Binwalk 2.0 – easy to use tool for analyzing, reverse engineering, and extracting firmware images
https://www.ispeech.org
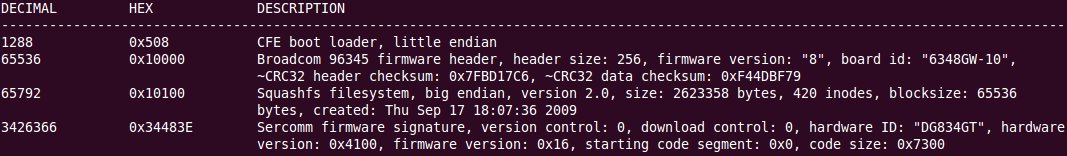
Binwalk is a “firmware analysis tool designed for analyzing, reverse engineering and extracting data contained in firmware images”. This tool written in python supports Linux, and somewhat Mac OS X, can scan firmware files for files signature, and can be useful for hacking firmware files, and finding hidden information.
Let’s install binwalk first. It’s very easy in a Debian or Ubuntu machine, as you just have to download the package, and run a script for installation:
wget https://github.com/devttys0/binwalk/archive/binkwalk-2.0.1.tar.gz tar xzvf binkwalk-2.0.1.tar.gz
cd binkwalk-2.0.1.tar.gz/src sudo ./debian_quick_install.sh
If you have another Linux ditributions, it’s just a little more complicated. You still need to download and extract the release package as above, but you’ll have to install the following package depending on the features your need:
- Minimal installation – python 2.6 or greater, and python-magic
- To generate entropy plot graphs – python-matplotlib
- For automated extraction:
- Packages – mtd-utils zlib1g-dev liblzma-dev gzip bzip2 tar unrar arj p7zip p7zip-full openjdk-6-jdk
- Build and install firmware-mod-kit
Once, this is done, run sudo python ./setup.sh install in src directory to complete the installation.
You can also checkout the latest source code from github:
git clone https://github.com/devttys0/binwalk.git








Gloss