PoC – Exploiting Vulnerabilities in Maian Support for a Complete Take Over
iSpeech
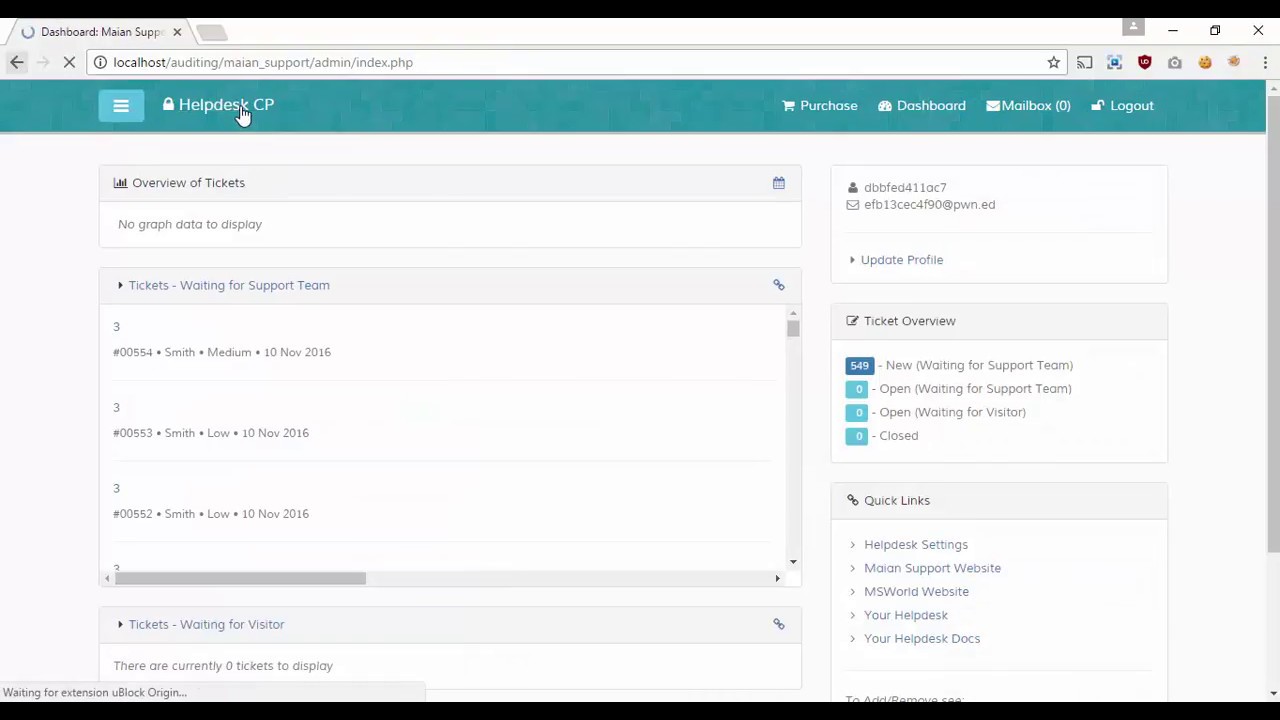
In this Proof of Concept video we show how an attacker uses a script to automate the exploitation of a number of
Missing Function Level Access Control Vulnerabilities (listed in the OWASP Top 10 2013) to gain full access on the Maian Support, a web based support helpdesk system.
The script first tries to create a new admin account, but it fails. So then it identifies an existing admin account and changes the username and password for that account.
It also uploads a php file to the system (as a PoC) and then the attacker is able to login to the system.
For more detailed and technical information about these vulnerabilities and how they can be exploited refer to: https://www.netsparker.com/blog/web-security/missing-function-level-access-control-vulnerability-maian-support-helpdesk/
2017-02-24 15:26:38
source







Gloss