November 22nd, 2012 | 🕒
iSpeech.org Speaker: CHRISTOPHER SOGHOIAN OPEN SOCIETY FELLOW, OPEN SOCIETY FOUNDATIONS BEN WIZNER DIRECTOR, SPEECH, PRIVACY, & TECHNOLOGY PROJECT, ACLU CATHERINE
November 22nd, 2012 | 🕒
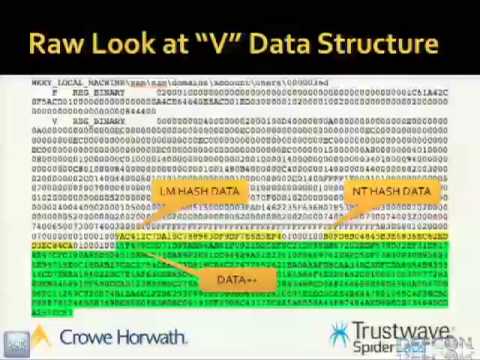
https://www.ispeech.org/text.to.speech Speakers: RYAN REYNOLDS MANAGER, SECURITY AND PRIVACY AT CROWE HORWATH LLP JONATHAN CLAUDIUS SECURITY RESEARCHER, SPIDERLABS RESEARCH, TRUSTWAVE The
November 21st, 2012 | 🕒
iSpeech.org AI vs Players, NATO vs USSR, WWIII-esque stuff, the usual. EDIT- I'd like to make a note here, roughly
November 21st, 2012 | 🕒
iSpeech Speaker: RENDERMAN CHIEF RESEARCHER What happens when a hacker gets bored and starts looking at an aircraft tracking systems?
November 21st, 2012 | 🕒
iSpeech Speaker: PHIL POLSTRA COMPUTER SECURITY PROFESSOR, UNIVERSITY OF DUBUQUE In this talk cheap easily constructed devices which can be
November 21st, 2012 | 🕒
iSpeech.org Speaker: PETER HANNAY SECURITY RESEARCHER, PHD STUDENT Smart phones and other portable devices are increasingly used with Microsoft Exchange
November 20th, 2012 | 🕒
https://www.ispeech.org/text.to.speech David Barton, Principal UHY Advisors, discusses the new OCR Audit Protocols and explains appropriate application for risk assessment against
November 20th, 2012 | 🕒
Text to Speech Speaker: NADEEM DOUBA CYGNOS IT SECURITY Have you ever wished for the power of Maltego when performing
November 20th, 2012 | 🕒
iSpeech.org Learn how attackers are exploiting the top vulnerabilities including attacks on Oracle, IBM DB2, Microsoft SQL Server and Sybase.
November 20th, 2012 | 🕒
https://www.ispeech.org Speakers: MICHAEL ROBINSON CONSULTANT | CHRIS TAYLOR SECURITY RESEARCHER Commercial spyware is available for mobile devices, including iPhones, Android
November 20th, 2012 | 🕒
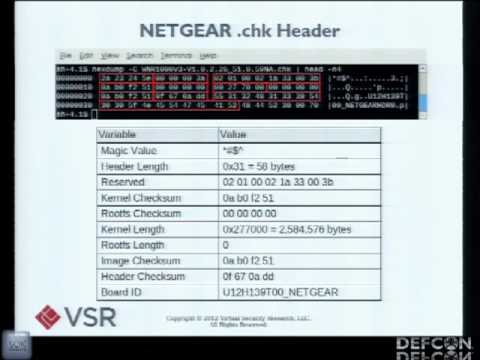
Speech Synthesis Speaker: MICHAEL COPPOLA SECURITY CONSULTANT AT VIRTUAL SECURITY RESEARCH Routers are the blippy switchy boxes that make up
November 20th, 2012 | 🕒
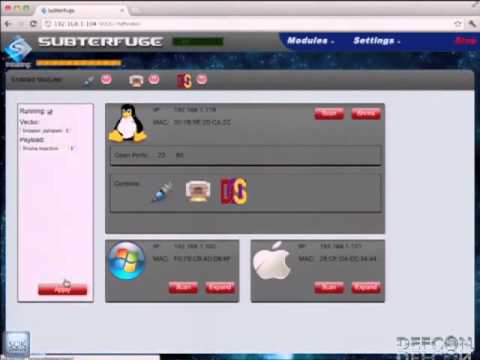
iSpeech Speaker: MATTHEW TOUSSAIN UNITED STATES AIR FORCE CHRISTOPHER SHIELDS UNITED STATES AIR FORCE Walk into Starbucks, plop down a
November 20th, 2012 | 🕒
https://www.ispeech.org Speaker: MARTIN GALLO SECURITY CONSULTANT, CORE SECURITY Nowadays, SAP Netweaver has become the most extensive platform for building enterprise
November 20th, 2012 | 🕒
https://www.ispeech.org/text.to.speech In this tutorial, I will address the use of tautological statements in SQL injection. I will demonstrate how to


















Gloss