February 14th, 2023 | 🕒
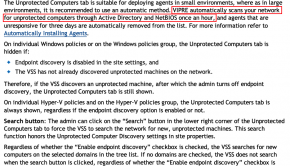
https://www.ispeech.org/text.to.speech This post documents a security mis-configuation I observed in VIPRE Endpoint Security with Endpoint Discovery. A few years ago,
February 14th, 2023 | 🕒
https://www.ispeech.org*] Recently I was browsing Twitter and came across a very interesting tweet: Umm- why can I find the password
February 14th, 2023 | 🕒
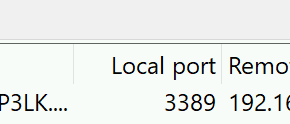
Powered by iSpeech*] I’ve often found that while performing password guessing on a network, I’ll find valid credentials, but the
February 13th, 2023 | 🕒
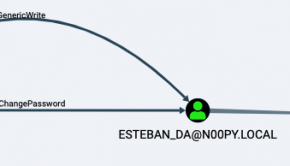
iSpeech.org*] Recently I came upon an attack path in BloodHound that looked like this: I had control of a computer
February 13th, 2023 | 🕒
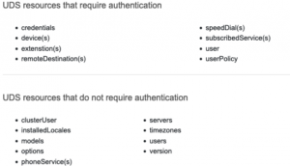
https://www.ispeech.org/text.to.speech This blog is about something I found recently regarding Cisco Unified Call Manager (CUCM). While playing around with SeeYouCM
February 12th, 2023 | 🕒
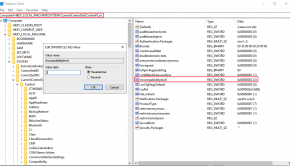
iSpeech*] There are two common reasons you may want to change a user’s password during a penetration test: You have
February 12th, 2023 | 🕒
https://www.ispeech.org In the past I had written a quick blog post on password spraying Dell SonicWALL Virtual Office. While it
February 12th, 2023 | 🕒
iSpeech.org This blog is meant to serve as a guide for practical exploitation of systems that allow for the NTLMv1
February 11th, 2023 | 🕒
https://www.ispeech.org*] Metasploit recently released version 6.3. With it came a whole lot of new features related to LDAP operations and









Gloss