September 25th, 2017 | 🕒
TTS Demo NEW CHANNEL LINK https://www.youtube.com/channel/UC3f76M6v9YGoopqMwV0rjHQ EQUIFAX TIME LINE (you can search for more information) 😮Hack Release https://investor.equifax.com/news-and-events/news/2017/09-07-2017-213000628 🤑 Executives
September 17th, 2016 | 🕒
https://www.ispeech.org/text.to.speech Download link + instruction - http://bit.ly/2cSxfF2 Tags - ignore please] NBA 2K17 CODEX NBA 2K17 3DM NBA 2K17 SKIDROW
September 14th, 2016 | 🕒
iSpeech Download link + instruction - http://bit.ly/2cwyeWw Tags - ignore please] ReCore CODEX ReCore 3DM ReCore SKIDROW ReCore NoCD ReCore
August 22nd, 2016 | 🕒
iSpeech Download link + instruction - http://bit.ly/2bbozbI Tags - ignore please] Deus Ex Mankind Divided CODEX Deus Ex Mankind Divided
February 29th, 2016 | 🕒
iSpeech What is credit card? It is used mainly to purchase online and for verification purposes. Here is great news
October 5th, 2015 | 🕒
Free Text to Speech The increasing number of smart devices will have a significant impact on the threat landscape, says
August 6th, 2015 | 🕒
iSpeech Hackers can steal any number of fingerprints remotely without user’s knowledge from Android smartphones Two FireEye researchers have discovered
June 19th, 2015 | 🕒
iSpeech Security expert at Voidsec have analyzed the popular social networking minds.com disclosing a number of security vulnerabilities. Security expert
January 14th, 2015 | 🕒
iSpeech "McAfee Customer Support Number 1-855-241-6700 offer Online Technical Support for McAfee. If you are facing problem in McAfee Call
July 12th, 2014 | 🕒
https://www.ispeech.org Friday, July 13, 2012: 11:00 pm (Sassaman): How easy is it to end up with illegal content on your
April 30th, 2014 | 🕒
Text to Speech How can we estimate the number of primes up to x? Watch the next lesson: https://www.khanacademy.org/computing/computer-science/cryptography/comp-number-theory/v/time-space-tradeoff?utm_source=YT&utm_medium=Desc&utm_campaign=computerscience Missed
June 3rd, 2012 | 🕒
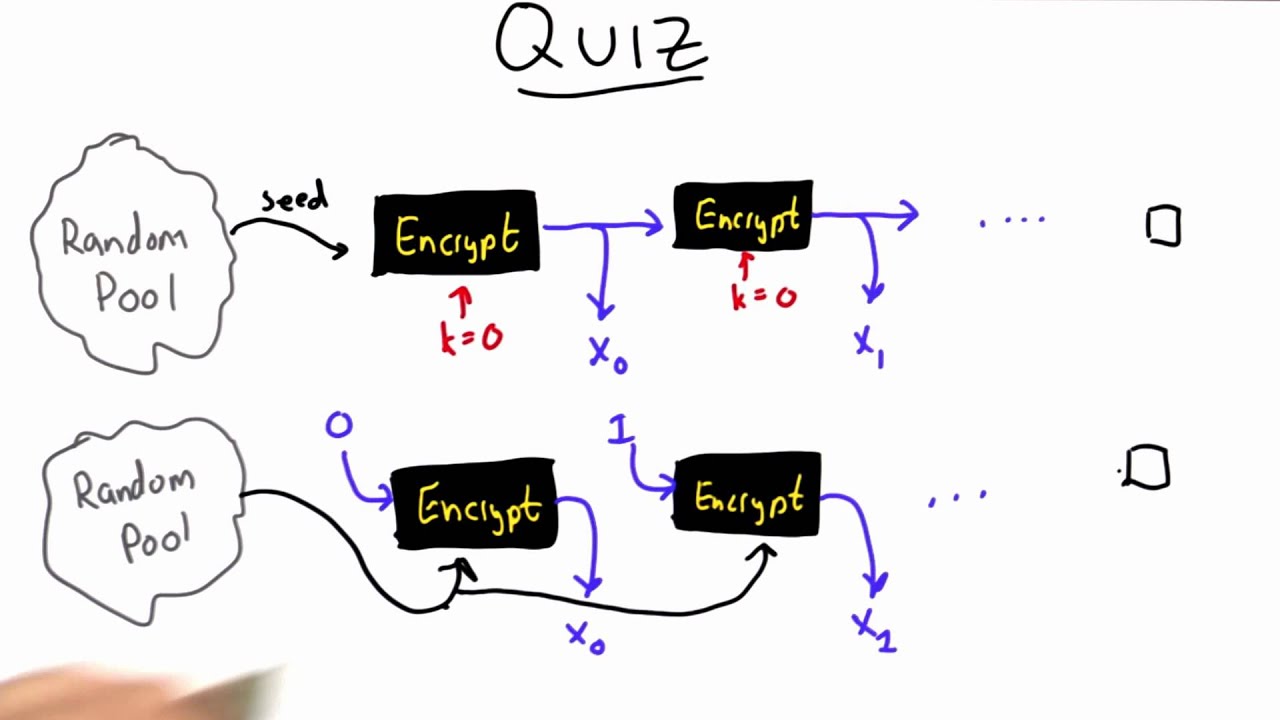
iSpeech This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387. video, sharing, camera
May 24th, 2012 | 🕒
https://www.ispeech.orgHow Firewall Middleboxes Reduce Security Abstract In this paper, we report a newly discovered “offpath TCP sequence number inference” attack
January 17th, 2011 | 🕒
iSpeech Speaker: Sean Boyce Security Researcher The problem of generating "reasonable" approximations to random numbers has been solved quite some


















Gloss