May 23rd, 2012 | 🕒
https://www.ispeech.org An overview of Vestige Digital Investigation's Computer & Digital Forensics capabilities, Electronic Discovery (e-Discovery) services and IT Auditing. Based
May 23rd, 2012 | 🕒
TTS Demo Host Suzette Standring welcomes back mystery writer Hallie Ephron who talks about her newest mystery novel, "Come and
May 22nd, 2012 | 🕒
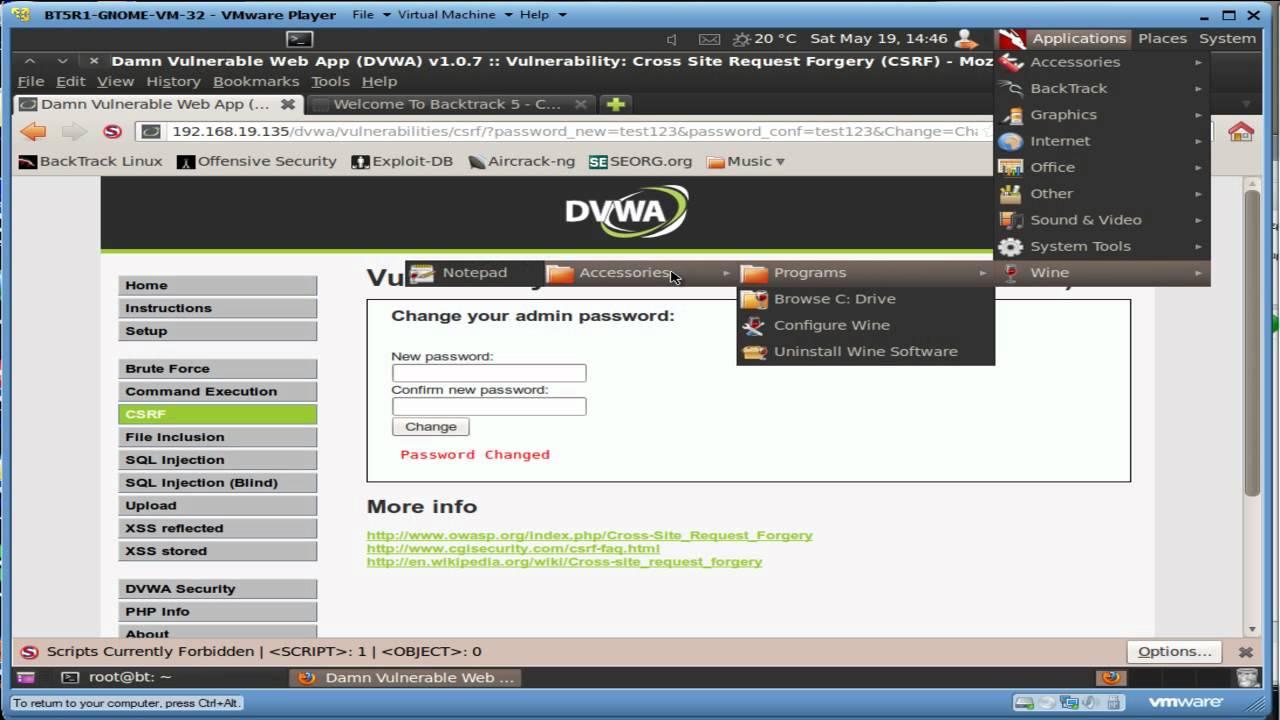
https://www.ispeech.org/text.to.speech We will test a basic Cross Site Request Forgery (XSRF) attack We will capture and manipulate a CSRF URL
May 21st, 2012 | 🕒
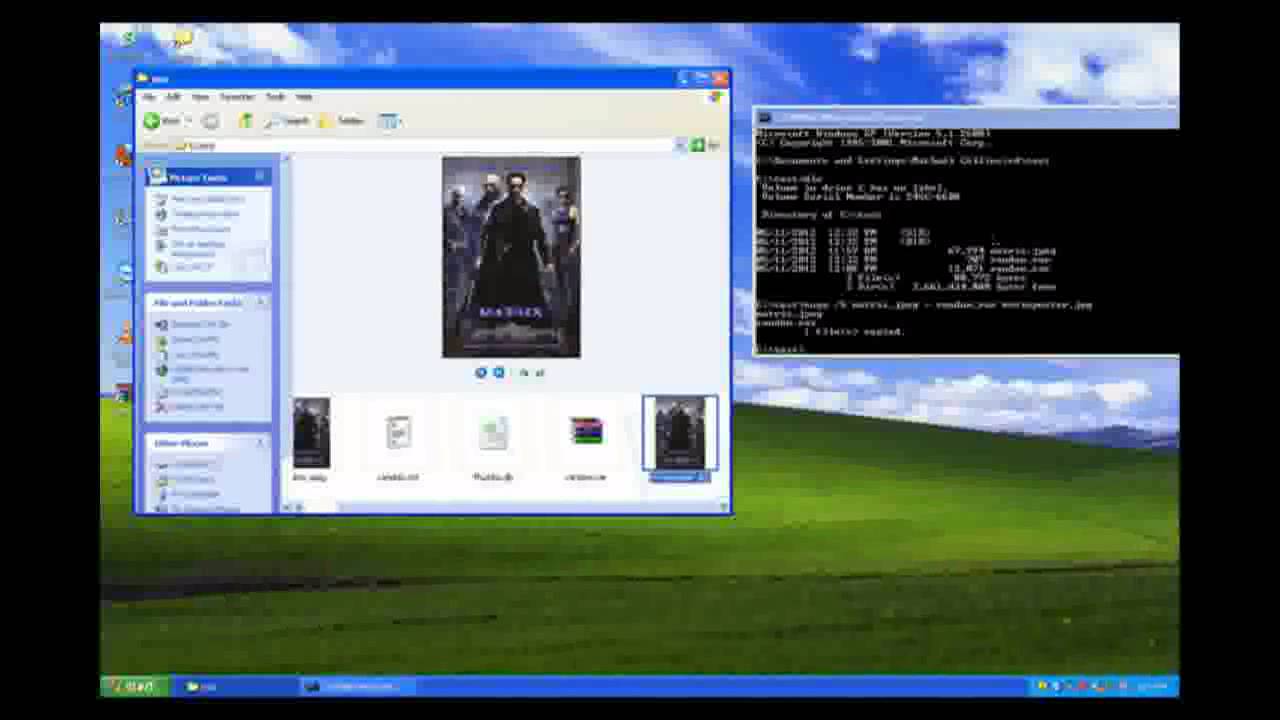
iSpeech MSIA 680 Regis University computer forensics week 1 evidence and incident handling by the Internet Safety for Kids 2012-05-21
May 21st, 2012 | 🕒
iSpeech Ofer Maor CTO of Qutoium, OWASP Leader and Application Security expert with 15 years in the field discusses how
May 21st, 2012 | 🕒
iSpeech.org It finally worked 2012-05-21 16:46:44 source
May 21st, 2012 | 🕒
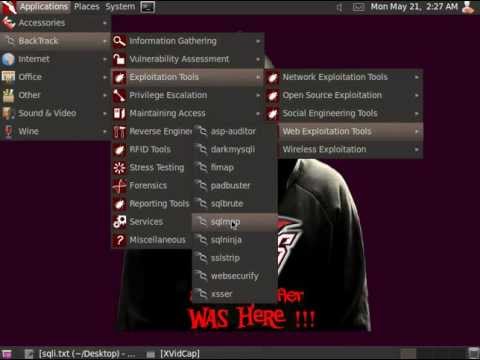
https://www.ispeech.org/text.to.speech The various commands used in this tutorial are: *python.py -u "vuln site link" --dbs *python.py -u "vuln site link"
May 18th, 2012 | 🕒
iSpeech New Album 'Prophet of Doom' available from iTunes http://vmuk.me/dl/hh or Via the New Website http://www.humblehorse.net All video: Illumicorp (A
May 18th, 2012 | 🕒
iSpeech Avi Wigderson is a professor of Mathematics at the Institute for Advanced Study in Princeton. After studying Computer Science
May 17th, 2012 | 🕒
Text to Speech http://www.trainsignal.com/Certified-Ethical-Hacker.aspx?utm_source=YouTube&utm_medium=Social%2BMedia&utm_campaign=CEH -~-~~-~~~-~~-~- This channel is an archive! Subscribe to Pluralsight for new IT Pro training ➨ https://www.youtube.com/user/Pluralsight?sub_confirmation=1
May 17th, 2012 | 🕒
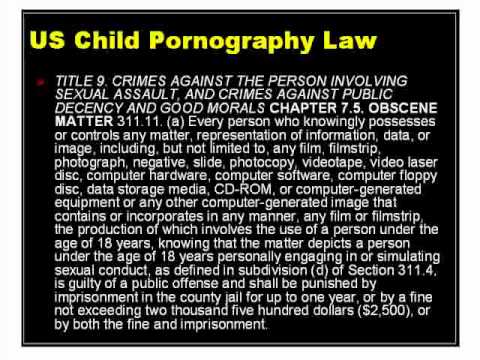
https://www.ispeech.org/text.to.speech http://www.trainsignal.com/Certified-Ethical-Hacker.aspx?utm_source=YouTube&utm_medium=Social%2BMedia&utm_campaign=CEH -~-~~-~~~-~~-~- This channel is an archive! Subscribe to Pluralsight for new IT Pro training ➨ https://www.youtube.com/user/Pluralsight?sub_confirmation=1 -~-~~-~~~-~~-~- 2012-05-17
May 17th, 2012 | 🕒
TTS http://www.trainsignal.com/Certified-Ethical-Hacker.aspx?utm_source=YouTube&utm_medium=Social%2BMedia&utm_campaign=CEH -~-~~-~~~-~~-~- This channel is an archive! Subscribe to Pluralsight for new IT Pro training ➨ https://www.youtube.com/user/Pluralsight?sub_confirmation=1 -~-~~-~~~-~~-~- 2012-05-17
May 17th, 2012 | 🕒
https://www.ispeech.org http://www.trainsignal.com/Certified-Ethical-Hacker.aspx?utm_source=YouTube&utm_medium=Social%2BMedia&utm_campaign=CEH -~-~~-~~~-~~-~- This channel is an archive! Subscribe to Pluralsight for new IT Pro training ➨ https://www.youtube.com/user/Pluralsight?sub_confirmation=1 -~-~~-~~~-~~-~- 2012-05-17
May 17th, 2012 | 🕒
https://www.ispeech.org/text.to.speech Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details















Gloss