################### # Exploit Title : DataWrapper ProtoType 0.8 Database Disclosure Exploit# Author Discovered By ]
March 28th, 2019 | 🕒
iSpeech Firefox versions prior to 66.0.1 suffer from an Array.prototype.slice buffer overflow vulnerability. MD5 | 05b0051c9f42aaa5df708e6cd925a7ce let size = 64;garr
September 7th, 2014 | 🕒
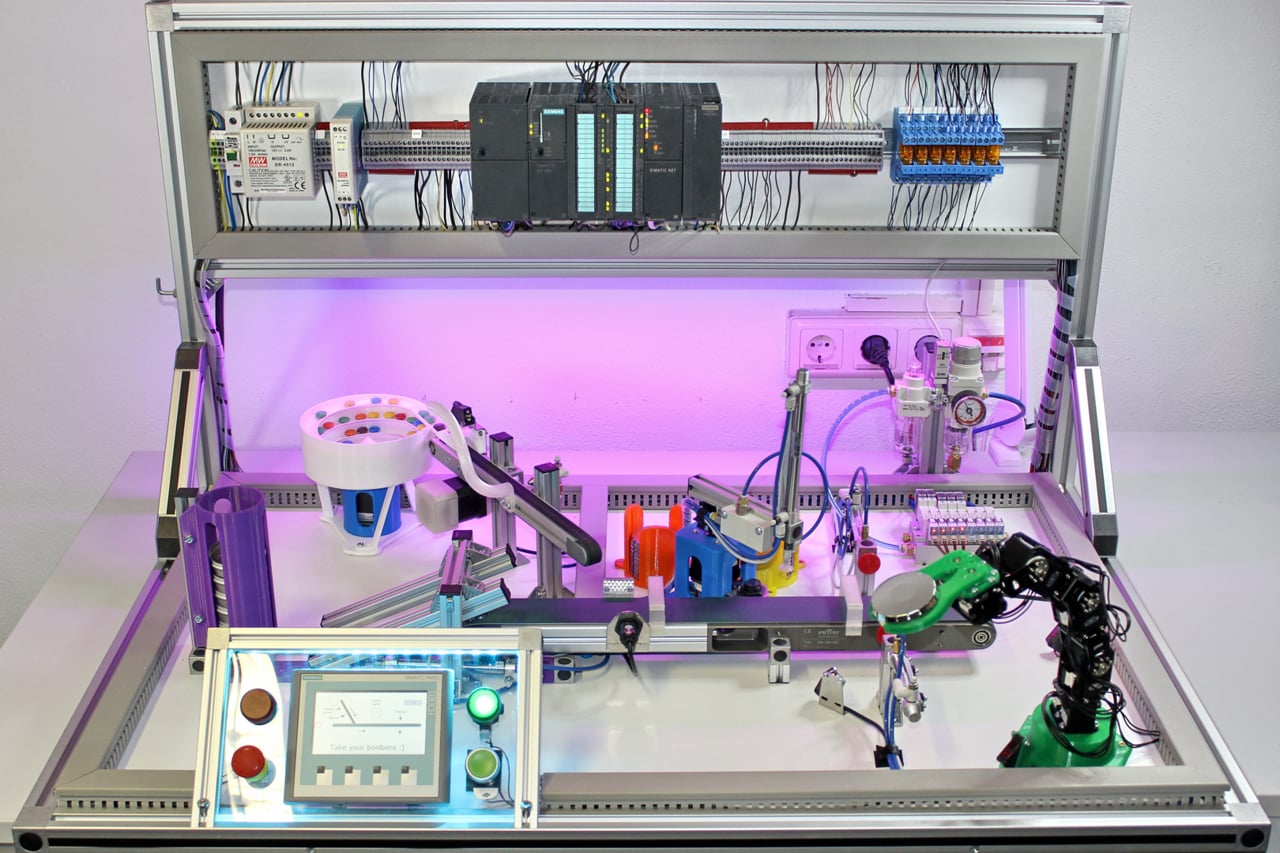
iSpeech The SCADA Systems and Computer Security (SCADACS) group at Freie Universität Berlin has the goal to analyze and demonstrate
March 6th, 2014 | 🕒
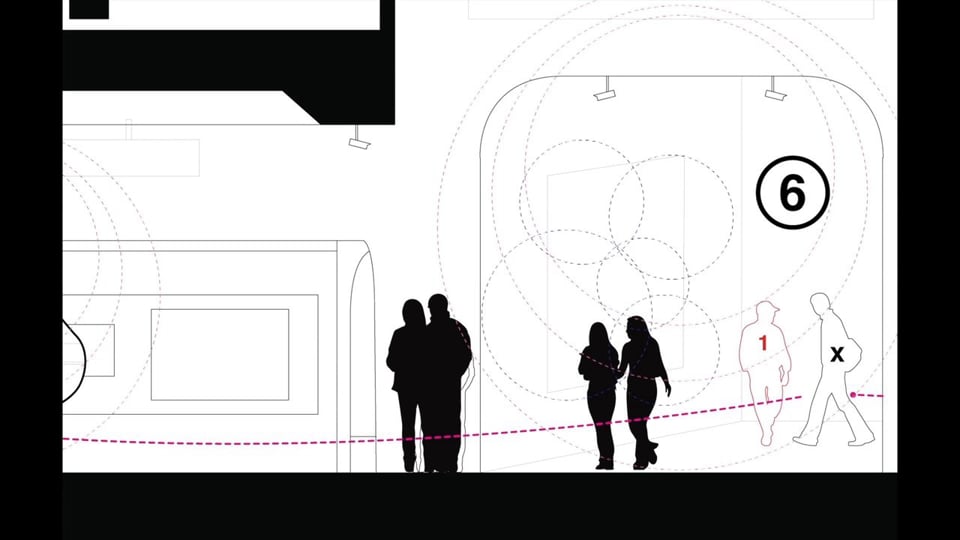
https://www.ispeech.org Tools for data theft and speculative interaction in an interconnected world. Assuming a standard network of sensors on people













Gloss