Microsoft on Wednesday revealed that a China-based threat actor known as Storm-0558 acquired the inactive consumer signing key to forging tokens to access Outlook by compromising an engineer's corporate account.
This enabled the adversary to access a debugging environment that contained a crash dump of the consumer signing system that took place in April 2021 and steal the key.
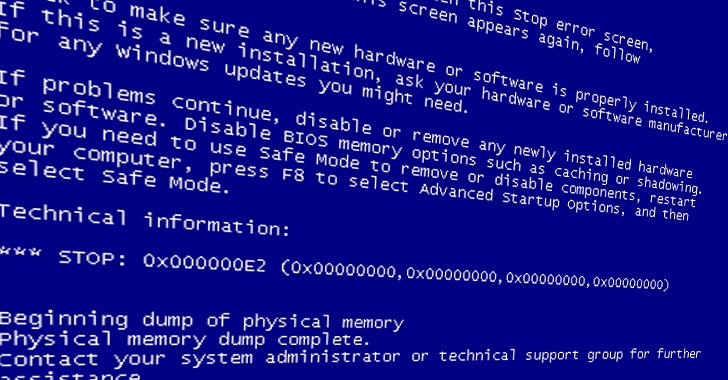
"A consumer signing system crash in April of 2021 resulted in a snapshot of the crashed process ('crash dump')," the Microsoft Security Response Center (MSRC) said in a post-mortem report.
"The crash dumps, which redact sensitive information, should not include the signing key. In this case, a race condition allowed the key to be present in the crash dump. The key material's presence in the crash dump was not detected by our systems."
The Windows maker said the crash dump was moved to a debugging environment on the internet-connected corporate network, from where Storm-0558 is suspected to have acquired the key after infiltrating the engineer's corporate account.

It's not currently not known if this is the exact mechanism that was adopted by the threat actor since Microsoft noted it does not have logs that offer concrete proof of the exfiltration due to its log retention policies.
Microsoft's report further alludes to spear-phishing and the deployment of token-stealing malware, but it did not elaborate on the modus operandi of how the engineer's account was breached in the first place, if other corporate accounts were hacked, and when it became aware of the compromise.
That said, the latest development offers insight into a series of cascading security mishaps that culminated in the signing key ending up in the hands of a skilled actor with a "high degree of technical tradecraft and operational security."
Storm-0558 is the moniker assigned by Microsoft to a hacking group that has been linked to the breach of approximately 25 organizations using the consumer signing key and obtaining unauthorized access to Outlook Web Access (OWA) and Outlook.com.
The zero-day issue was blamed on a validation error that allowed the key to be trusted for signing Azure AD tokens. Evidence shows that the malicious cyber activity commenced a month earlier before it was detected in June 2023.
Way Too Vulnerable: Uncovering the State of the Identity Attack Surface
Achieved MFA? PAM? Service account protection? Find out how well-equipped your organization truly is against identity threats
This, in turn, was made possible because the "mail system would accept a request for enterprise email using a security token signed with the consumer key." The "issue" has since been rectified by Microsoft.
Cloud security firm Wiz subsequently revealed in July that the compromised Microsoft consumer signing key could have enabled widespread access to other cloud services.
Microsoft, however, said it found no additional evidence of unauthorized access to applications outside of email inboxes. It has also expanded access to security logging following criticism that the feature was limited to customers with Purview Audit (Premium) licenses, thereby restricting forensics data to others.







Gloss