May 9th, 2013 | 🕒
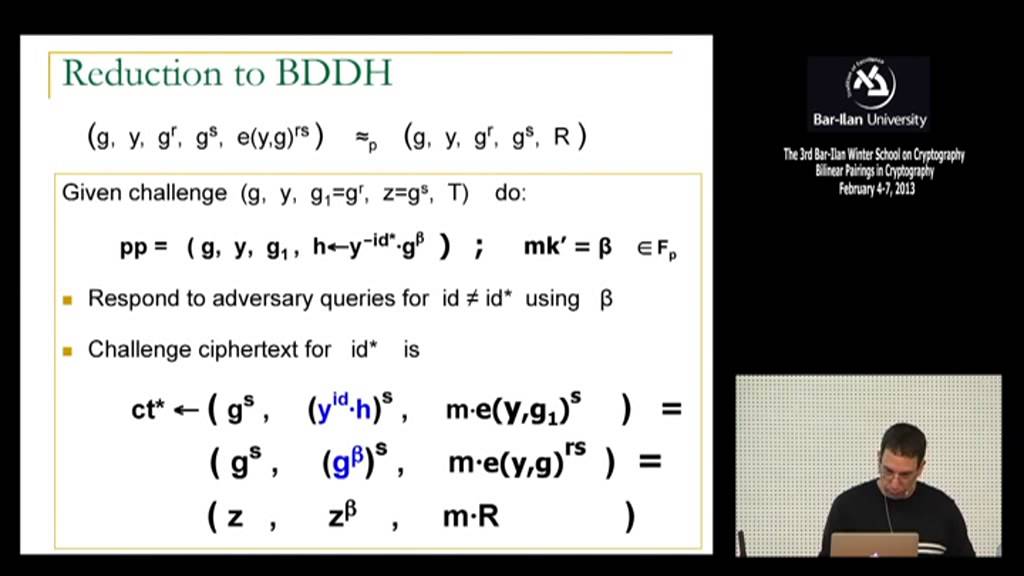
https://www.ispeech.org The 3rd Bar-Ilan Winter School on Cryptography: Bilinear Pairings in Cryptography, which was held between February 4th - 7th,
December 10th, 2012 | 🕒
iSpeech Visit www.MarkSeguin.com to contact us for more information on how you can enroll in products. We provide best-in-class training
September 12th, 2012 | 🕒
https://www.ispeech.org/text.to.speech BEFORE WATCHING SWITCH TO HTML5 PLAYER( bottom right below video description) Our everyday lives are increasingly dependent upon the
April 16th, 2012 | 🕒
iSpeech.org Computer forensics expert Dave Kleiman was featured on ABC News, WPBF 25 Florida, discussing with Alexis Rivera explains, modern-day
August 26th, 2011 | 🕒
https://www.ispeech.org Holistic data security is when people and technology work together to protect customers and intellectual property. Data security is
February 1st, 2011 | 🕒
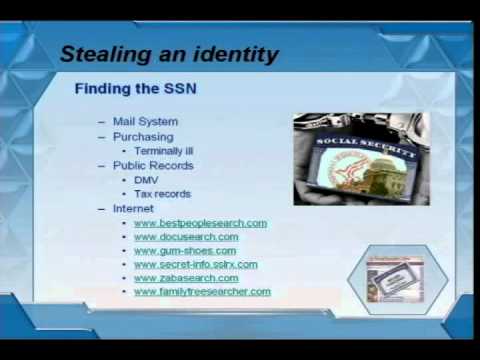
Text to Speech Demo Speaker: Johan Hybinette Abstract: An Anonymous identity is difficult but not impossible to obtain. With help
April 10th, 2009 | 🕒
https://www.ispeech.org/text.to.speech http://budurl.com/InvisusAntiVirus . http://budurl.com/ISAEvaluationTour Contact John Piro Toll Free (877) JON-PIRO Invisus Direct Computer AntiVirus Spyware & Whole Indentity Theft
November 28th, 2008 | 🕒
Speech Synthesis Identity Theft Speaker discusses Cyber Monday and Computer Security www.IDTheftSecurity.com video, sharing, camera phone, video phone, free, upload













Gloss