March 21st, 2020 | 🕒
https://www.ispeech.org Introduction to applied cryptography Cryptography is widely used in modern technology, particularly in software. The primary purpose of cryptography
November 16th, 2019 | 🕒
https://www.ispeech.org This talk explores how AI is revolutionizing hardware side-channel attacks and what this new wave of attacks mean for
May 25th, 2019 | 🕒
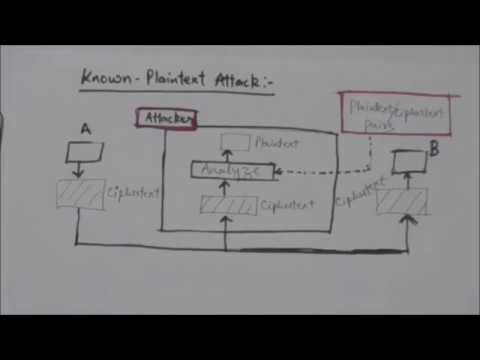
Text to Speech Voices NETWORK SECURITY, CRYPTANALYSIS, KNOWN PLAINTEXT, CHOSEN PLAINTEXT, CHOSEN CIPHERTEXT, BRUTEFORCE,, CIPHERTEXT ONLY video, sharing, camera phone,
February 18th, 2019 | 🕒
iSpeech.org This video is part of Riscure’s free online training “Side Channel Analysis (SCA) for IoT developers - A practical
December 29th, 2018 | 🕒
https://www.ispeech.org/text.to.speech By Ben Nassi. Read the full paper on: https://www.computer.org/csdl/proceedings/sp/2019/6660/00/666000a800.pdf 2018-12-29 17:14:24 source
October 16th, 2017 | 🕒
iSpeech.org Learn network security in a simple and a easy way. What is Cryptology,Cryptography and Cryptanalysis?(NETWORK SECURITY) 2017-10-16 13:42:11 source
May 12th, 2017 | 🕒
iSpeech Cryptanalysis : Types Of Cryptanalysis Attacks On Cryptography. Visit Our Channel :- https://www.youtube.com/channel/UCxikHwpro-DB02ix-NovvtQ In this lecture we have taught
May 31st, 2012 | 🕒
https://www.ispeech.org Winter School on Lattice-Based Cryptography and Applications, which took place at Bar-Ilan University between february 19 - 22. The
July 14th, 2011 | 🕒
https://www.ispeech.org/text.to.speech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 2: Crypto Basics Sections 2.5-2.6 taxonomy of cryptography,













Gloss