March 4th, 2024 | 🕒
https://www.ispeech.org/text.to.speech Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive
March 4th, 2024 | 🕒
https://www.ispeech.org Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive
December 6th, 2023 | 🕒
https://www.ispeech.org/text.to.speech In an increasingly complex and fast-paced digital landscape, organizations strive to protect themselves from various security threats. However, limited
October 24th, 2023 | 🕒
Convert Text to Speech ### This module requires Metasploit: https://metasploit.com/download# Current source: https://github.com/rapid7/metasploit-framework## require 'net/ssh'require 'net/ssh/command_stream' class MetasploitModule < Msf::Exploit::Remoteinclude
September 30th, 2023 | 🕒
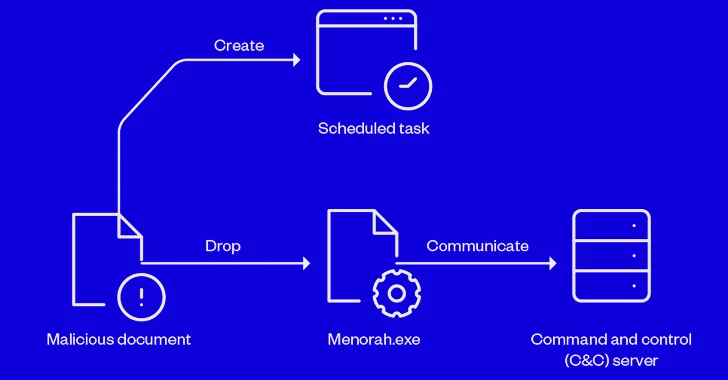
Speech Synthesis Sep 30, 2023THNCyber Espionage / Malware Sophisticated cyber actors backed by Iran known as OilRig have been linked
September 2nd, 2023 | 🕒
https://www.ispeech.orgVMWare Aria Operations for Networks (vRealize Network Insight) static SSH key remote code execution proof of concept exploit. Source link
August 31st, 2023 | 🕒
iSpeech.org Aug 31, 2023THNMalware / Cyber Threat An open-source .NET-based information stealer malware dubbed SapphireStealer is being used by multiple
August 30th, 2023 | 🕒
iSpeech Aug 30, 2023THNVulnerability / Network Security VMware has released software updates to correct two security vulnerabilities in Aria Operations
July 26th, 2023 | 🕒
iSpeech.org ### This module requires Metasploit: https://metasploit.com/download# Current source: https://github.com/rapid7/metasploit-framework## class MetasploitModule < Msf::Exploit::RemoteRank = ExcellentRanking include Msf::Exploit::Remote::HttpClientinclude Msf::Exploit::CmdStagerprepend Msf::Exploit::Remote::AutoCheck
May 22nd, 2023 | 🕒
TTSA financially motivated threat actor of Indonesian origin has been observed leveraging Amazon Web Services (AWS) Elastic Compute Cloud (EC2)
February 28th, 2023 | 🕒
iSpeech There has been a steady stream of work from home (WFH) guidance (including our posts and checklists) published
February 27th, 2023 | 🕒
Speech Synthesis Security professionals cite emerging technologies such as artificial intelligence, advanced analytics and machine learning as key to staying
February 26th, 2023 | 🕒
iSpeech Executive Summary Optiv’s Global Threat Intelligence Center (gTIC) is distributing this advisory as an update to our previous report
February 26th, 2023 | 🕒
iSpeech Updated 2/22/2022 advisory available. See the latest here. Executive Summary In mid-January, a destructive malware campaign targeted several
















Gloss