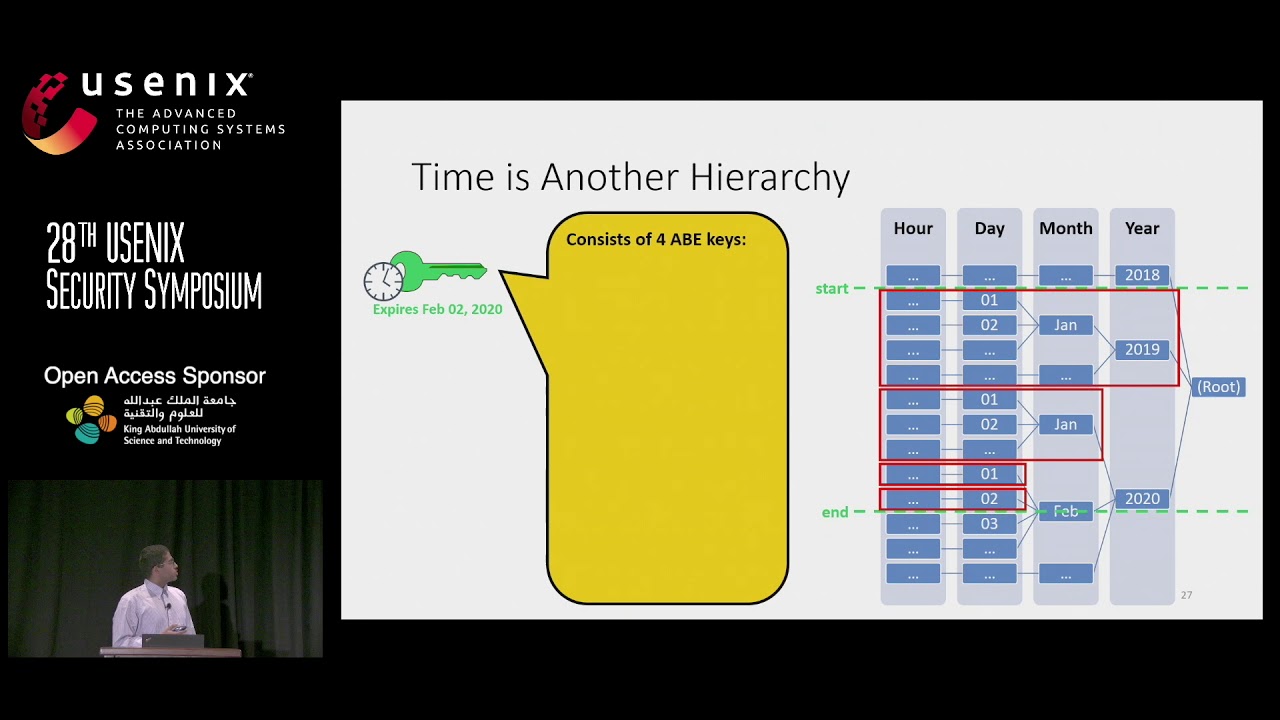
USENIX Security '19 – JEDI: Many-to-Many End-to-End Encryption and Key Delegation for IoT
September 27th, 2019 | 🕒
iSpeech JEDI: Many-to-Many End-to-End Encryption and Key Delegation for IoT Sam Kumar, University of California, Berkeley As the Internet of







Gloss