February 6th, 2017 | 🕒
iSpeech 4SICS Forum presentations at the 3rd International Summit for Security in Industrial Control Systems, Stockholm, Sweden, 25–27 October 2016.
February 6th, 2017 | 🕒
iSpeech.org If I got 50liks from everyone our team will post more thank Sqlmap | SQL Injection High Level Tutorial
February 6th, 2017 | 🕒
Powered by iSpeechAs the internet evolves and computer networks become bigger and bigger, network security has become one of the
February 6th, 2017 | 🕒
iSpeech.org http://www.privshell.com Komutlar: Durdurmak için CTRL + C kullanabilirsiniz veya Terminali kapatırsanız duracaktir. cd Downloads ls unzip + indirilen arsiv
February 6th, 2017 | 🕒
Text to Speech Demo Want to know how to exploit a common cryptographic flaw or forge administrator cookies, recover passwords?
February 6th, 2017 | 🕒
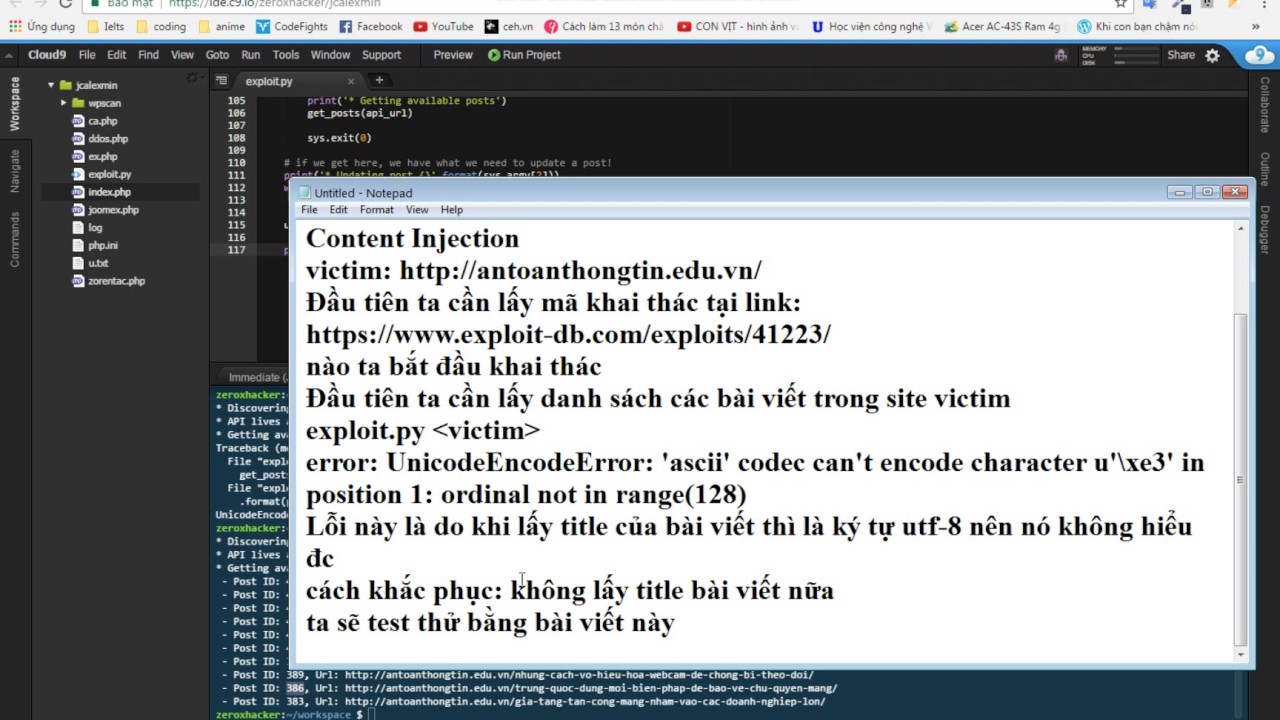
TTS WordPress 4.7.0/4.7.1 Unauthenticated Content Injection Exploit code: https://www.exploit-db.com/exploits/41223/ Steps: Download exploit code Run exploit code with command: python exploit.py
February 6th, 2017 | 🕒
Convert Text to Speech OWASP - WebGoat 7 - Injection Flaws - Blind Numeric SQL Injection 2017-02-06 03:25:14 source













Gloss