April 11th, 2024 | 🕒
german tts import requestsimport argparseimport zipfileimport osimport sys RED = '\03391m'GREEN = '\03392m'YELLOW = '\03393m'RESET = '\0330m'ORANGE = '\03338;5;208m' MALICIOUS_PAYLOAD
October 16th, 2023 | 🕒
Text to Speech Medical students, health care workers, and even physicians are increasingly using mobile apps in greater numbers to
June 30th, 2023 | 🕒
iSpeech ┌┌───────────────────────────────────────────────────────────────────────────────────────┐││ C r a C k E r ┌┘┌┘ T H E C R A C K O F
June 22nd, 2023 | 🕒
https://www.ispeech.org/text.to.speech Jun 22, 2023The Hacker NewsNetwork Security / Machine Learning Why Data Exfiltration Detection is Paramount? The world is witnessing
April 28th, 2023 | 🕒
Free Text to Speech ┌┌───────────────────────────────────────────────────────────────────────────────────────┐││ C r a C k E r ┌┘┌┘ T H E C R A C
February 21st, 2023 | 🕒
TTS Demo In part one of this series, we addressed the challenges of shifting from a reactive to a proactive
February 21st, 2023 | 🕒
iSpeech Machine Learning (ML) is well established in cybersecurity, internet search engines, healthcare diagnostics, supply chain optimization and many other
February 17th, 2023 | 🕒
iSpeech Introduction Machine learning (ML) is playing an increasingly important role in cyber security. Here at FireEye, we employ ML
February 17th, 2023 | 🕒
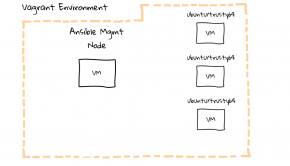
TTS Learning Ansible with Vagrant (Part 2/4) #45 - Learning Ansible with Vagrant (Part 2/4) Links, Code, and Transcript In
February 17th, 2023 | 🕒
Powered by iSpeech Reverse engineers, forensic investigators, and incident responders have an arsenal of tools at their disposal to dissect
February 17th, 2023 | 🕒
iSpeech.org Reverse engineers, forensic investigators, and incident responders have an arsenal of tools at their disposal to dissect malicious software
February 17th, 2023 | 🕒
iSpeech.org Reverse engineers, forensic investigators, and incident responders have an arsenal of tools at their disposal to dissect malicious software
February 17th, 2023 | 🕒
iSpeech Reverse engineers, forensic investigators, and incident responders have an arsenal of tools at their disposal to dissect malicious software
February 17th, 2023 | 🕒
Powered by iSpeech Reverse engineers, forensic investigators, and incident responders have an arsenal of tools at their disposal to dissect













Gloss