March 15th, 2024 | 🕒
Text to Speech #- Exploit Title: JetBrains TeamCity 2023.05.3 - Remote Code Execution (RCE)#- Shodan Dork: http.title:TeamCity , http.favicon.hash:-1944119648#- Exploit
March 14th, 2024 | 🕒
Speech Synthesis ### This module requires Metasploit: https://metasploit.com/download# Current source: https://github.com/rapid7/metasploit-framework## class MetasploitModule < Msf::Exploit::RemoteRank = ExcellentRanking prepend Msf::Exploit::Remote::AutoCheckinclude Msf::Exploit::Remote::HttpClientinclude
March 11th, 2024 | 🕒
TTS Mar 11, 2024NewsroomRansomware / Vulnerability The threat actors behind the BianLian ransomware have been observed exploiting security flaws in
March 8th, 2024 | 🕒
iSpeech Mar 08, 2024NewsroomVulnerability / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a critical
March 7th, 2024 | 🕒
iSpeechJetBrains TeamCity versions prior to 2023.11.4 remote authentication bypass exploit that can be leveraged for user addition and remote code
March 5th, 2024 | 🕒
Text to Speech Demo Mar 05, 2024NewsroomVulnerability / Network Security A new pair of security vulnerabilities have been disclosed in
February 7th, 2024 | 🕒
iSpeech.org Feb 07, 2024NewsroomCybersecurity / Software Security JetBrains is alerting customers of a critical security flaw in its TeamCity On-Premises
December 14th, 2023 | 🕒
iSpeech Threat actors affiliated with the Russian Foreign Intelligence Service (SVR) have targeted unpatched JetBrains TeamCity servers in widespread attacks
October 19th, 2023 | 🕒
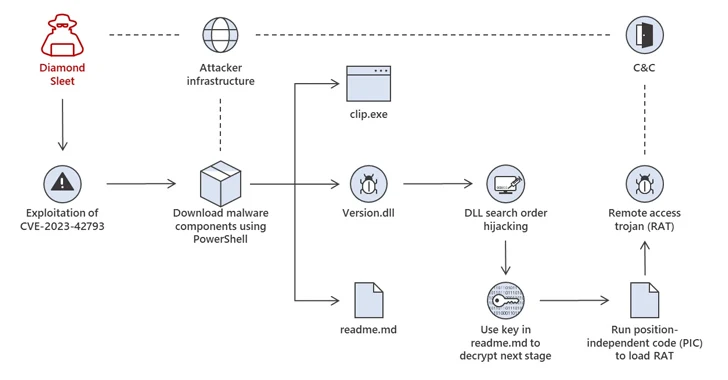
text to speech Oct 19, 2023Newsroom North Korean threat actors are actively exploiting a critical security flaw in JetBrains TeamCity
October 5th, 2023 | 🕒
https://www.ispeech.org Oct 05, 2023NewsroomVulnerability / Cyber Attack The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security
September 29th, 2023 | 🕒
https://www.ispeech.org ### This module requires Metasploit: https://metasploit.com/download# Current source: https://github.com/rapid7/metasploit-framework## class MetasploitModule < Msf::Exploit::RemoteRank = ExcellentRanking include Msf::Exploit::Retryprepend Msf::Exploit::Remote::AutoCheckinclude Msf::Exploit::Remote::HttpClient
September 26th, 2023 | 🕒
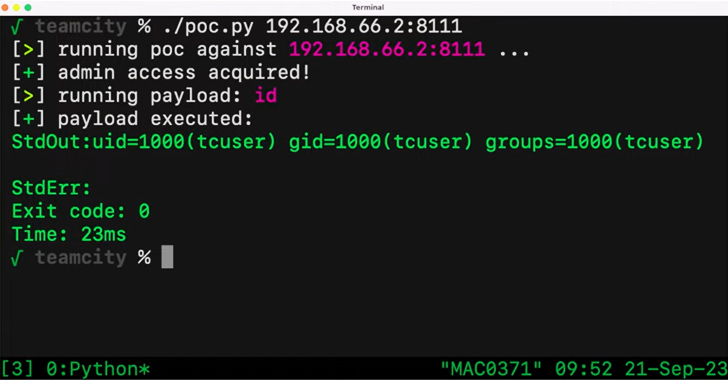
iSpeech Sep 26, 2023THNVulnerability / Source Code A critical security vulnerability in the JetBrains TeamCity continuous integration and continuous deployment
January 7th, 2021 | 🕒
Powered by iSpeech CISA said late yesterday that it had determined that the threat actors behind the Solorigate incident used
February 4th, 2020 | 🕒
https://www.ispeech.org/text.to.speech














Gloss