Operation Pawn Storm hackers use a iOS spyware
iSpeech.org
By investigating on the cyber espionage campaign dubbed Operation Pawn Storm, experts at TrendLabs discovered a spyware designed for iOS devices.
Security experts at TrendLabs have discovered a new espionage iOS app while they were investigating on the cyber espionage campaign dubbed Operation Pawn Storm. In October 2014, security experts at Trend Micro uncovered a cyber espionage operation dubbed Operation Pawn Storm, which was targeting military, government and media entities worldwide. The threat actors behind the operation have been active since at least 2007 and are still running several attacks worldwide.
The researchers have found a poisoned pawn—spyware specifically designed to spy on Apple iOS devices.
“In our continued research on Operation Pawn Storm, we found one interesting poisoned pawn—spyware specifically designed for espionage on iOS devices. While spyware targeting Apple users is highly notable by itself, this particular spyware is also involved in a targeted attack.” states a blog post published by TrendLabs.
[adsense size='1']
The experts linked the “Operation Pawn Storm” to Russian state-sponsored hackers, which increased their activity in concurrently with beginning crisis between Russia and Ukraine.
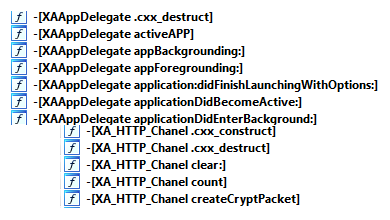
The experts discovered two malicious iOS applications used by hackers behind the Operation Pawn Storm, a first one dubbed XAgent and the other one uses the name of a legitimate iOS game, MadCap. Both apps are samples of the SEDNIT spyware that is used to spy on iOS devices by stealing personal data, acquiring audio from the microphone and making screenshots. The C&C server contacted by the iOS malware is still live according to the malware researchers.
The bad actors behind the Operation Pawn Storm managed spear phishing campaign and targeted Web attacks, which exploited bogus Outlook webmail pages and “typo-squatting” websites. The malicious app infected Apple iOS devices without having to jailbreak them.
“We have seen one instance wherein a lure involving XAgent” states the report.”We have seen one instance wherein a lure involving XAgent simply says “Tap Here to Install the Application.”
The attackers used the “lure” website to serve the malware via Apple’s ad-hoc provisioning feature for developers, the malicious application is provided with a .plist file hosted on the remote server.
[adsense size='1']
Experts also speculated on other methods of infection, including the connection of the IOS devices to a compromised or infected Windows laptop via a USB cable.
According to the researchers, the malicious XAgent app was written for iOS 7, but it is not optimized to hide its presence on iOS 8 devices, the second app MadCap doesn’t work on jailbroken devices.








Gloss