Meterpreter Paranoid Mode – Meterpreter over SSL/TLS connections
Exploitation:
Payloads available:
Staged (payload.bat|ps1|txt|exe):
windows/meterpreter/reverse_winhttps
windows/meterpreter/reverse_https
windows/x64/meterpreter/reverse_https
Stageless (binary.exe):
windows/meterpreter_reverse_https
windows/x64/meterpreter_reverse_httpsDependencies
- xterm
- zenity
- metasploit
- postgresql
Limitations:
- This tool will NOT evade AV detection, its made to prevent the data beeing transmited from client (payload) to server beeing captured (Eavesdropping)
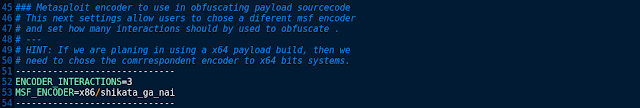
- If you decided to use a 64bit payload, then edit settings file and change 'MSF_ENCODER=x86/shikata_ga_nai' to one payload arch compatible encoder(64bit)
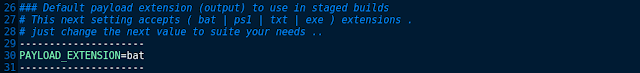
- Only in 'staged' builds, Users are allowed to chose the extension (bat|ps1|txt|exe)
Config Settings file (warning: case sensitive)
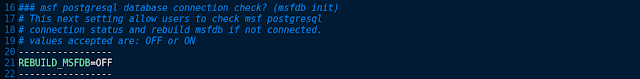
msf postgresql database connection check? (msfdb reinit)
Default payload extension (output) to use in staged builds
Input agent (output) name manually
Metasploit encoder to use in obfuscating payload sourcecode
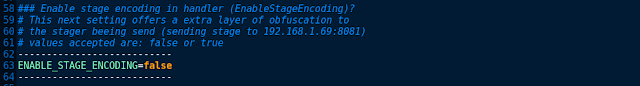
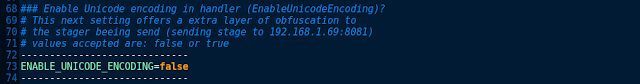
This tool will also encode the 'stage' beeing send (sending stage to 192.168.1.69:666 ..)
using the encoder + unicode_encoder sellected on settings file (default: x86/shikata_ga_nai)
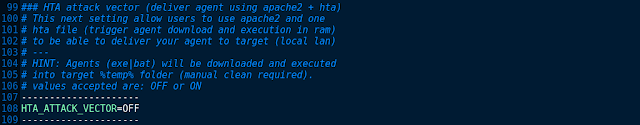
HTA attack vector (deliver agent in local lan using apache2)
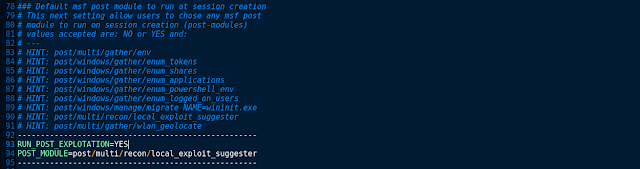
Default msf post module to run at session creation
Download/Install/Config:
1° - Download framework from github
git clone https://github.com/r00t-3xp10it/Meterpreter_Paranoid_Mode-SSL.git
2° - Set files execution permitions
cd Meterpreter_Paranoid_Mode-SSL
sudo chmod +x *.sh
[adsense size='1' ]
3° - Config tool settings
nano settings
4° - Run main tool
sudo ./Meterpreter_Paranoid_Mode.shVideo tutorials:
MPM [ Stageless payload - exe ]
MPM [ Staged payload - bat ]
MPM [ Stageless payload -exe - set encoder and post-module ]
[adsense size='1' ]
MPM [ Staged payload - ps1 - HTA attack vector ]










Gloss