March 11th, 2019 | 🕒
iSpeechA new mega data leak made the headlines, an unprotected MongoDB database (150GB) belonging to a marketing company exposed up
March 11th, 2019 | 🕒
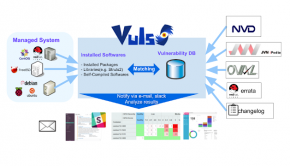
https://www.ispeech.org/text.to.speechVulnerability scanner for Linux/FreeBSD, agentless, written in golang. Twitter: @vuls_en adsense size='1'] DEMO adsense size='1'] Abstract For a system administrator,
March 10th, 2019 | 🕒
iSpeechCat-Nip Automated Basic Pentest Tool this tool will make your basic pentesting task like Information Gathering, Auditing, And Reporting so this tool will do every task
March 10th, 2019 | 🕒
iSpeechThe malicious code targets both Windows and Linux systems, compromised systems are used to carry out brute force attacks along
March 9th, 2019 | 🕒
iSpeech.orgThe theme at the ongoing RSA 2019 conference is “Better”. As the official RSA page explains, “This means working hard to find
March 9th, 2019 | 🕒
https://www.ispeech.org Goca is a FOCA fork written in Go, which is a tool used mainly to find metadata and hidden information in the documents its
March 8th, 2019 | 🕒
iSpeech.org Turbinia is an open-source framework for deploying, managing, and running distributed forensic workloads. It is intended to automate running of common forensic
March 8th, 2019 | 🕒
Speech SynthesisA scripted pipeline of tools to simplify the bug bounty/penetration test reconnaissance phase, so you can focus on chomping bugs Scope
March 8th, 2019 | 🕒
https://www.ispeech.org The NSA released the Ghidra, a multi-platform reverse engineering framework that could be used to find vulnerabilities and security holes in applications.
March 7th, 2019 | 🕒
text to speech Legion, a fork of SECFORCE's Sparta, is an open source, easy-to-use, super-extensible and semi-automated network penetration testing framework that
March 5th, 2019 | 🕒
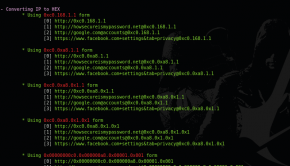
https://www.ispeech.org/text.to.speech IP obfuscator made to make a malicious ip a bit cuter A simple python tool to help you to
March 5th, 2019 | 🕒
iSpeech.orgAutomate discovering and dropping payloads on LAN Raspberry Pi's via ssh. rpi-hunter is useful when there are multiple Raspberry Pi's on your LAN
March 4th, 2019 | 🕒
iSpeech.org XNU suffers from a copy-on-write behavior bypass via mount of user-owned filesystem image. MD5 | babb0ad99959bd04e0f28e89ee861d68 Download Source: packetstormsecurity.com
March 4th, 2019 | 🕒
iSpeechWhat is a CMS? A content management system (CMS) manages the creation and modification of digital content. It typically supports multiple users

















Gloss