The State of Malware and the Banking Trojan
iSpeech.org
It's no secret financial institutions are under constant attack. For online banking services, a banking Trojan is among the most aggressive cyberthreats. With a growing number of criminal crews using banking malware, financial institutions must adapt their security policies to protect their online customers — and their money.
Financial Trojans in 2014: The Good News
In March 2015, security experts at Symantec published a report on the evolution of financial Trojans in 2014. Researchers analyzed nine common banking Trojans between January and December of 2014. They found the number of malicious codes detected decreased significantly over those 12 months — a decline attributed to the numerous operations and arrests conducted by international law enforcement.
[adsense size='1']
Security experts estimate the GameOver Zeus botnet, one of the most long-lived botnets, was made up of a number of infected machines ranging from 500,000 to 1,000,000 units, and it was responsible for the theft of millions of dollars worldwide. In June 2014, the Department of Justice and the FBI announced the success of a multinational effort to disrupt the GameOver Zeus botnet. This and other takedowns operated by law enforcement worldwide contributed to the 53 percent drop in infections during 2014, an encouraging figure accompanied by the concomitant 74 percent decrease in phishing e-mails.
If you take a close look at the family of financial Trojans Symantec analyzed in its report, you'll notice an important decrease in the number of infections for the Zeus Trojan and its variants. In addition, Cridex (W32.Cridex) and SpyEye each decreased by 88 percent and 87 percent from 2012 to 2014, respectively. Some banking malware families such as Shylock nearly disappeared, aiding the diffusion of other variants in the criminal ecosystem.
The Bad News: Cybercrime Still Persists
In spite of the progress made by law enforcement, the study concluded that "Institutions that persist with weaker security measures will continue to be targeted by attackers."
 Almost every banking Trojan implements a "man in the browser" attack, during which attackers are able to inject malicious code directly into victims' browsers, impersonate them and operate their banking accounts. But cybercriminals are using banking Trojans in more complex ways than ever before. The last variants detected in the wild use resilient command, control infrastructures based on Tor and I2P networks, and implement sophisticated evasion techniques.
Almost every banking Trojan implements a "man in the browser" attack, during which attackers are able to inject malicious code directly into victims' browsers, impersonate them and operate their banking accounts. But cybercriminals are using banking Trojans in more complex ways than ever before. The last variants detected in the wild use resilient command, control infrastructures based on Tor and I2P networks, and implement sophisticated evasion techniques.
It's worth mentioning that the diffusion of such malware is enabled by mobile and social networking platforms. Cybercriminals are targeting these new paradigms to reach broader bases of banking customers.
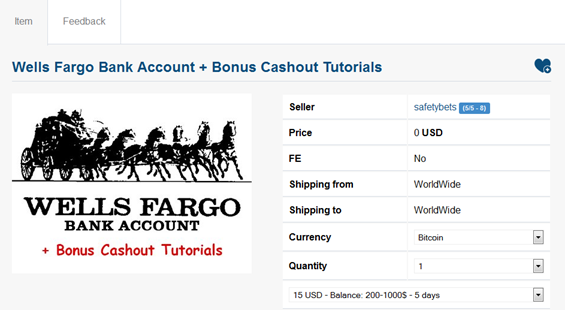
Symantec's study confirms that compromised bank accounts could be used by criminals to directly monetize their efforts through theft; alternatively, criminal crews could offer account info in the criminal underground. The cost of compromised bank account information in the underground market varies: Several marketplaces offer compromised accounts for 5 to 10 percent of their balance values, while other sellers offer them at a price dependent upon several factors, including the bank and any insurance of their validity. According to Symantec, as long as it is luractive to attack weaker intitutions, criminals will continue to perfect and automate their attack techniques.
Adapting to the Banking Trojan Threat Landscape
The experts at Symantec suggest adopting strong authentication mechanisms to improve bank account security. While effective, these measures won't completely secure banking accounts, due to the existence of malware that eludes these mechanisms (by infecting a victim's mobile device, for example). In order to reduce the risk of infection, financial institutions must also improve their security postures.
[adsense size='1']
To achieve enhanced security, financial institutions must adapt their security policies to improve the level of security for online transactions. As Gartner analysts Rob McMillan and Jay Heiser explain, using best practices when writing and adopting a security policy can make a big difference in its ability to reduce risk.
Security policies must be written with a deep knowledge of the cyberthreat landscape, and they must be contextualized to the level of security requested for the organization. In specific cases, a policy must address every technical and functional aspect of an online service. Malware authors constantly search for holes in security chains, and for this very reason it's important to compose a flexible and efficient policy.
Make no mistake: Cybercrime is on the rise, and it will continue to intensify as new malware is developed and spread. To learn more about developing effective AppSec policies, check out Veracode's extensive pool of resources.








Gloss