September 13th, 2014 | 🕒
https://www.ispeech.org computer hacking,computer hacking for beginners,computer hacking forensic investigator,computer hacking tricks,computer hacking,computer hacking for beginners,computer hacking forensic investigator,computer hacking tricks,computer
October 16th, 2013 | 🕒
iSpeech Sophos security expert Maxim Weinstein (in conjunction with The Center for Internet Security) helps beginners learn how malware works,
July 6th, 2013 | 🕒
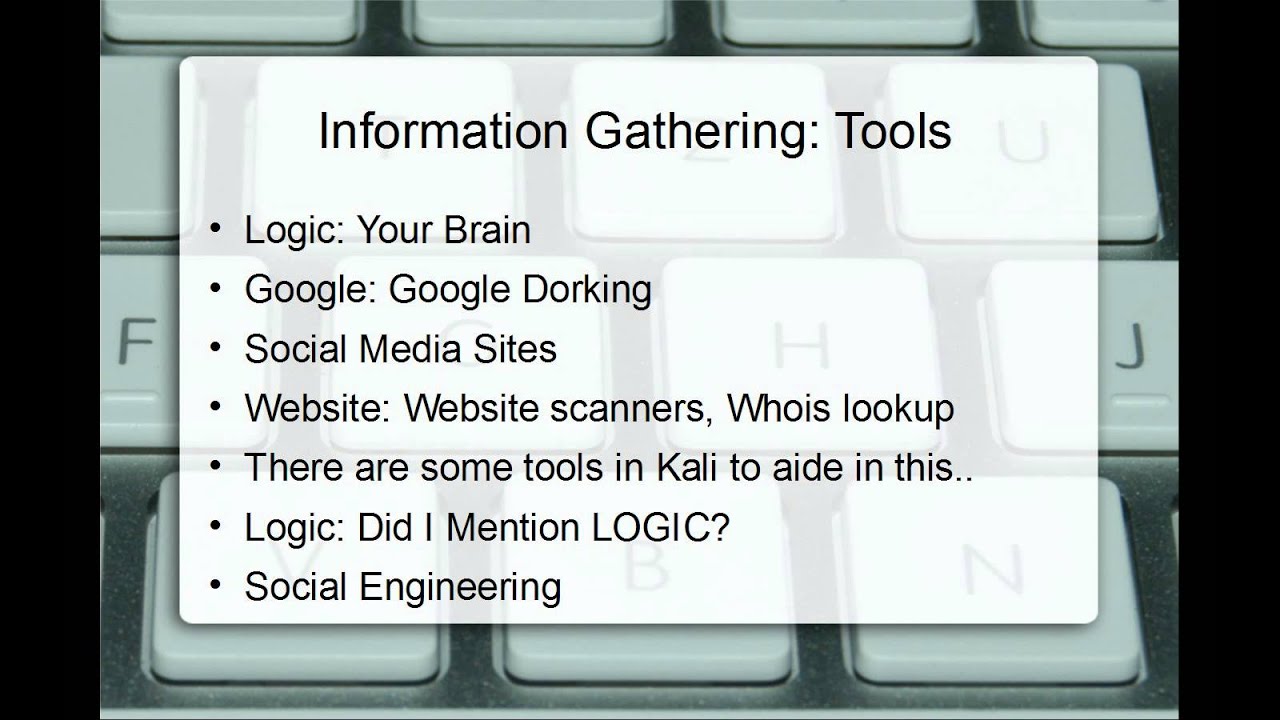
Convert Text to Speech Hey guys, in this video we enter in part 3 of the video series, the Recon
June 20th, 2013 | 🕒
https://www.ispeech.org This Video talks about the Correct Phases and Flow of a Professional Network Security Audit / Penetration Test. This
June 8th, 2013 | 🕒
Text to Speech Cross-site scripting (XSS) is a type of computer security vulnerability typically found in Web applications. XSS enables
March 31st, 2013 | 🕒
iSpeech made with ezvid, free download at http://ezvid.com How to install Kali-linux on Machine or VM. In later videos I












Gloss