
Monthly Archives: January 2013
Firefox & the 'plugin has security vulnerabilities' alert
January 20th, 2013 | 🕒
https://www.ispeech.org This tutorial describes how to proceed past the "This plugin has security vulnerabilities" alert in the latest version of
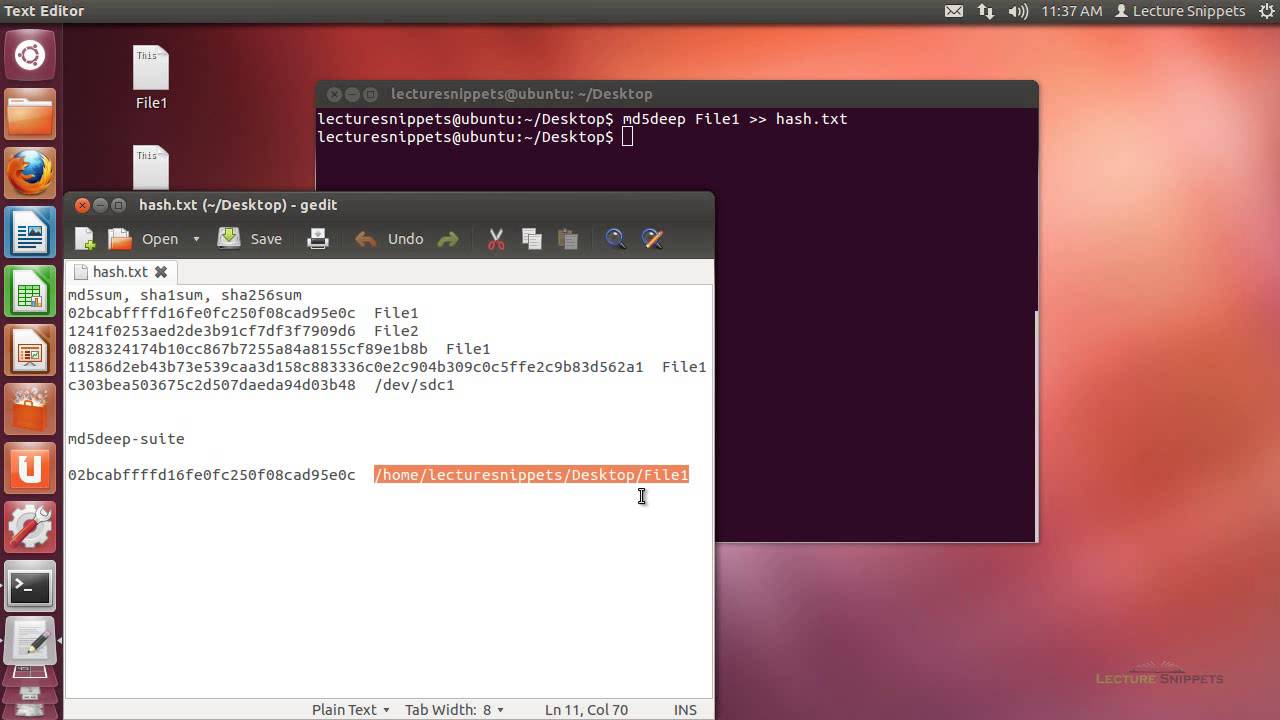
Ubuntu 12.04 Forensics – md5deep, sha1deep, sha256deep, tigerdeep, and whirlpooldeep
January 20th, 2013 | 🕒
https://www.ispeech.org This video is part of a series on Computer Forensics using Ubuntu 12.04. In this Lecture Snippet I use
Ubuntu 12.04 Forensics – md5sum, sha1sum, and sha256sum
January 20th, 2013 | 🕒
Text to Speech Demo This video is part of a series on Computer Forensics using Ubuntu 12.04. In this Lecture
SAE Institute Cape Town – 3D Modeling Reel – 2013
January 19th, 2013 | 🕒
iSpeech.org Character and Environment modeling, texturing and lighting from my 1 year at SAE Institute Cape Town for the Higher
BackTrack Reborn – Kali Linux Teaser
January 19th, 2013 | 🕒
iSpeech BackTrack reborn - Kali Linux Promo movie by Offensive Security. http://www.offensive-security.com Likes: 351 Viewed: source
Apple Software Certifications and the Digital Corps
January 18th, 2013 | 🕒
Powered by iSpeech Software certifications are a key component to success at the Digital Corps. Knowing your creative team is
Invisible Criminal
January 17th, 2013 | 🕒
https://www.ispeech.org/text.to.speech Computer crime film; writer and director; an award winning drama (New York Film & TV Silver) designed to powerfully
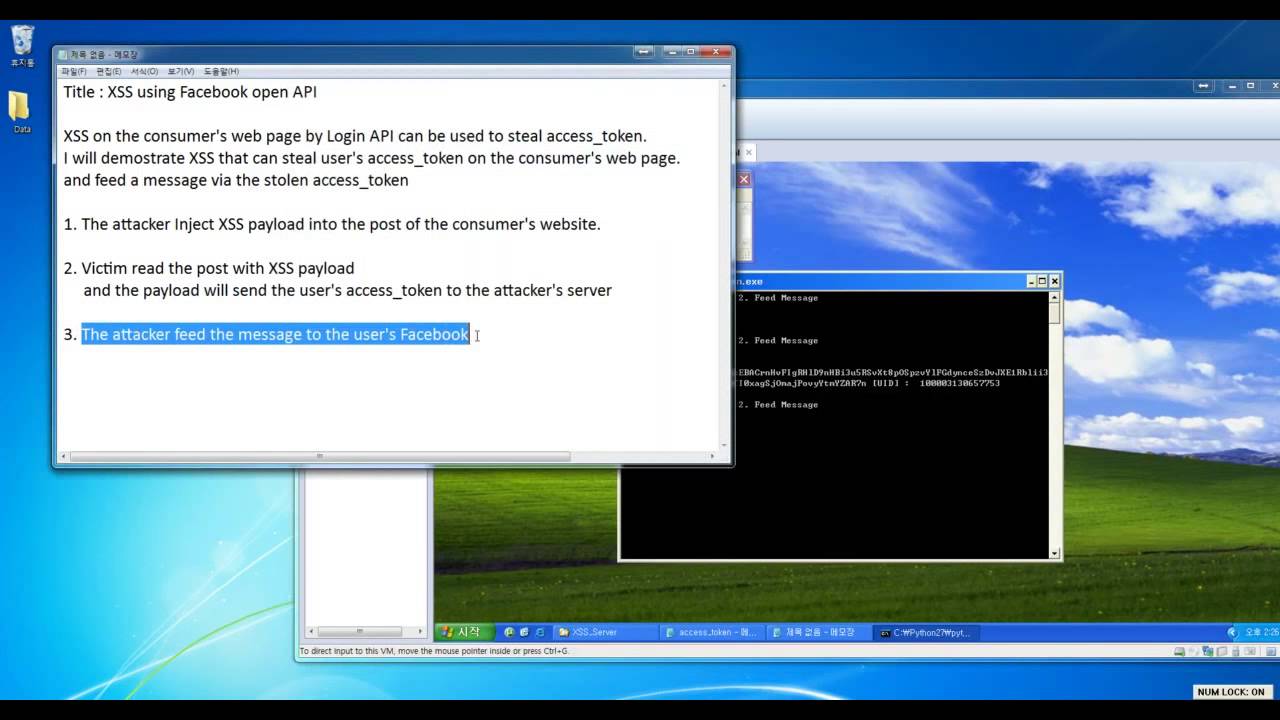
XSS using Facebook open API
January 17th, 2013 | 🕒
iSpeech XSS on the consumer's web page by Login API can be used to steal access_token. I will demonstrate XSS
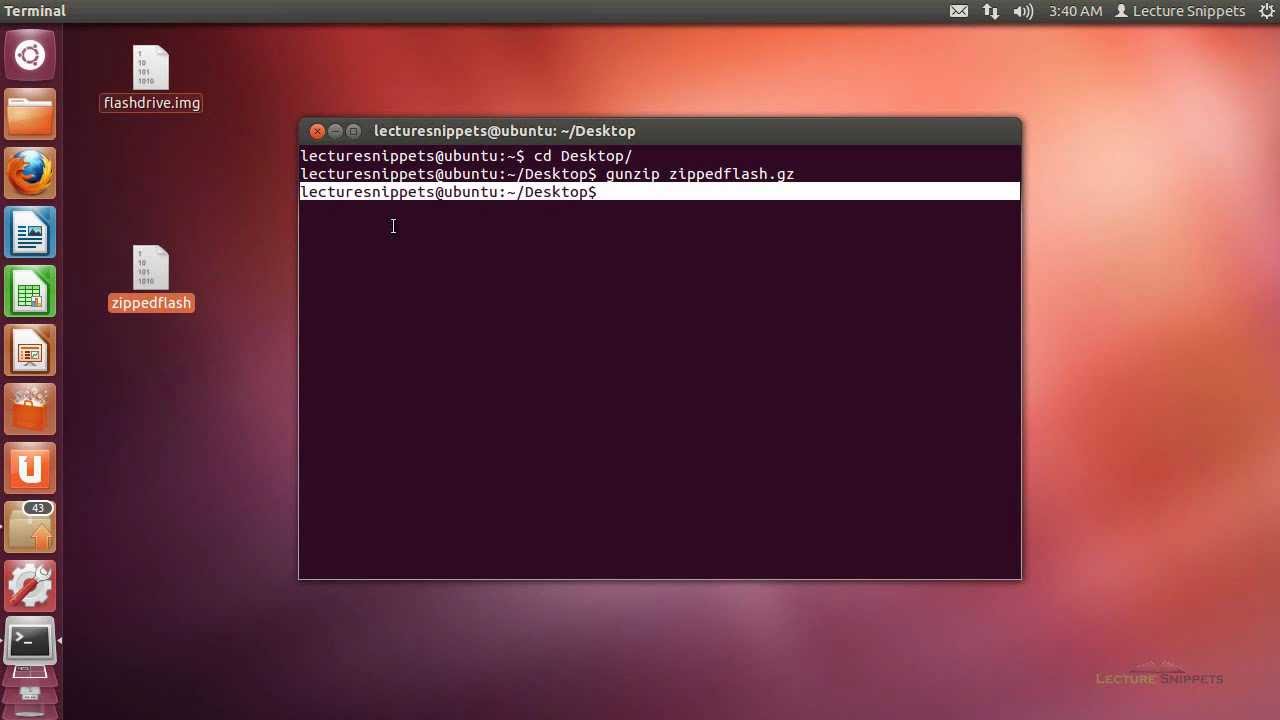
Ubuntu 12.04 Forensics – Disk to Compressed Image Using gzip dc3dd
January 17th, 2013 | 🕒
iSpeech.org This video is part of a series on Computer Forensics using Ubuntu 12.04. In this Lecture Snippet I use
Virtual Drive Secure Cloud Storage Services
January 16th, 2013 | 🕒
https://www.ispeech.org http://VirtualDrive.com ] Virtual Drive provides secure online cloud storage to share large files, upload and transfer files using
[BackTrack 5] SQL Injection Attack
January 16th, 2013 | 🕒
TTS BackTrack 5] SQL Injection Attack Seems like the Video is stopping sometimes. Anyway theese are the codes. Once loaded:
10. Open Addressing, Cryptographic Hashing
January 14th, 2013 | 🕒
https://www.ispeech.org MIT 6.006 Introduction to Algorithms, Fall 2011 View the complete course: http://ocw.mit.edu/6-006F11 Instructor: Srini Devadas License: Creative Commons BY-NC-SA

















Gloss