Session Identifier are for Now, Passwords are Forever – XSS-Based Abuse of Browser Password Managers
iSpeech.org
By Sebastian Lekies and Ben Stock
"Ever since Cross-site Scripting (XSS) was discovered in the year 2000, one of the main goals of an XSS attack was to take over the victim's session, and, thus his authentication context with the vulnerable web application. Consequently, the terms ""XSS"" and ""Session Hijacking"" were used as synonyms for many years. However, the introduction of defensive features, such as HTTPonly Cookies, efficiently prevents the stealing of session IDs and mitigating this class of attacks. However, while session identifiers are protected robustly, another more powerful and much more long-lived authentication credential might not be: The Web user's password.
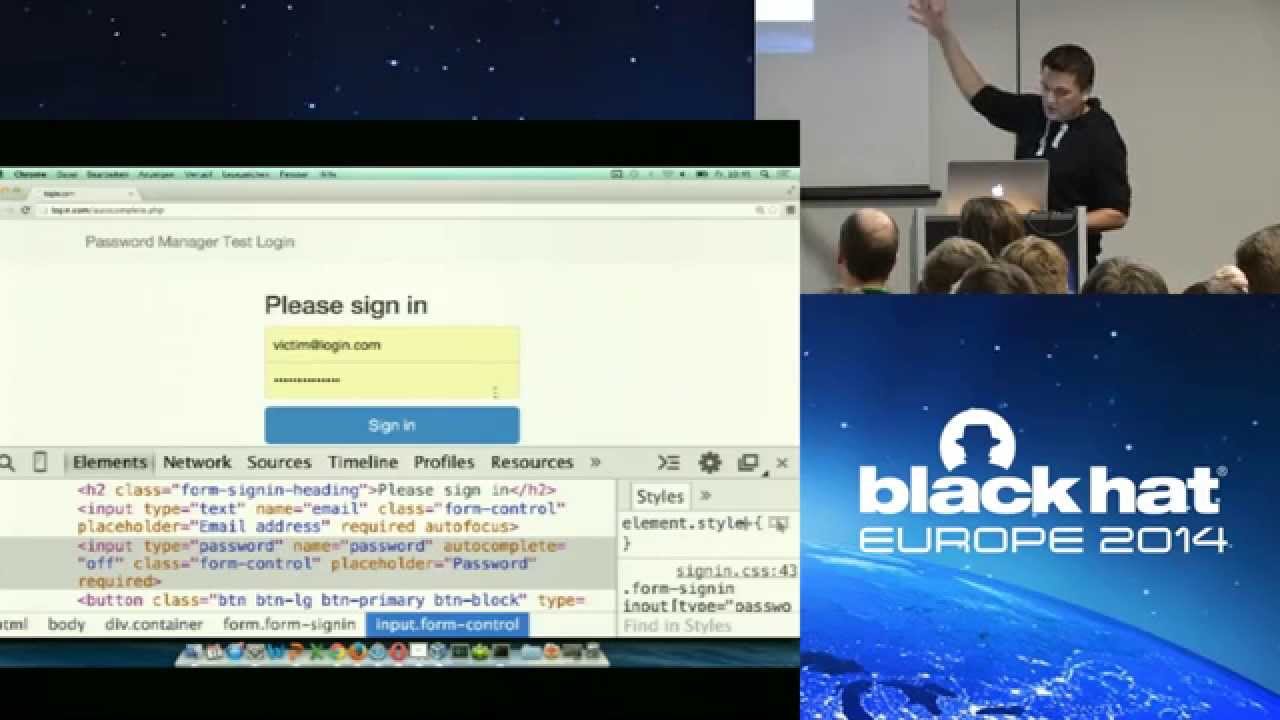
As it turns out, browser-based password managers appear to be the exact tool that attackers need: To ease the burden of repeated password authentication on multiple sites, modern web browsers provide password managers, which offer to automatically complete password fields on web pages, after the password has been stored once. Unfortunately, these managers operate by simply inserting the clear-text password into the document's DOM, where it is accessible by JavaScript.
In consequence, a successful XSS attack can be leveraged by the attacker to read and leak password data which has been provided by the password manager.
In this presentation, we give a comprehensive overview on potential XSS-based attack patterns on browser-provided password managers. In this context, we present two systematic studies:
- For one, we examine the current generation of existing password managers in all (!) major browsers and show their susceptibility to the outlined attacks. We will show in detail how an XSS attack can leak obtain user's password from the manager and leak it to the user.
- Furthermore, we report on a large-scale study on the Alexa Top 4000 site, in which we studied how password fields are used by popular websites.
We will conclude the presentation with a set of recommendations, both for website operators as well as web users, how to protect themselves against the demonstrated attacks."
2015-04-03 17:44:42
source







Gloss