February 18th, 2023 | 🕒
iSpeech.org ====================================================================================================================================| # Title : Argon Dashboard - v1.1.2 Auth By Pass Vulnerability || # Author : indoushka || #
February 18th, 2023 | 🕒
iSpeech The concept of privacy-by-design was actually devised almost 30 years ago by Ann Cavoukian, PhD, former Ontario Information and
February 18th, 2023 | 🕒
iSpeech.org Matt Atkinson | 27 May 2021 at 15:30 UTC As we mentioned in our recent blog post on good
February 18th, 2023 | 🕒
iSpeech I love VMware (used it since its first releases) and I love it even more now 😄. Yesterday I
February 18th, 2023 | 🕒
https://www.ispeech.org/text.to.speech Users have long needed to access important resources such as virtual private networks (VPNs), web applications, and mail servers
February 18th, 2023 | 🕒
iSpeech -----BEGIN PGP SIGNED MESSAGE-----Hash: SHA256 - -------------------------------------------------------------------------Debian Security Advisory DSA-5351-1 security@debian.orghttps://www.debian.org/security/ Alberto GarciaFebruary 17, 2023 https://www.debian.org/security/faq- ------------------------------------------------------------------------- Package :
February 18th, 2023 | 🕒
tts Where to find them. How to keep them. Alternatives to hiring. While part of the solution to a
February 18th, 2023 | 🕒
Text to Speech Voices Build SBOMs, Upgrade (or Remove) Everything Another major exploit made headlines over the holidays when attackers
February 18th, 2023 | 🕒
iSpeech Emma Stocks | 02 June 2021 at 11:23 UTC The Burp Suite user community can easily be described as
February 18th, 2023 | 🕒
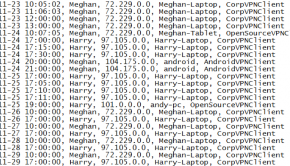
https://www.ispeech.org Just look at this: I just got Little Snitch to keep working even with network filter being off (that
February 18th, 2023 | 🕒
iSpeech.org Introduction Through FireEye Dynamic Threat Intelligence (DTI), we observed RIG Exploit Kit (EK) delivering a dropper that leverages the
February 18th, 2023 | 🕒
https://www.ispeech.org/text.to.speech On June 4, 2018, Optiv gTIC Human Intelligence (HUMINT) cell contacted an India-based individual providing interview-proxy services for job
February 18th, 2023 | 🕒
iSpeech As a Chief Information Security Officer (CISO) or cybersecurity leader, one of the most important parts of your role
February 18th, 2023 | 🕒
french text to speech In this episode we are going to review Control Groups (cgroups), which provide a mechanism for















Gloss