March 15th, 2013 | 🕒
Text to Speech Voices We demonstrate how static code analysis helps find security vulnerabilities in software. Visit us at http://www.softscheck.com/index_en.html
December 5th, 2012 | 🕒
iSpeech.org Title: Static Analysis of Java Class Files for Quickly and Accurately Detecting Web-Language Encoding Methods Abstract Attacks such as
November 23rd, 2012 | 🕒
TTS Title: Using Interactive Static Analysis for Early Detection of Software Vulnerabilities Abstract We present our work of using interactive
September 8th, 2012 | 🕒
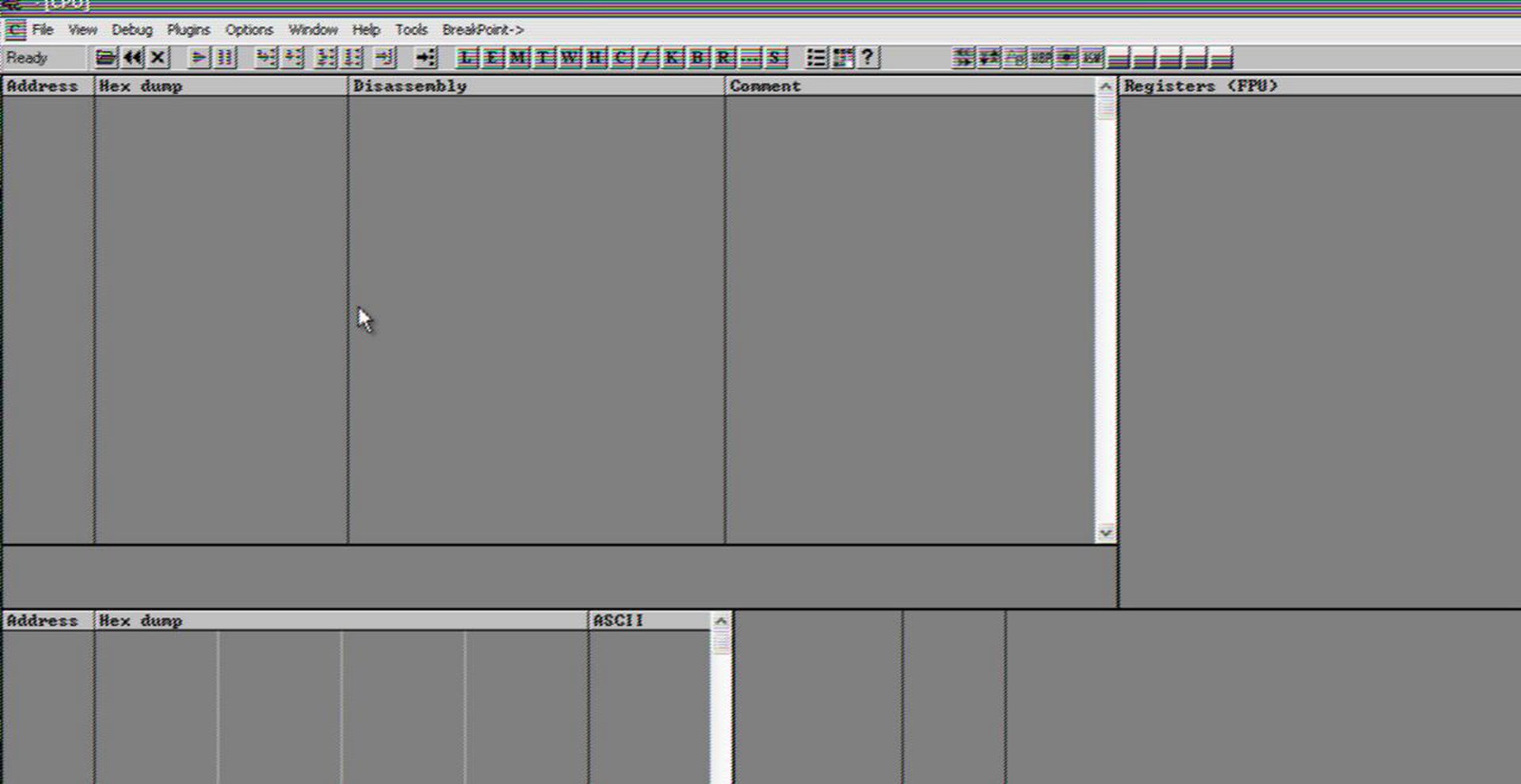
iSpeech This video is the part of our free community project on "Reverse engineering and Malware analysis" training. Training source
September 8th, 2012 | 🕒
iSpeech.org This video is the part of our free community project on "Reverse engineering and Malware analysis" training. Training source
August 26th, 2012 | 🕒
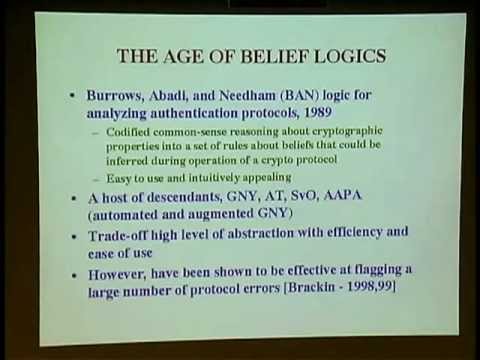
Convert Text to Speech From the CISR video library (http://www.cisr.us) Dr. Matt Bishop, University of California at Davis Vulnerabilities Analysis
August 10th, 2012 | 🕒
iSpeech From the CISR video library (http://www.cisr.us) Sylvan Pinsky introduces Cathy Meadows (NRL) Topic: Cryptographic Protocol Analysis February 9, 2004
July 21st, 2012 | 🕒
iSpeech.org Demo video of Cuckoo Sandbox 0.4 while analyzing a rogue PDF document exploiting a Flash Player vulnerability (CVE-2011-0611). source
July 16th, 2012 | 🕒
iSpeech Welcome to the first TekTip episode from TekDefense.com. In this episode we talk about and demo basic dynamic malware
July 15th, 2012 | 🕒
iSpeech This video is part of the presentation presented at the SecurityXploded meet in Bangalore For more details visit http://securityxploded.com
May 17th, 2012 | 🕒
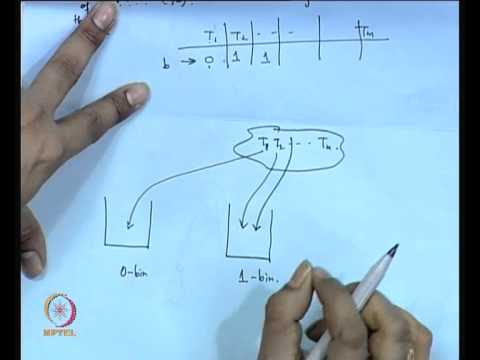
Convert Text to Speech Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur.
May 15th, 2012 | 🕒
iSpeech.org This video is the part of our free community project on "Reverse engineering and Malware analysis" training. Training source
April 16th, 2012 | 🕒
iSpeech.org Abstract: Most important Web application vulnerabilities, such as SQL Injection, Cross Site Scripting and Malicious File Execution, are typically
April 15th, 2012 | 🕒
iSpeech.orgRAFT is a testing tool for the identification of vulnerabilities in web applications.RAFT is a suite of tools that utilize


















Gloss