EmbedInHTML – Embed and hide any file in an HTML file
- An python script which generates the output HTML file based on a template, using RC4 encryption routines, and embedding the decryption key within the output file. The resulting HTML can either be browsed by the targeted user or sent as an attachement.
- An HTML/Javascript that you can drag the file into be encrypted to, which generates the output HTML file, using the WebCrypto API, but NOT embedding the decryption material (key and counter). Instead, the decryption material is displayed as a set of URL parameters to be added into a URL pointing to the HTML resulting file:
http(s)://hosting.server.com/result.html#hexencodedkey!hexencodedcounter. So the resulting HTML file cannot be sent as an attachment. The main advantage of this technique is that the decryption material is not embedded into the file itself, hence preventing analysis and even retrieval of the payload by any system which doesn't have the full URL (eg: intercepting proxy)
- This tool was inspired and derived from the great 'demiguise' tool : https://github.com/nccgroup/demiguise
- The b64AndRC4 function used on the binary input (from the XLL file) is a mix of:https://gist.github.com/borismus/1032746 and https://gist.github.com/farhadi/2185197
- Check https://gist.github.com/Arno0x/f71a9db515ddea686ccdd77666bebbaa for an easy malicious XLL creation which is a perfect example of a malicious document one could try to deliver with this method.
- In the HTML template (html.tpl file) it is advised to insert your own key environmental derivation function below in place of the 'keyFunction'. You should derive your key from the environment so that it only works on your intended target (and not in a sandbox).
Usage
Few payload examples files are provided in the payloads_examples directory. For instance the
calc.xll is an Excel add-in (XLL) file that contains a metasploit shellcode for x86 processes to launch the calc.exe process.
Using the python script
1/ Generate the malicious html file from the XLL file, along with a secret key:
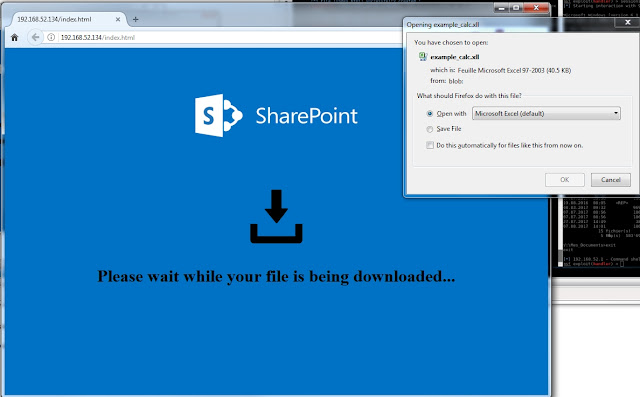
python embedInHTML.py -k mysecretkey -f example_calc.xll -o index.html2/ Expose the html file on a web server (one can be optionnaly started for you with the-w flag)
Using the HTML/Javascript
1/ Open the embedInHTML.html file within a browser
2/ Simply drag the payload file into the page (you can optionnaly change the output file name)
3/ Save the resulting file and take note of the decryption material as URL parameters to be added to the file name in the form:
http(s)://hosting.server.com/result.html#hexencodedkey!hexencodedcounter[adsense size='1' ]
Eventually...
Point the target's browser to the html file and let the magic happen:








Gloss