March 21st, 2024 | 🕒
Powered by iSpeech In today's digital-first business environment dominated by SaaS applications, organizations increasingly depend on third-party vendors for essential
May 23rd, 2023 | 🕒
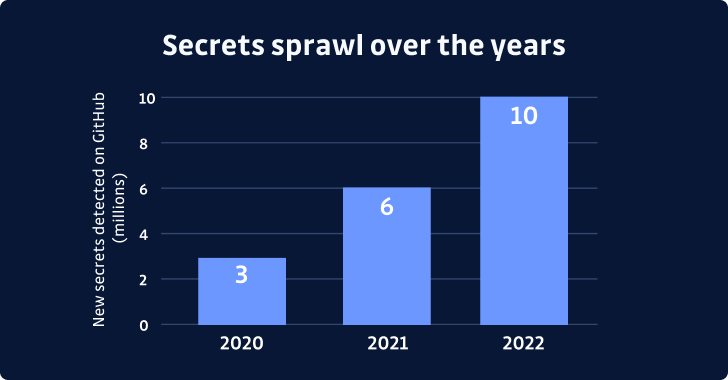
iSpeech.org May 23, 2023The Hacker NewsApplication Security The most precious asset in today's information age is the secret safeguarded under
September 8th, 2022 | 🕒
iSpeech Thomas Barwick By Christopher Gannatti, CFA We know we have a diverse array of readers: Individual business owners Employees
August 17th, 2022 | 🕒
Text to Speech The Great Resignation is adding strain on the already tight security industry labor shortage. In turn, it’s
August 10th, 2022 | 🕒
iSpeech.org Article by One Identity APJ technical director Serkan Cetin. Most cyberattacks are caused by a common vulnerability – compromised credentials.
February 28th, 2022 | 🕒
https://www.ispeech.org/text.to.speech For many in the region, the digital revolution has meant prosperity. Even when Covid-19 struck, the cloud and cloud
November 23rd, 2021 | 🕒
https://www.ispeech.org Accumulating multiple cybersecurity solutions from different vendors can cause massive inefficiencies and unnecessary costs. Vendor sprawl, or the accumulation
October 13th, 2021 | 🕒
TTS DALLAS, Oct. 12, 2021 /PRNewswire/ -- Trend Micro Incorporated (TYO: 4704; TSE: 4704), a global cybersecurity leader, today revealed that global organizations
October 12th, 2021 | 🕒
https://www.ispeech.org/text.to.speech The global independent research* uncovered serious challenges facing SOC teams tasked with detecting and responding to emerging cyber threats.
July 15th, 2021 | 🕒
Text to Speech Thank you to all who joined our recent webinar, “Tool Sprawl – The Trillion Dollar Problem in
October 20th, 2020 | 🕒
iSpeech ReliaQuest, a leader in enterprise security, released the findings of the 2019 ReliaQuest Security Technology Sprawl Report, which reveals
April 29th, 2020 | 🕒
iSpeech.org Almost every network these days will have one or more scanning tools designed to look for everything from malware
March 15th, 2020 | 🕒
Text to Speech Twenty years ago, when enterprise information security was starting to hit its stride, nearly all enterprise security


















Gloss